Extended Detection and Response (XDR) brings telemetry, analytics, and automated response together across endpoints, networks, cloud, and identity to cut threat dwell time and make SOC teams more effective. This guide lays out why XDR matters for enterprises, how to plan and deploy it, the concrete technical steps teams should follow, and how to keep the program improving after launch. If your organization wrestles with alert fatigue, siloed telemetry, or long mean time to remediation (MTTR), you’ll find checklists, evaluation criteria, and vendor comparison guidance to support a clear decision.
We cover core concepts (what XDR is and what it delivers), planning and deployment best practices, a prioritized implementation playbook, operational optimization patterns, and vendor evaluation checkpoints for managed XDR offerings. Related technologies such as EDR, SIEM, SOAR, telemetry pipelines, and managed SOCs are referenced throughout to preserve context and search relevance.
What is XDR and Why Should Businesses Implement It?
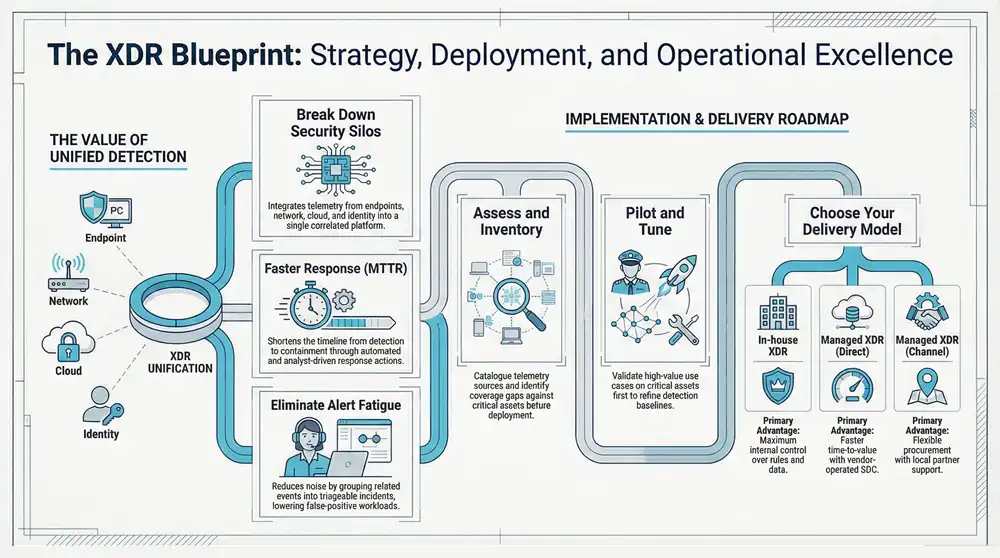
XDR is a platform-style approach that ingests telemetry from endpoints, network devices, cloud services, and identity systems, enriches and correlates those signals with analytics and threat intelligence, and coordinates automated or analyst-driven responses. By linking related telemetry and surfacing high-fidelity incidents, XDR reduces noise, shortens MTTR, and lowers false-positive workloads for SOC teams. Organizations adopt XDR to gain unified visibility, speed up detection, and execute coordinated response across previously fragmented tools—improving security posture while simplifying operations. Knowing the core architecture and expected outcomes lets decision-makers prioritize XDR and set success metrics before procurement. The next section explains the technical building blocks that make consolidated detection and automated response possible.
Understanding Extended Detection and Response Technology
An XDR architecture generally includes collection agents and sensors, a correlation and analytics engine, detection content, orchestration and automation layers, and integrations for threat intelligence and SOAR. Endpoint agents, network sensors, cloud connectors, and identity feeds supply logs, flow data, process telemetry, and authentication events; the platform normalizes and indexes this data for correlation. Detection combines rule-based logic, behavioral analytics, and threat intelligence enrichment to group related events into triageable incidents, reducing alert volume and improving prioritization. Unlike point solutions such as EDR (endpoint-focused) or SIEM (log aggregation with manual correlation), XDR is built to manage correlation across multiple telemetry domains so teams can respond end-to-end more quickly. Understanding this component map clarifies deployment prerequisites and informs planning assessments.
Key Benefits of XDR for Enterprise Security
XDR produces measurable operational gains by unifying telemetry, automating correlation, and enabling coordinated response across the attack surface. First, it shortens detection-to-response timelines by surfacing cross-domain incidents and recommending or running remediation actions, which cuts dwell time and speeds containment. Second, consolidated telemetry and unified alerting reduce analyst fatigue and increase SOC throughput by lowering false positives and packing investigation context into each alert. Third, XDR maximizes ROI from existing investments by integrating EDR, NDR, cloud logs, and identity signals under a single correlation and response framework. Those outcomes make XDR especially relevant to CIOs, CISOs, enterprise SOCs, and MSPs weighing incremental tooling versus an integrated detection platform, and they feed directly into deployment and operational planning.
For organizations evaluating enterprise-grade XDR platforms, ShieldWatch offers an integrated XDR solution delivered as a platform and via managed channels focused on threat detection, SOC workflows, and orchestration. ShieldWatch positions its offering around operational outcomes—consolidated telemetry, strong correlation, and managed response—designed for mid-market and enterprise environments. This vendor example shows one delivery path while keeping procurement decisions grounded in operational needs and measurable security outcomes.
How to Plan Your XDR Deployment: Best Practices for Businesses
Successful XDR deployment starts with clear objectives, an inventory of telemetry, a staffing assessment, and realistic timelines tied to measurable SLAs such as MTTR and detection coverage. Planning should define use cases (for example, lateral movement detection, cloud configuration drift, or identity-based compromise), map telemetry sources to those use cases, and set success criteria for detection and response automation. A structured readiness assessment reduces onboarding surprises by revealing gaps in log coverage, retention policies, and permissions required for data ingestion. The sections that follow include a practical readiness checklist and a deployment-model comparison to help with the build-versus-buy decision.
Assessing Your Security Needs Before XDR Setup
Begin by cataloguing telemetry sources—endpoints, network flows, cloud logs, and identity providers—and evaluate log quality, retention, and coverage gaps against your critical assets and compliance needs. Review existing detection content and baseline alert volumes to gauge analyst capacity, MTTR targets, and the acceptable scope of automated responses. Factor in compliance, data residency, and retention constraints that influence telemetry routing and storage, and list required integrations with SIEMs, SOARs, or ticketing systems for reporting and workflows. This readiness snapshot defines scope, deployment phases, and resource plans and informs whether to run XDR internally or consume it as a managed service.
Choosing Between Managed XDR Services and In-House Solutions
The choice between in-house XDR and managed XDR depends on cost structure, control preferences, time-to-value, and staffing. In-house XDR gives maximum control over detection logic and data but requires significant operations effort, skilled analysts, and tooling investment. Managed XDR hands operational responsibility to a provider with SLAs and experienced SOC staff for faster time-to-value. Many organizations find hybrid approaches attractive—keeping control where it matters while using a managed provider for 24/7 monitoring or specific telemetry domains—to balance expertise with ownership. ShieldWatch supports multiple delivery channels, including direct managed services and partner/MSP options, illustrating how delivery choices can align with staffing and governance needs.
Deployment model comparison: a quick table to guide procurement decisions.
This comparison clarifies trade-offs in cost, effort, and speed-to-value so stakeholders can choose the right procurement path. The next section turns planning into concrete implementation steps technical teams will execute.
What Are the Essential Steps in the XDR Setup Process for Enterprises?
A disciplined setup process reduces risk and accelerates measurable outcomes by combining environment preparation, staged deployments, configuration best practices, and iterative validation. Key steps include environment assessment and cleanup, agent and connector rollout, baseline tuning and detection configuration, pilot validation, phased production rollout, and ongoing tuning informed by postmortems and telemetry growth. Prioritizing high-value telemetry and critical assets during the pilot delivers early wins and proves MTTR improvements quickly. The subsections below provide actionable guidance for infrastructure prep and detection and response configuration.
Preparing Your IT Environment for XDR Integration
Preparation starts with an agent rollout plan that stages endpoints and workloads by risk and criticality and includes rollback and compatibility testing with existing endpoint controls. Enable network and cloud telemetry (flow records, cloud audit logs, identity events) early and confirm collectors and connectors can forward normalized data without exceeding bandwidth or storage limits. Create service accounts and minimal-privilege permissions for ingestion, test integration points with SIEMs or SOAR platforms, and document onboarding runbooks to standardize deployments across teams. Proper preparation reduces integration friction and sets expectations for pilot success and future phases.
This checklist turns high-level steps into verifiable tasks to help teams track readiness and outcomes. The following subsection highlights configuration priorities for sustainable detection quality.
Configuring and Deploying XDR Tools Effectively
Prioritize baseline tuning, focused detection rules, alert enrichment, and clear triage workflows to avoid overwhelming analysts in the early weeks. Start by ingesting broad telemetry while suppressing noisy rules and adding contextual enrichment—asset tags, business impact, user role—to speed prioritization. Define alert routing and escalation, integrate SOAR for playbook-driven containment, and ensure ticketing and reporting hooks are in place for SOC metrics and audit trails. Validate production readiness with tabletop exercises and simulated incidents to refine playbooks and detection thresholds before broadening coverage.
How to Optimize XDR Performance Post-Implementation?
Post-deployment optimization is continuous: tune rules regularly, measure KPIs, and maintain a content and capacity plan so detection quality keeps pace with environment changes. Focus on core KPIs—MTTR, detection rate, analyst triage time, and false-positive rate—to prioritize tuning and justify additional telemetry or automation investments. Operationalizing playbooks reduces manual steps for repeatable incidents while preserving analyst oversight for complex cases. The sections that follow provide runbook-style practices for alert management and a cadence for continuous improvement and scale.
Monitoring and Managing XDR Alerts and Incidents
Run daily operations from a prioritized triage workflow that scores alerts by risk and business impact, applies enrichment to reduce analyst context gathering, and escalates incidents per SLA thresholds. Use playbooks to automate containment actions like network isolation or endpoint quarantine while reserving manual investigation for incidents that need forensic work. Maintain dashboards for KPI tracking and conduct weekly and monthly reviews to uncover recurring false positives and content gaps, then feed those findings into detection tuning and rule suppression. Disciplined alert management reduces fatigue and improves mean time to containment.
Continuous Improvement: Updating and Scaling XDR Solutions
Continuous improvement requires routine rule reviews, incident postmortems, capacity planning for telemetry growth, and regular threat intelligence updates so detection content stays effective and scalable. Establish a quarterly cadence for content reviews, capture lessons learned from incidents, and update playbooks to reflect new techniques and environmental changes. Model telemetry growth to plan storage and retention, and scale compute and correlation capacity as data volumes rise. Adding threat intelligence and proactive threat hunting keeps detection coverage relevant as adversaries evolve.
Which Managed XDR Services Should Businesses Compare?
When evaluating managed XDR providers, compare service model attributes, telemetry breadth, response SLAs, integration support, and delivery options so capabilities match operational goals. A clear vendor evaluation framework helps procurement and security leaders ask precise questions about 24/7 coverage, threat hunting practices, onboarding timelines, and channel delivery options. The following sections give a vendor evaluation checklist and a capability-driven feature list that differentiate strong managed XDR offerings.
Criteria for Evaluating Managed XDR Providers
When vetting providers, confirm telemetry coverage across endpoints, network, cloud, and identity; assess SOC staffing and coverage hours; validate response SLAs and escalation protocols; and request onboarding and integration timelines. Review the provider’s detection-content lifecycle, threat-hunting capabilities, and the level of customization available for rules and playbooks. Check reporting and compliance support, channel or MSP delivery options, and evidence of operational maturity such as documented false-positive management and incident postmortems. These criteria shape procurement discussions and pilot scopes.
This table highlights the core attributes to compare during procurement and helps buyers prioritize capabilities that align with operational goals.
Top Features to Look for in Managed XDR Services
High-value managed XDR services combine wide telemetry coverage, proactive threat hunting, automation, and robust channel support to deliver measurable security outcomes. Look for providers that offer 24/7 SOC coverage staffed by experienced analysts, a documented runbook and playbook library for common incidents, proactive threat hunting and frequent content updates, seamless integration with customer toolchains, and flexible MSP/channel delivery options. Strong onboarding, transparent SLAs, and reporting tied to business risk and compliance requirements are essential for sustainable programs. Partner-delivered options can add procurement flexibility and local support while keeping enterprise-grade detection and response capabilities intact.
As an example of channel-enabled delivery, ShieldWatch delivers enterprise-grade XDR and SOC services both directly and through MSP and channel partners, giving buyers the choice between direct managed engagement or partner-based delivery depending on procurement and support needs. This illustrates how delivery routes affect onboarding timelines and local support without prescribing a single procurement outcome.
If you’re ready to decide, the checklist below summarizes selection steps and next actions, and points teams toward managed service engagement when operational management is preferred. Consider ShieldWatch if you need an enterprise-grade XDR platform combined with managed detection and response delivered directly or via channel partners.
- Inventory telemetry: Confirm endpoint, network, cloud, and identity coverage before vendor selection.
- Define success metrics: Set target MTTR, detection coverage, and SLA expectations for the pilot and production phases.
- Choose delivery model: Select in-house, direct managed, or MSP/channel delivery based on staffing and control needs.
- Pilot high-value use cases: Validate detections on critical assets first, then expand coverage.
- Verify onboarding and SLAs: Confirm timelines, SOC hours, escalation paths, and integration support.
Key procurement actions:
- Request a telemetry proof-of-concept: Confirm the vendor can ingest your logs and demonstrate correlation during the trial.
- Confirm playbook coverage: Verify the vendor’s runbook library addresses your priority incident types.
- Validate channel arrangements: If procuring through an MSP, confirm partner responsibilities and support models.
These procurement actions turn selection criteria into contractual checkpoints and practical validations that reduce procurement risk and speed time-to-value.
This guide provides an actionable XDR implementation path—from defining XDR and its components through planning, deployment best practices, optimization, and vendor evaluation—so teams can structure projects, choose delivery models, and select managed XDR services that fit business and operational priorities. For organizations seeking enterprise-grade managed XDR and SOC services delivered directly or through MSP and channel partners, ShieldWatch is an example of a provider positioned to support detection, response, and managed operations for mid-market and enterprise environments.
Frequently Asked Questions
What are the common challenges businesses face when implementing XDR?
Common challenges include integrating XDR with existing security tooling, normalizing diverse telemetry, and ensuring staff are trained to use new workflows. Alert fatigue from large alert volumes is another frequent issue. Clear objectives, defined success metrics, and a staged rollout help teams avoid these pitfalls. Aligning XDR capabilities with compliance and business requirements also takes deliberate planning during deployment.
How does XDR differ from traditional security solutions like EDR and SIEM?
XDR differs by design: EDR focuses on endpoints and SIEM aggregates logs for analysis, while XDR consolidates telemetry from endpoints, networks, cloud, and identity into a correlated detection and response framework. That holistic view improves event correlation, reduces false positives, and speeds incident response—making XDR better suited to today’s distributed environments.
What role does threat intelligence play in XDR?
Threat intelligence enriches telemetry and detection logic, helping XDR identify known bad indicators and prioritize alerts. Integrated feeds and intelligence-driven rules improve detection accuracy and enable teams to focus on high-risk activity. Intelligence also informs playbooks and content updates so defenses evolve with emerging threats.
How can organizations measure the success of their XDR implementation?
Measure success with KPIs like mean time to detection (MTTD), mean time to response (MTTR), detection coverage, and the false-positive rate. Track analyst triage time and SOC throughput as operational measures. Regular reviews of incident outcomes and analyst workload help confirm the implementation meets defined success criteria.
What are the best practices for maintaining an effective XDR system?
Maintain XDR effectiveness through continuous monitoring, periodic tuning of detection rules, and regular playbook updates based on incident postmortems. Integrate threat intelligence, conduct proactive threat hunting, and invest in analyst training so your team can operate the platform and respond to new techniques confidently.
Can XDR be integrated with existing security tools and systems?
Yes. Modern XDR solutions are designed to integrate with SIEMs, SOAR platforms, EDR tools, and ticketing systems. Successful integration requires planning—mapping data flows, validating APIs and connectors, and ensuring permissions are in place so data flows reliably between systems.
Conclusion
Implementing XDR strengthens security by unifying telemetry and automating coordinated response across complex environments. The approach reduces detection and response times, eases analyst workload, and improves operational efficiency. By following the recommended best practices and evaluating managed XDR options, organizations can accelerate security outcomes. If you’re ready to advance your defenses, explore XDR solutions and delivery models that match your operational priorities.




Sign up for our affiliate program and watch your earnings grow!
Become our partner and turn clicks into cash—join the affiliate program today!
Boost your earnings effortlessly—become our affiliate!
Drive sales, collect commissions—join our affiliate team!
Promote our brand, reap the rewards—apply to our affiliate program today!