Cybersecurity compliance frameworks are organized sets of policies, controls and processes that help teams manage cyber risk, satisfy regulations, and produce evidence for auditors and customers. In 2026 those frameworks are more important than ever: evolving threats, supply-chain obligations, and sector rules create legal and contractual obligations that affect continuity and trust. This guide breaks down the major standards — what each requires, where they differ, and practical steps security teams can take to prioritize and implement controls. You’ll get a decision framework for choosing standards, a function-level view of NIST CSF 2.0, step-by-step ISO 27001 and SOC 2 guidance, CMMC pathways, and a look at how continuous compliance transforms operational risk management.
Practical checklists, comparison tables, and EAV mappings translate standards into technical artifacts and auditor evidence. After the standards-focused guidance, select sections show how ShieldWatch’s XDR and managed SOC services map to controls and streamline evidence generation.
What Are the Most Important Cybersecurity Compliance Frameworks in 2026?
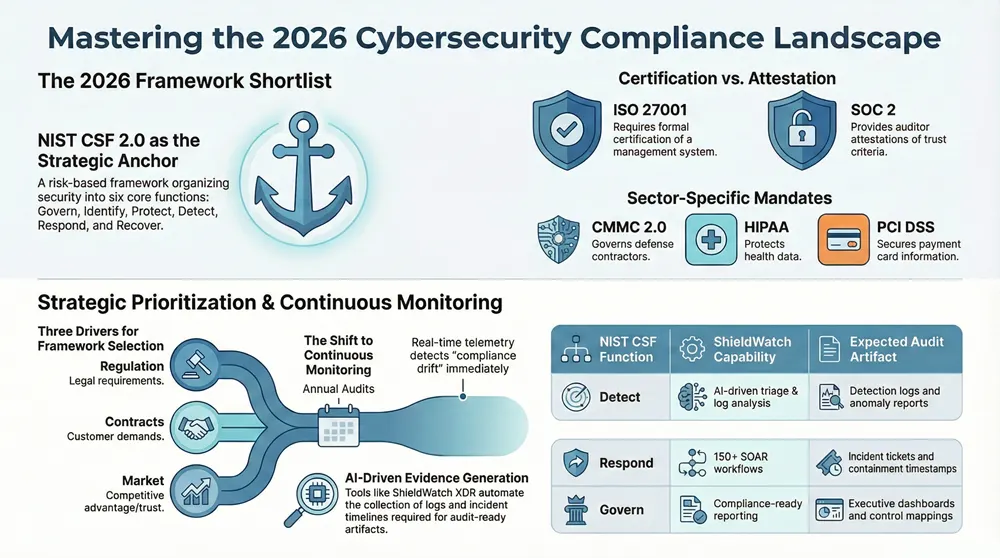
Compliance frameworks define expected security outcomes and offer either prescriptive or risk-based controls to reach them. In 2026 a handful of frameworks drive enterprise and mid-market compliance planning because they align with enforcement priorities, contract terms, or sector-specific risk management. Which frameworks apply depends on industry, data sensitivity, and contractual flow-downs; choosing the right mix reduces duplication and focuses limited resources. The list below summarizes the most relevant standards, their primary focus, and where they typically apply so security leaders can shortlist priorities for remediation and evidence collection.
The major frameworks to consider include:
- NIST CSF 2.0: A risk-based framework that organizes cybersecurity activities into core functions to support enterprise risk management and governance.
- ISO 27001: An auditable certification for an Information Security Management System (ISMS) that prescribes management processes and Annex A controls.
- SOC 2: An attestation against the Trust Services Criteria (security, availability, processing integrity, confidentiality, privacy) commonly used for vendor assurance.
- CMMC 2.0: A U.S. DoD-aligned maturity model that sets assessment requirements for defense contractors and their suppliers.
- HIPAA: Legal requirements protecting health information, with administrative, technical, and physical safeguards.
- PCI DSS: A prescriptive standard for payment card data protection with specific technical controls.
- CIS Controls / GDPR / State Privacy Laws: Complementary frameworks that cover operational controls and privacy obligations.
These frameworks often overlap; mapping common controls reduces audit effort and creates reusable evidence artifacts. The section that follows explains practical decision criteria for prioritizing frameworks.
Which Frameworks Should Businesses Prioritize for Regulatory Adherence?
Prioritization starts with assessing legal exposure, contract requirements, and data sensitivity, then weighing implementation effort and business impact. Begin with a risk assessment that catalogs regulated data, jurisdictional exposure, and any contractual clauses that flow down requirements from customers or partners. That ensures remediation targets the controls that reduce the most business risk and produces audit-ready evidence where it matters. Priorities typically fall into three scenarios — regulation-driven, contract-driven, or market-driven — and a layered roadmap can avoid redundant work.
- Regulation-driven prioritization: Implement frameworks legally required in your sector, such as HIPAA for healthcare or PCI DSS for payment processors.
- Contract-driven prioritization: Meet frameworks your major customers or prime contractors demand — for example, CMMC for DoD suppliers.
- Market-driven prioritization: Pursue certifications or attestations that win business, like ISO 27001 or SOC 2, when customers require vendor assurance.
One practical approach is to adopt a baseline like NIST CSF for enterprise risk structure, then layer ISO or SOC attestations to satisfy certification and market assurance goals. Layering reduces duplicate controls and centralizes evidence collection for multiple audits.
How Do NIST CSF, ISO 27001, SOC 2, CMMC, and HIPAA Differ?
The frameworks differ by purpose, enforcement, and prescriptiveness — distinctions that guide the right compliance pathway. NIST CSF offers flexible, risk-based guidance centered on functions and outcomes; ISO 27001 requires an auditable ISMS and formal certification; SOC 2 delivers an auditor attestation against Trust Services Criteria rather than a certification; CMMC enforces maturity levels for defense contracting through assessments; HIPAA is a regulation with legally enforceable safeguards for protected health information.
- Purpose and scope vary: some standards focus on management systems (ISO 27001), others on control outcomes (NIST CSF), and others carry legal force (HIPAA).
- Certification vs attestation: ISO 27001 yields certification by accredited bodies; SOC 2 provides auditor attestations; CMMC requires formal assessments for DoD work.
- Prescriptive controls vs flexible guidance: PCI DSS and HIPAA include specific technical requirements, while NIST CSF emphasizes risk-informed control selection.
Understanding these differences helps teams combine frameworks strategically — use NIST CSF to drive risk assessment, pursue ISO 27001 for formal certification, and use SOC 2 for customer-facing assurance. The next section explores how NIST CSF 2.0 anchors enterprise risk management.
How Does the NIST Cybersecurity Framework 2.0 Support Enterprise Risk Management?
NIST CSF 2.0 supports enterprise risk management by mapping cybersecurity activities to business objectives and measurable outcomes. Its structure helps prioritize work, tie technical telemetry to executive risk reporting, and build continuous feedback loops for risk treatment decisions. Adopting the core functions plus the Govern component creates artifacts boards and auditors expect — risk registers, control baselines, and performance metrics — which reduce ambiguity when prioritizing remediation.
CSF profiles let organizations set target states, measure current posture, and build prioritized remediation roadmaps. Continuous monitoring feeds those profiles so teams can reassess as threats, business priorities, or regulations change. The section below outlines the core functions and the typical controls auditors expect to see.
What Are the Core Functions and Controls of NIST CSF 2.0?
NIST CSF 2.0 organizes cybersecurity into core functions — Identify, Protect, Detect, Respond, Recover, and Govern — each with control families that map to day-to-day activities and evidence. Identify covers asset inventory and risk assessment; Protect includes access management and encryption; Detect spans logging and anomaly detection; Respond covers incident handling and containment; Recover focuses on continuity and restoration; Govern centers on policy, roles, and risk ownership. Auditors and boards commonly expect artifacts like an asset inventory, risk register, incident response plan, a system-of-record for controls, and regular metrics demonstrating effectiveness.
- Identify: Asset inventory, risk assessment, business impact analysis.
- Protect: Access controls, configuration baselines, encryption, secure development.
- Detect: Logging, SIEM/XDR detections, anomaly detection, alert triage.
- Respond: Playbooks, containment workflows, forensics, stakeholder communication.
- Recover: Backups, recovery plans, restore testing and lessons learned.
- Govern: Policies, roles, compliance mapping, performance reporting.
These functions map to teams — asset owners handle Identify, security operations run Detect and Respond, and risk or compliance teams own Govern — creating clear accountability and measurable KPIs that support enterprise risk management. The section that follows shows how ShieldWatch XDR aligns with these functions.
How Does ShieldWatch XDR Enhance NIST CSF Compliance Through AI and Automation?
ShieldWatch XDR helps meet NIST CSF goals by aligning automated detection, containment and governance telemetry with the CSF functions — producing both operational outcomes and audit-ready artifacts. The platform combines XDR, EDR, SOAR workflows and 24/7 SOC monitoring to deliver continuous detection and fast incident response. Built-in compliance tooling supports SOC 2, HIPAA, CMMC 2.0 and ISO 27001. AI-driven triage and automation reduce alert fatigue, speed mean time to detection and containment, and generate evidence — detection logs, containment timelines and executive dashboards — that auditors and leadership value.
The table below maps NIST CSF functions to ShieldWatch XDR features and the types of compliance evidence produced:
This mapping shows how ShieldWatch translates raw telemetry into structured artifacts aligned with NIST CSF controls, helping teams present concrete evidence of detection, response and governance. Standardized outputs shorten audit cycles and enable continuous compliance monitoring.
What Are the Key Requirements for Achieving ISO 27001 Certification?
ISO 27001 certification requires an organization to create, implement, maintain and continually improve an Information Security Management System (ISMS) that meets the standard’s management system requirements and addresses Annex A controls. Key steps include scoping the ISMS, securing top-management commitment, performing risk assessment and treatment, selecting and implementing applicable Annex A controls, documenting policies and procedures, and preparing for certification and ongoing surveillance audits. Auditors look for documented processes, evidence of control operation, measurement of effectiveness and a continual improvement loop demonstrating the ISMS works in practice.
A practical ISO 27001 roadmap covers scoping and gap assessment, risk treatment planning, control implementation with measurable KPIs, internal audits, management review, and external certification. Continuous monitoring and retained telemetry, plus structured evidence exports, reduce audit friction because auditors can validate control operation rather than just documentation. The next subsection explains ISMS alignment and responsibilities before showing how ShieldWatch supports audit readiness.
How Does an Information Security Management System Align with ISO 27001?
An ISMS aligns with ISO 27001 by establishing a scoped management framework that links business objectives to risk treatment and control operation, formalizing responsibility, policy and continual improvement. Core ISMS components include a security policy, risk assessment methodology, statement of applicability, documented procedures, an internal audit program, and scheduled management reviews. Leadership must endorse the ISMS, appoint risk owners and provide resources for control implementation and monitoring so policies become measurable outcomes auditors can verify.
- Policy and scope: Define the ISMS boundaries and objectives.
- Risk assessment and treatment: Identify assets, threats and controls; document residual risk.
- Control implementation: Deploy technical and organizational controls aligned with Annex A.
- Monitoring and review: Maintain metrics, run internal audits, and manage corrective actions.
These components form a continual improvement loop: risk assessment informs controls, controls are monitored, findings drive corrective actions, and management review validates effectiveness. The following subsection describes ShieldWatch outputs that support ISMS evidence needs.
In What Ways Does ShieldWatch XDR Facilitate Continuous Monitoring and Audit Readiness?
ShieldWatch XDR supports ISO 27001 readiness with continuous telemetry capture, automated evidence exports and dashboards that map technical events to ISMS processes and auditor expectations. The platform collects endpoint and network logs, correlates incidents and retains historical data auditors use to verify control operation over time. Automated reporting and streamlined incident timelines demonstrate control effectiveness, while pre-built SOAR playbooks speed remediation and produce reproducible audit artifacts.
The table below maps ISMS processes to evidence types and the ShieldWatch artifacts that help demonstrate compliance:
By producing these artifacts, ShieldWatch cuts time spent compiling evidence and helps auditors confirm that controls are not just documented but actively operating. Automated exports and dashboards reduce manual work and make ISO surveillance audits more sustainable.
How Can Organizations Meet SOC 2 Compliance Requirements Effectively?
Meeting SOC 2 requires scoping, implementing controls mapped to the Trust Services Criteria, maintaining evidence of control operation, and completing an independent attestation. Start by defining the services and boundaries in scope, choose the applicable Trust Services Criteria, and implement controls addressing security, availability, processing integrity, confidentiality and privacy as needed. Continuous monitoring, logging, change management and incident handling are core control areas auditors examine; evidence such as system logs, change records, alerts and policy documents demonstrates operational maturity.
A stepwise SOC 2 preparation process speeds readiness and reduces audit friction:
- Scoping and gap analysis: Define systems and boundaries, identify control gaps.
- Control implementation: Deploy technical and administrative controls aligned to the selected criteria.
- Monitoring and evidence collection: Ensure continuous logging and retention across the audit period.
- Audit readiness and attestation: Run internal audits, remediate findings, and undergo the external audit.
These steps require coordinated work across security, IT and compliance teams and sustained monitoring during the audit period. The next subsection explains the Trust Services Criteria and why auditors focus on them.
What Are the Trust Services Criteria and Their Importance in SOC 2?
The Trust Services Criteria—Security, Availability, Processing Integrity, Confidentiality and Privacy—define the outcomes auditors evaluate in SOC 2 attestations. Each criterion maps to specific controls and evidence expectations. Security is the baseline and covers protection against unauthorized access; Availability addresses uptime and recovery; Processing Integrity ensures systems process data completely and accurately; Confidentiality governs sensitive data handling; Privacy focuses on personal data practices. Auditors expect evidence of control design, implementation and operating effectiveness across these categories.
- Security: Access controls, firewalls, monitoring and incident response.
- Availability: Uptime metrics, backups and continuity testing evidence.
- Processing Integrity: Input/output validation, reconciliation records and processing logs.
- Confidentiality: Data classification, encryption records and access audits.
- Privacy: Consent records, subject-rights processes and retention policies.
Documented controls plus continuous evidence collection — logs, change records and monitoring exports — are central to a successful SOC 2 engagement. The next subsection shows how ShieldWatch creates artifacts that support each Trust Services Criterion.
How Does ShieldWatch XDR Support SOC 2 Controls and Reporting?
ShieldWatch XDR supports SOC 2 by delivering continuous logging, availability monitoring, integrity checks and auditor-friendly exports that map to the Trust Services Criteria and reduce manual evidence work. Our 24/7 SOC generates standardized incident records, uptime and performance metrics, and change-event histories auditors can review to verify control operation. Automating detection, containment and reporting shortens audit prep time and produces repeatable artifacts that demonstrate operating effectiveness across criteria.
The following table summarizes how ShieldWatch aligns with each Trust Services Criterion and the practical evidence produced:
These mappings show how ShieldWatch converts telemetry into auditor-ready outputs, supporting both Type I and Type II engagements by documenting consistent control operation over time. That capability shortens audit cycles and strengthens vendor assurance.
What Are the Certification Levels and Compliance Steps for CMMC?
CMMC 2.0 defines assessment levels ranging from self-assessment for basic safeguards to third-party assessments for higher assurance, governing how defense contractors demonstrate cybersecurity maturity. The model groups practices into levels tied to contract requirements; organizations must identify the level their contracts require and implement the associated practices and process maturity. Typical steps include scoping Controlled Unclassified Information (CUI), running a gap analysis against required practices, remediating gaps, and preparing for either self-attestation or a third-party assessment depending on the level.
A concise CMMC workflow includes these stages:
- Scoping: Identify systems and data that store or process CUI and define boundaries.
- Gap analysis: Map current controls against required practices for the target CMMC level.
- Remediation: Implement missing technical and process controls and document procedures.
- Assessment: Prepare for self-assessment or third-party assessment and address findings.
CMMC enforces flow-down obligations across subcontractors and primes, so suppliers must align posture with the prime’s required certification level. The next subsection explains the practical impacts of CMMC maturity expectations.
How Does CMMC Maturity Model Impact Defense Contractors and Enterprises?
CMMC’s maturity model affects contractors by tying assessment obligations to contract eligibility, increasing the need for documented processes, measurable control operation and evidence retention. Prime contractors must ensure subcontractors meet minimum levels, shifting procurement requirements and tightening remediation timelines before bids. Higher maturity levels require investments in technical controls, continuous monitoring and process discipline, plus planning for periodic reassessments and corrective action tracking.
- Obligation flow-down: Primes require assurance from subcontractors, increasing vendor scrutiny.
- Investment in controls: Higher levels demand stronger technical implementations and process maturity.
- Timeline pressure: Certification requirements often align with bidding cycles, creating tight remediation deadlines.
Recognizing these impacts helps organizations plan procurement, budgeting and operational changes to meet defense contracting expectations. The following subsection describes how ShieldWatch supports CMMC readiness in practical terms.
ShieldWatch XDR helps CMMC readiness by providing continuous telemetry, structured evidence exports and managed-service options that close gaps in logging, detection and incident response required for higher maturity levels. Our compliance-ready outputs — correlated logs, incident timelines and playbook execution records — map directly to CMMC practice objectives and reduce manual evidence collection. When internal capacity is limited, ShieldWatch’s managed SOC offers operational execution, remediation support and documentation that accelerate assessment readiness and demonstrate process maturity.
- Control mapping: Telemetry and workflows map to specific CMMC practices for direct evidence.
- Managed remediation: SOC services fill operational gaps and handle containment and reporting.
- Faster evidence collection: Automated exports and dashboards shorten assessment prep time.
For example, a subcontractor that centralizes logs and automates containment playbooks with ShieldWatch produces consistent incident records that satisfy assessor sampling and reduce time-to-certification. The next section examines the broader benefits of continuous compliance monitoring.
How Does Continuous Compliance Monitoring Improve Cybersecurity Posture?
Continuous compliance monitoring shifts point-in-time audits into an ongoing process that detects drift, prioritizes remediation and automatically retains evidence — delivering measurable reductions in detection time and audit prep overhead. Real-time telemetry and automated analysis surface control failures as they occur and track corrective actions to closure. Moving from periodic checks to continuous assurance lowers risk exposure, reduces surprises during audits and helps teams demonstrate sustained control operation to stakeholders.
Measurable benefits include faster detection and containment, reduced audit prep time, improved control coverage and stronger alignment between technical operations and governance. The following subsection looks at how automation and AI enable these outcomes.
What Role Does Automation and AI Play in Reducing Alert Fatigue and Enhancing Response?
Automation and AI reduce alert fatigue by triaging alerts, correlating telemetry across sources and executing deterministic playbooks for containment so analysts can focus on high-priority investigations and strategic remediation. AI-driven triage filters low-fidelity signals and elevates high-confidence detections, while SOAR runbooks automate enrichment, containment and notifications. Industry benchmarks show significant alert reduction and faster mean time to respond when XDR and SOAR are combined with 24/7 SOC operations.
- AI triage: Prioritizes alerts using behavioral baselining and anomaly scoring.
- SOAR playbooks: Automate containment steps and evidence collection to reduce manual toil.
- Measured outcomes: Lower analyst workload, faster containment and consistent evidence capture.
Combining triage and automation improves MTTD and MTR while producing standardized artifacts that support compliance. The next subsection explains how managed SOC services make continuous compliance operational for organizations that need external support.
How Can ShieldWatch’s Managed SOC Services Enable Ongoing Regulatory Adherence?
ShieldWatch’s managed SOC turns continuous monitoring into a regulated, auditable practice by running 24/7 detection, executing predefined SOAR workflows and delivering a reporting cadence aligned to audit and governance needs. Our managed model includes daily monitoring, weekly operational summaries, quarterly compliance reviews and targeted audit-prep sprints that compile evidence for assessors. These deliverables reduce internal resource strain and create a sustainable compliance posture by converting raw telemetry into auditor-friendly exports and executive metrics.
- Operational deliverables: Daily alerts, weekly incident summaries and quarterly control reviews.
- Audit support: Prepackaged evidence bundles, incident retrospectives and remediation tracking.
- Outcome focus: Continuous evidence, reduced audit time and demonstrable control effectiveness.
- Weekly Reports: Provide operational visibility and remediation status for control owners.
- Quarterly Reviews: Help leadership and auditors with trend analysis and control performance.
- Audit-Prep Sprints: Bundle artifacts and perform targeted remediation ahead of assessments.
These service elements turn monitoring data into verified evidence and keep regulatory obligations predictable. Continuous evidence generation and managed operations close the loop between technical controls and compliance requirements.
Frequently Asked Questions
1. What is the importance of cybersecurity compliance frameworks for businesses?
Compliance frameworks give organizations a repeatable way to manage cyber risk, meet legal and contractual requirements, and show customers and auditors that controls are working. They reduce uncertainty during audits, lower the chance of breaches driven by gaps in process or tooling, and help protect reputation and revenue — making them a business imperative as much as a security one.
2. How can organizations assess their current compliance status?
Start with a gap analysis: list systems and data in scope, inventory existing controls, and compare them to the chosen framework’s requirements. Pair that with a risk assessment to prioritize high-impact gaps. Regular internal audits and continuous monitoring help track progress and surface new issues as your environment changes.
3. What are the potential consequences of non-compliance with cybersecurity regulations?
Non-compliance can lead to fines, legal exposure, lost contracts and reputational damage. It also increases the risk of breaches that cause direct financial loss and customer churn. Maintaining compliance protects the organization legally and preserves trust with customers and partners.
4. How often should organizations review and update their compliance strategies?
Review compliance strategies at least annually and whenever significant changes occur — new regulations, major technology shifts or changes in business operations. Continuous monitoring and periodic reassessments ensure controls remain effective as threats and requirements evolve.
5. What role does employee training play in maintaining cybersecurity compliance?
Employee training is essential. Staff must understand policies, know how to spot threats and follow incident procedures. Regular, role-based training reduces human error, strengthens adherence to controls and supports evidence collection for audits.
6. Can small businesses effectively implement cybersecurity compliance frameworks?
Yes. Small businesses should prioritize frameworks that match their risk profile and resources, use managed services or compliance tools where practical, and focus on high-impact controls first. Incremental implementation and automation make compliance achievable without overwhelming small teams.
7. How does continuous compliance monitoring benefit organizations?
Continuous monitoring provides real-time visibility into control health, detects drift quickly, and keeps evidence current for audits. It shortens incident detection and response times, reduces audit prep effort, and helps teams demonstrate sustained control operation to regulators and customers.
Conclusion
Implementing the right cybersecurity frameworks is a practical way to reduce risk, meet legal and contractual obligations, and build customer trust. Standards like NIST CSF, ISO 27001 and SOC 2 provide structure; continuous compliance and automation make that structure sustainable. ShieldWatch helps translate controls into operational outcomes and auditor-ready evidence, so you can focus resources on the highest risks and keep compliance predictable. Contact ShieldWatch to learn how we can help you streamline compliance and operationalize continuous assurance.



Share your link, earn rewards—sign up for our affiliate program!
Join forces with us and profit from every click!