Detecting and Preventing Insider Threats in Your Organization
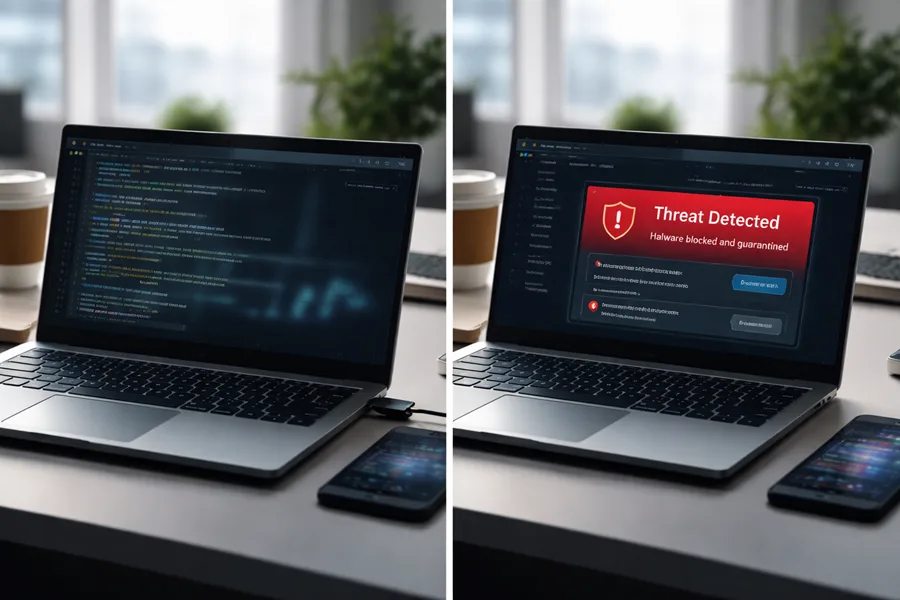
[lwptoc] Insider threats start inside the perimeter—employees, contractors, partners or compromised credentials—and can inflict outsized damage to data, operations and reputation. This guide shows how modern...