Vulnerability management is an ongoing, measurable program that discovers assets, assesses weaknesses, prioritizes by real business risk, and drives verified remediation. This guide shows how a modern program combines automated scanning, risk-based prioritization, disciplined patch management, and continuous monitoring to reduce time-to-remediate and lower exposure across the estate. You’ll get a clear view of the vulnerability lifecycle, why contextual, risk-first scoring beats CVSS-only approaches, practical patching and remediation practices, how continuous monitoring supports compliance, and how managed XDR and SOC services scale enterprise efforts. Practical examples, executive-friendly EAV tables, and actionable checklists help security leaders align tools and processes to outcomes like shorter MTTR, fewer false positives, and stronger audit artifacts.
Throughout, we reference contemporary techniques—automated scanning, AI-driven risk scoring, SOAR playbooks, managed XDR, and continuous monitoring—to help CISOs and SecOps convert detection into reliable, auditable fixes.
What is the Vulnerability Management Process and Why is it Critical?
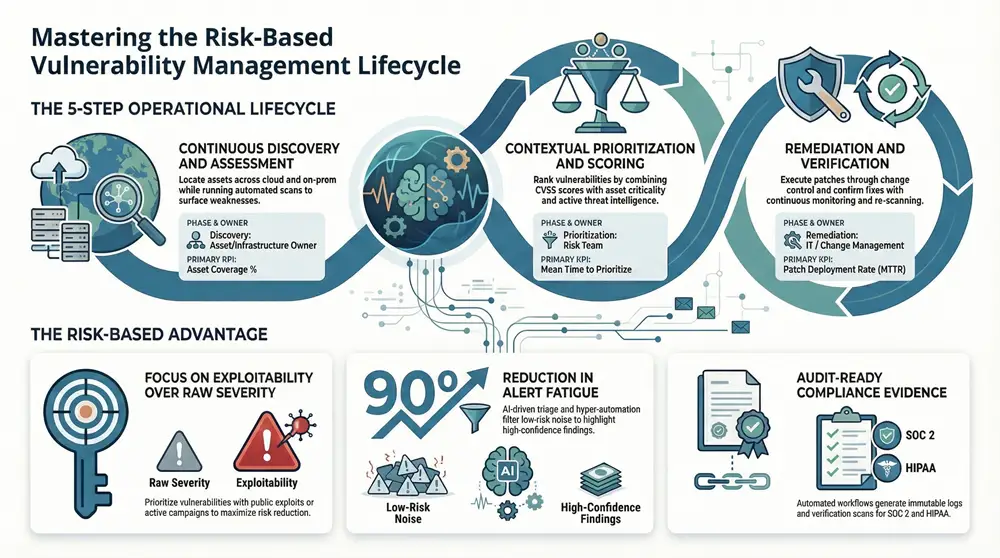
Vulnerability management is the repeatable lifecycle that finds assets, assesses weaknesses, scores and prioritizes risk, remediates issues, and verifies fixes to prevent exploitation. It depends on continuous discovery plus contextual inputs—asset criticality, threat intelligence, and exploitability—so teams act on vulnerabilities that matter to the business. The payoff is a smaller attack surface, shorter dwell times, and a lower chance of breach when detection is paired with timely remediation and validation. Below is a concise lifecycle overview and an executive EAV table to support planning and resourcing.
These lifecycle steps create operational clarity for security teams and stakeholders:
- Discovery and Inventory: Locate assets across cloud, on-prem, and the external attack surface.
- Assessment and Scanning: Run automated scans and manual validation to surface weaknesses.
- Prioritization and Risk Scoring: Use contextual, risk-based prioritization to direct remediation.
- Remediation and Patch Management: Coordinate fixes with change control and rollback plans.
- Verification and Continuous Monitoring: Confirm repairs and watch for regressions or new exposures.
This flow ensures discovery drives prioritized action, and prioritization drives efficient remediation and verification.
Executive EAV summary mapping lifecycle elements to decision-making:
This table ties cadence and tooling to lifecycle phases and helps leaders prioritize investment in continuous discovery and verification. That alignment moves teams from isolated scans to a cohesive vulnerability program.
How Does Vulnerability Assessment Identify Security Weaknesses?
Vulnerability assessment uncovers weaknesses through discovery, automated scanning (agent or agentless), manual validation, and external surface analysis. Automated scans quickly enumerate known CVEs and common misconfigurations across endpoints, cloud workloads, and network devices. Manual validation reduces false positives and confirms exploitability before remediation. Agent-based approaches provide richer telemetry and continuous coverage for endpoints and cloud instances; agentless scans simplify rapid discovery for appliances and external systems. Adding external attack-surface management ensures exposures visible to adversaries are found and prioritized.
Assessment results feed prioritization and remediation workflows, producing verifiable tickets and evidence artifacts for compliance. Combining scanning modalities with human validation balances scale and accuracy and ensures remediation targets real-world risk.
What are the Key Steps in the Vulnerability Management Lifecycle?
The lifecycle breaks into distinct operational steps that map to accountable roles, KPIs, and verification artifacts used by SecOps and IT. Identification relies on asset inventories and automated scans to create vulnerability datasets; prioritization enriches those findings with asset criticality and threat context; remediation assigns work and tracks patch deployments; verification confirms fixes with follow-up scans and analytics. Each step yields measurable outcomes—scan coverage, time-to-patch, remediation rate, and verification success—that align to SLAs and compliance needs.
Clear ownership and KPI tracking turn vulnerability management into a measurable program that closes exploitable windows and supports risk reporting.
How Does Risk-Based Prioritization Enhance Vulnerability Remediation?
Risk-based prioritization steers limited resources to vulnerabilities most likely to be exploited and most damaging to the business. It combines CVSS with exploitability data, asset criticality, telemetry, and threat intelligence to produce risk scores that reflect business impact rather than raw severity. The outcome is faster MTTR for high-risk items, fewer low-value remediation tasks, and clearer decisions about patch timing and compensating controls. Below are the core inputs to risk-based scoring and an example EAV table showing prioritization factors.
Key inputs for risk-based prioritization include:
- Exploitability and active exploit evidence
- Asset criticality and data sensitivity
- Existing compensating controls
- Threat intelligence signaling adversary interest or campaigns
Using these inputs reduces noise and focuses remediation on the findings that matter most, improving efficiency and lowering exposure to active threats.
Practical comparison of risk attributes and prioritization outcomes:
These attributes turn scan output into actionable priorities, letting teams apply limited patch cycles where they yield the greatest risk reduction.
ShieldWatch example — AI-driven prioritization:
ShieldWatch XDR combines AI-driven risk scoring with integrated threat context to operationalize risk-based prioritization. By merging endpoint telemetry, AI Agent Hyperautomation, and curated intelligence, ShieldWatch surfaces high-confidence prioritized findings while cutting alert fatigue. Teams get rapid verdicts and contextual scores that flag exploitable vulnerabilities on critical assets—so remediation is targeted, faster, and less noisy.
This vendor example shows how AI and SOC capabilities can tighten the feedback loop between detection, prioritization, and remediation at enterprise scale.
What Role Does AI-Driven Risk Scoring Play in Prioritizing Vulnerabilities?
AI-driven risk scoring supplements traditional rules by learning from telemetry, past remediation outcomes, and threat feeds to dynamically rank vulnerabilities. Typical inputs include endpoint behavior, exploit telemetry, asset importance, and external intelligence; outputs are risk scores that reflect both likelihood of exploitation and potential business impact. AI helps filter low-risk noise and highlights high-confidence cases for immediate action, shortening investigation time for analysts. Ongoing model validation and analyst feedback keep scores accurate and adaptive to shifting adversary tactics.
Operationalizing AI-assisted scoring improves patch planning and workflow efficiency, letting scarce remediation capacity focus on fixes that meaningfully reduce breach risk.
How Does Contextual Threat Intelligence Improve Remediation Decisions?
Contextual threat intelligence adds real-world signals—active exploit campaigns, proof-of-concept releases, or actor TTPs—that change remediation urgency and technique. When intelligence is integrated into VM tools, a vulnerability with an active exploit in the wild becomes higher priority than a similar CVSS-scored item with no active threat. Threat context also guides remediation choices: whether to patch now, isolate a system, or apply compensating controls and enhanced monitoring.
Linking intelligence to remediation workflows produces faster, more targeted responses and stronger evidence trails for auditors and leadership—so decisions are both timely and defensible.
What are Best Practices for Effective Vulnerability Remediation and Patch Management?
Effective remediation combines clear policy, safe automation, phased rollouts, and verification to reduce risk while minimizing operational disruption. Start with documented patch policies and defined change windows, automate safe discovery-to-ticket workflows, and use phased deployments with rollback plans to limit risk. Maintain a steady verification cadence to confirm fixes and retain audit artifacts. The list below distills core operational rules teams should adopt.
Core best practices for remediation and patch management:
- Define Patch Policies and Windows: Establish SLAs and change control for critical and non-critical fixes.
- Automate Safe Workflows: Link scans to ticketing and run pre-deployment tests to accelerate fixes safely.
- Phased Rollouts with Rollback: Validate in canary groups before enterprise-wide deployment to reduce incidents.
- Integrate SOAR and Ticketing: Use playbooks and ITSM integrations to orchestrate remediation and capture evidence.
- Verify and Re-scan: Confirm remediation success and monitor for regressions after deployment.
These practices make remediation timely, auditable, and reliable while preserving business continuity.
Example: ShieldWatch automation in remediation:
ShieldWatch couples hyper-automation with 150+ pre-built SOAR workflows to automate alert triage and remediation orchestration. These playbooks accelerate patch orchestration, endpoint isolation, and automated verification while syncing with ITSM systems. Pre-built workflows reduce engineering overhead and speed safe automation adoption in complex enterprise environments.
This example illustrates how automation and SOAR content can operationalize remediation best practices without heavy custom development.
How Can Automated Patch Management Reduce Security Gaps?
Automated patch management shrinks exposure windows by speeding testing, deployment, and verification while retaining rollback safeguards. A mature pipeline moves findings through discovery, automated testing in isolated environments, phased deployment, and post-deploy verification with re-scans. Automation typically raises patch rates and shortens MTTR—especially for high-severity items. Safeguards like canary deployments, automated rollback, and exception processes preserve service stability while accelerating remediation velocity.
Teams that adopt staged automation generally see measurable gains in patch coverage and lower administrative burden, freeing staff to focus on complex incidents and proactive hunting.
What SOAR Playbooks Support Incident Response and Containment?
SOAR playbooks codify common remediation steps and speed containment when vulnerabilities are exploited or at imminent risk. Typical playbooks cover patch orchestration, endpoint isolation, credential resets, network segmentation changes, and automated verification scans. Each playbook connects to ticketing, CMDB, and EDR to preserve traceability and produce audit-ready evidence. Curated templates reduce human error and ensure consistent, repeatable responses across incidents.
Common SOAR playbooks include:
- Patch Orchestration: Automate test, deploy, verify, and rollback paths for patches.
- Endpoint Isolation: Quarantine affected hosts and capture forensic evidence.
- Credential Rotation: Reset service and user credentials linked to compromised systems.
These playbooks shorten response cycles and ensure remediation steps are repeatable and documented for compliance and post-incident review.
How Does Continuous Monitoring and Compliance Support Security Posture?
Continuous monitoring blends telemetry, 24/7 SOC coverage, and automated verification to detect remediation failures, regressions, or new exposures as they appear. It verifies fixes and prevents configuration drift from reintroducing vulnerabilities. From a compliance view, continuous records—scan reports, patch logs, and change records—map directly to control requirements and auditor expectations. Below we explain SOC benefits and show how common VM artifacts align to major frameworks.
Continuous monitoring reduces dwell time and provides assurance that remediation workflows completed successfully. Compliance reporting turns operational artifacts into audit evidence—so monitoring both secures systems and simplifies regulatory adherence.
What are the Benefits of 24/7 SOC Monitoring for Vulnerability Management?
A 24/7 SOC provides continuous analyst coverage to validate alerts, confirm exploitation attempts, and coordinate urgent remediation outside business hours. Around-the-clock monitoring shortens detection-to-remediation windows, supplies prioritized analyst guidance, and enables verification of critical fixes across time zones. KPIs—MTTR, detection-to-action time, and verified remediation rates—improve when SOC triage drives remediation. SOC analysts also enrich vulnerability context with telemetry and hunting results, improving prioritization and remediation effectiveness.
Continuous SOC engagement ensures high-risk vulnerabilities are handled promptly and verified consistently across operational cycles.
How Does Compliance Reporting Align with SOC 2, HIPAA, and ISO 27001?
Vulnerability management artifacts—scan logs, remediation tickets, patch deployment records, and verification scans—map directly to controls in SOC 2, HIPAA, and ISO 27001. Immutable logs and consolidated evidence support auditor requests for timelines, owners, and proof of remediation. Regular reporting and control mappings demonstrate ongoing compliance rather than a point-in-time snapshot. The table below links VM artifacts to framework expectations for clarity.
Aligning VM artifacts with compliance controls produces the evidence auditors expect while improving security posture and transparency.
What Advantages Do Managed XDR and SOC Services Offer for Enterprise Vulnerability Solutions?
Managed XDR and SOC services extend an organization’s detection, triage, and response capacity without a proportional increase in headcount or tooling complexity. These services correlate telemetry across endpoints, network, cloud, and identity to detect sophisticated attack patterns, prioritize vulnerabilities in context, and coordinate remediation with IT and change teams. Operational benefits include 24/7 coverage, access to specialized threat hunting, and fewer false positives through advanced correlation—together these drive measurable MTTR and security improvements. Below is a business-oriented EAV table mapping capabilities to KPIs to aid procurement decisions.
Those capabilities translate into measurable gains across security operations, making managed services a practical route to mature VM programs without a large internal build.
ShieldWatch managed XDR and SOC integration (business summary):
ShieldWatch delivers an autonomous XDR platform paired with a 24/7 SOC that blends AI Agent Hyperautomation with human analyst collaboration. The platform’s AI-driven triage and 150+ pre-built SOAR workflows reduce alert fatigue by up to 90% and speed remediation through automated playbooks. ShieldWatch highlights rapid verdict times—sub-8.5 second average—plus 90-day historical threat hunting, 100% cloud coverage, and built-in compliance readiness for SOC 2, HIPAA, CMMC 2.0, and ISO 27001. For enterprises and MSPs, this managed model delivers scalable expertise and resilience without the cost of building equivalent in-house capabilities.
This positions managed XDR and SOC as an efficient, results-driven option for faster, evidence-backed remediation.
How Does AI-Human Collaboration Enhance Threat Detection and Response?
AI-human collaboration delegates repetitive triage and low-risk decisions to automated agents while reserving complex analysis, attribution, and escalation for skilled analysts. AI provides rapid verdicts and confidence scores from telemetry and models; humans validate and refine those outputs, improving the models over time. This collaboration speeds detection, reduces false positives, and ensures remediation actions with business impact receive appropriate human oversight. Metrics like analyst time saved, lower alert volumes, and improved high-confidence detection rates show the operational gains.
Combined AI and human workflows amplify expertise and accelerate remediation while preserving governance and oversight.
What Differentiates Managed SOC Services from In-House Security Operations?
Managed SOC services differ from in-house SOCs in scalability, cost structure, and access to specialist skills and tooling. Managed providers deliver on-demand expertise, broad telemetry correlation across customers, and pre-built automation that’s costly to replicate internally. In-house teams require ongoing investment in hiring, training, tooling, and 24/7 staffing. CIOs and CISOs typically weigh maturity needs, budget, and time-to-value; for many organizations, managed services are the faster path to advanced capabilities like proactive hunting and integrated SOAR at scale.
Key decision factors include:
- Scalability and staffing flexibility
- Speed of deployment and operational maturity
- Access to specialized analysts and threat intelligence
- Cost comparison vs. hiring and tooling investments
Frequently Asked Questions
What are the common challenges organizations face in vulnerability management?
Common challenges include limited resources, skills shortages, and the complexity of heterogeneous environments. Teams often struggle with high alert volumes from automated scans, difficulty prioritizing findings, and poor integration of VM processes into existing workflows—which can delay remediation. Maintaining consistent compliance evidence across frameworks adds further complexity, requiring reliable documentation and reporting of assessments and fixes.
How can organizations measure the effectiveness of their vulnerability management program?
Measure effectiveness with KPIs such as mean time to remediate (MTTR), number of vulnerabilities identified and resolved, and percent of critical vulnerabilities patched within defined SLAs. Regular audits and maturity assessments provide additional insight. Track reductions in attack surface, frequency of successful exploits, and verification pass rates. Continuous monitoring and feedback loops are essential for iterative improvement.
What role does employee training play in vulnerability management?
Employee training builds a security-aware culture and reduces human error. Programs should cover common threats, safe computing practices, and reporting procedures. Regular training and simulated exercises (for example phishing drills) improve staff ability to spot and report vulnerabilities and contribute to overall resilience.
How does vulnerability management integrate with incident response plans?
Vulnerability management and incident response are tightly linked. Effective VM reduces incident likelihood by closing known gaps. When incidents occur, VM data helps incident responders identify exploited weaknesses and prioritize containment and remediation. Integrating VM outputs into IR playbooks ensures response decisions reflect the current threat and vulnerability landscape.
What technologies are essential for a robust vulnerability management program?
A robust program relies on automated vulnerability scanners, patch management platforms, and threat intelligence. Scanners find issues across assets; patch tools speed remediation; threat feeds add context for prioritization. SIEM or XDR platforms help aggregate telemetry and correlate events, enabling detection and response tied to vulnerability findings.
How can organizations ensure compliance with regulatory requirements through vulnerability management?
To meet regulatory requirements, align VM practices to framework controls (HIPAA, SOC 2, ISO 27001). Keep detailed records of assessments, remediation activities, and reporting. Regular audits and continuous monitoring help verify adherence. Having consolidated, auditable artifacts available makes compliance review more efficient and demonstrates an ongoing security posture.
Conclusion
A strong vulnerability management program reduces risk by systematically finding and fixing security gaps. By combining automated tools, risk-based prioritization, disciplined patching, and continuous verification, organizations shrink their attack surface and produce the evidence auditors expect. Adopting these practices builds resilient operations and a culture of proactive security. Start refining your vulnerability management approach now to protect assets and improve long-term resilience.