Managed Extended Detection and Response (Managed XDR) is a subscription service that combines continuous telemetry collection, cross-domain correlation, and automated response playbooks to produce measurable return on security investment (ROSI) through cost avoidance and reduced breach exposure. This guide shows how faster detection, automated containment, and tool consolidation translate into hard-dollar savings and lower business risk. Security leaders often find it hard to put a number on security value because benefits are indirect—avoided breaches, less downtime, fewer escalations across IT, legal, and business teams.
Here we translate those outcomes into repeatable ROI metrics (ALE, ROSI, MTTD, MTTR), offer practical calculation frameworks, identify the OPEX categories most affected, and provide scenario templates for executive decision-making. We also map risk-reduction pathways and include an example vendor section showing how ShieldWatch XDR accelerates time-to-value without getting lost in technical detail. By the end, you’ll have the formulas, metrics, and stepwise method to estimate your organization’s ROI from Managed XDR.
What Is Managed XDR and How Does It Deliver ROI?
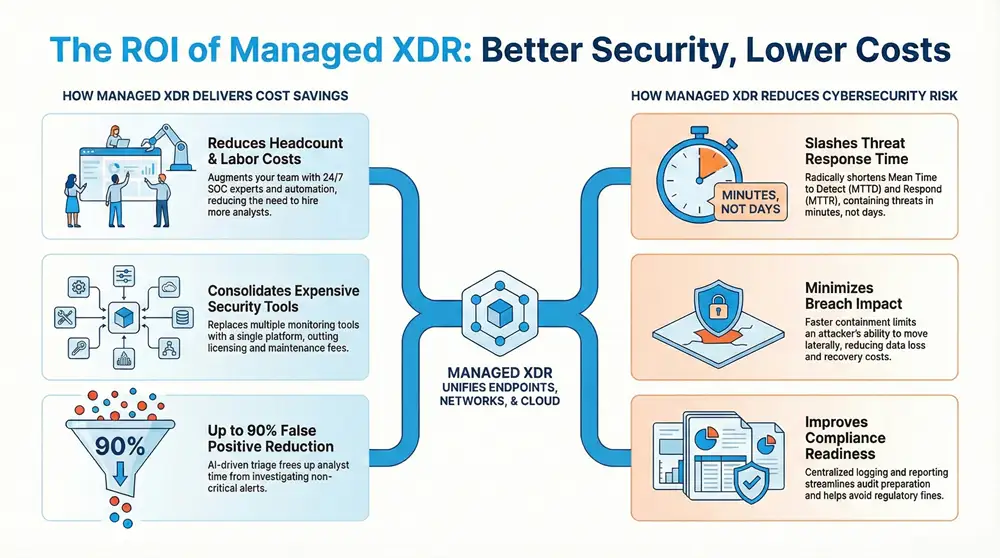
Managed XDR is a managed security service that ingests telemetry from endpoints, network, cloud, and identity systems, correlates signals with analytics, and orchestrates automated containment to reduce incident impact and operational burden. ROI comes from two clear channels: fewer and smaller incidents thanks to faster detection and containment, and lower operating costs through automation and vendor consolidation. Together these effects reduce expected annual breach costs and shrink SOC labor and licensing spend—improving ROSI and lowering ALE. Understanding those mechanisms makes it easier to pick the right metrics for your business case.
Managed XDR creates value through practical operational levers:
- Consolidating many monitoring tools into a single detection-and-response pipeline.
- Providing continuous 24/7 monitoring plus automated containment to shorten MTTR.
- Applying AI-driven triage and playbooks to cut false positives and manual investigation time.
Those levers convert directly into financial outcomes—fewer required FTEs and fewer costly incident escalations—which we quantify in the sections that follow.
Defining Managed Extended Detection and Response Services
Managed Extended Detection and Response (Managed XDR) bundles cross-domain detection (endpoints, cloud, network, identity) with managed analysis and response. Unlike standalone EDR, MDR, or SIEM, Managed XDR provides correlation across sources, automated remediation, and continuous SOC coverage in a single managed service that owns detection-to-containment workflows. Typical elements include telemetry ingestion, threat hunting, SOAR-driven playbooks, and incident reporting; operational responsibilities—alert tuning, integration, and first-stage triage—shift to the provider while the enterprise retains policy control and escalation rights. The managed model reduces the day-to-day burden of alert noise and tool sprawl, freeing security teams to focus on strategic priorities instead of routine triage.
The next subsection maps concrete product capabilities to ROI drivers so you can see specific ways a platform accelerates savings and reduces risk.
How ShieldWatch XDR Enhances Security Operations and Investment Value
ShieldWatch XDR demonstrates how product capabilities become ROI drivers: AI Agent Hyperautomation and round-the-clock SOC monitoring speed detection and containment; rapid verdicting (sub-8.5 second threat verdicts with containment in minutes) reduces dwell time and limits exfiltration. These features lower average incident costs by shrinking time-to-containment and cutting manual analyst hours through AI-agent collaboration and 150+ pre-built SOAR workflows that automate common playbooks. Operational advantages—fast deployment with retroactive 90-day historical log analysis and free deployed sensors—compress time-to-value and reduce integration costs, while reported false-positive reductions up to 90% materially cut analyst triage time.
Map those features to financial metrics—shorter MTTR, fewer analyst hours, and fewer escalations—and security leaders can estimate how ShieldWatch-style capabilities affect ROSI and annualized loss expectancy.
How Can You Quantify Cost Savings from Managed XDR?
Start quantifying savings by identifying the expense categories Managed XDR impacts, then apply conservative assumptions to calculate annualized benefits. The practical approach converts lower incident frequency and severity, plus efficiency gains, into dollar values using FTE cost avoidance, license consolidation, and avoided breach estimates. In practice you’ll estimate reclaimed FTE hours, eliminated licensing fees, and incidents prevented or mitigated; sum those values to get annual benefit, then compare against the service fee to calculate ROSI and payback. This produces repeatable, defensible figures for executive review.
Primary cost-savings categories include:
- Headcount and labor costs (FTE avoidance and productivity gains).
- Tool licensing and maintenance savings from consolidation.
- Incident remediation and third-party forensic costs avoided.
- Infrastructure and storage savings from centralized telemetry handling.
Which Operational Expenses Are Reduced by Managed XDR?
Most operational savings with Managed XDR show up in labor, tooling, and incident-handling costs. The mechanism is automation plus managed coverage that replaces repetitive tasks and redundant platforms. Labor savings come from fewer required SOC analysts, lower on-call churn, and less time spent on false positives; tooling savings come from removing overlapping licenses and integration overhead; incident-handling savings come from shorter containment windows and fewer escalations to costly external firms. A common calculation starts with: FTE cost avoided = fully burdened SOC FTE cost × FTEs redeployed or not hired, then adds reductions in overtime and contractor spend.
To stay conservative, model low/medium/high scenarios and validate assumptions for incident frequency and average remediation cost so stakeholders see a realistic range. Those scenario outputs feed directly into ROSI and payback calculations described later.
How Does Automation and Tool Consolidation Drive Financial Benefits?
Automation and tool consolidation reduce MTTD and MTTR while lowering operational overhead through orchestrated playbooks and a unified data model. That means fewer hours per incident and reduced licensing bills. Automated SOAR workflows execute routine containment steps—quarantine, block, enrich—without human intervention, saving triage minutes that add up to significant annual hours. Consolidating tools removes duplicate telemetry pipelines, cutting license and integration maintenance costs and simplifying compliance reporting.
To quantify these benefits: measure average triage time per alert before and after automation, multiply by alert volume and analyst hourly cost, then add license savings from retired tools. That produces a defensible, auditable annualized savings figure you can plug into ROSI calculations.
In What Ways Does Managed XDR Reduce Cybersecurity Risk?
Managed XDR reduces cyber risk by improving detection accuracy, accelerating response, and broadening visibility across previously siloed telemetry—lowering the chance of large-scale breaches and shrinking the financial impact when incidents happen. The mechanism is greater visibility plus automated containment, which shortens attacker dwell time and limits lateral movement. Measurable outcomes include reduced MTTR, fewer false positives, and a smaller attack surface thanks to continuous monitoring and retrospective log analysis—each mapping directly to lower ALE and stronger business continuity.
Common risk-reduction outcomes to watch for:
- Shorter mean time to detect (MTTD) and mean time to respond (MTTR).
- Lower probability of successful data exfiltration because containment happens sooner.
- Improved compliance readiness that reduces potential fines and remediation costs.
Together, these mechanisms reduce the number and scope of business-impacting incidents. The table below links those mechanisms to financial outcomes in an EAV-style view.
How Does Rapid Threat Detection and Response Minimize Breach Impact?
Faster detection and response reduce breach impact by shortening attacker dwell time, limiting data exfiltration, and enabling quicker recovery—together these lower direct remediation costs and indirect business interruption losses. The causal chain is straightforward: earlier detection → faster containment → smaller scope of compromise → lower recovery expenses and less downtime. Quantitatively, if MTTR falls from days to hours, average incident costs often drop materially because forensic scope, notification obligations, and legal exposure scale with time and data lost.
When modeling savings, apply a conservative multiplier to average incident cost based on containment improvements—for example, a 50% reduction in MTTR might yield a 30–60% reduction in recovery costs depending on data sensitivity and regulatory exposure.
What Compliance Cost Avoidance and Reputational Benefits Are Achieved?
Managed XDR improves compliance readiness by preserving centralized evidence, streamlining reporting, and mapping controls—cutting audit prep time and lowering the odds of regulatory fines. Continuous monitoring plus pre-built controls and reporting templates reduce the marginal cost of audits and remediation. Reputational benefits come from fewer public incidents and faster, more effective responses when incidents do occur, which helps limit customer churn and revenue impact.
Estimating these benefits requires valuing avoided fines, reduced audit labor, and projected customer churn from breach scenarios. While less precise than direct cost savings, reasonable ranges can be included in ALE models to capture this indirect but material portion of ROI.
How Does ShieldWatch XDR Provide a Superior ROI Advantage?
ShieldWatch XDR is presented as an autonomous cybersecurity platform that accelerates ROI through AI-driven automation, rapid verdicting, and features built to cut time-to-value and reduce manual work. The core mechanism pairs hyperautomation with 24/7 SOC coverage to lower incident impact and operating costs; built-in compliance tooling and retroactive 90-day log analysis further reduce audit and forensic spend. We use these vendor-specific capabilities as an illustrative case to show how a modern Managed XDR can change the economics of security without clouding the neutral analysis.
Key ShieldWatch differentiators that map to ROI include AI Agent Hyperautomation, sub-8.5 second threat verdicts with containment in minutes, false-positive reductions up to 90%, fast deployment with 90-day historical log analysis, and 150+ pre-built SOAR workflows that cut weeks off tuning and playbook development. Combined, these shorten MTTR, reduce analyst hours, and lower integration costs—core inputs in ROSI modeling.
What Unique Features Enable Faster Deployment and Reduced Alert Fatigue?
ShieldWatch speeds deployment with free sensors and automated onboarding that ingest telemetry quickly, while pre-built SOAR playbooks and AI-agent collaboration reduce tuning time and alert noise. Template-driven orchestration plus automated enrichment shortens the ramp from purchase to operational effectiveness and lowers false positives that otherwise consume analyst cycles. Less alert fatigue lets existing analysts focus on meaningful investigations, delaying hires or enabling redeployment and reducing churn.
Faster deployment and lower alert volume both increase time-to-value and directly affect FTE avoidance and licensing consolidation estimates used in ROI calculations.
Which Customer Success Stories Demonstrate Quantifiable ROI?
Anonymized customer examples regularly report measurable results—large MTTR reductions, big drops in false positives, and faster compliance reporting after adopting advanced Managed XDR. The pattern is consistent: challenge (fragmented tools, slow response), action (deploy XDR with automation and 24/7 SOC), result (lower incident cost, controlled SOC headcount). When customers quantify these outcomes, they feed directly into ROSI models as reductions in annual incident spend and labor expense.
Numeric outcomes vary by environment, but platforms that emphasize automation, rapid verdicting, and retroactive analysis tend to deliver the most predictable ROI. Next, we explain how to apply these improvements in a calculable ROI exercise with an interactive calculator.
How Can You Calculate Your Potential ROI with ShieldWatch Managed XDR?
Calculating ROI requires a consistent framework: collect inputs, choose conservative assumptions, compute baseline annualized loss, apply expected Managed XDR improvements, then calculate net savings and ROSI. The mechanism is scenario modeling using formulas like and . Executives should supply current tooling spend, fully burdened FTE costs, incident frequency, and realistic percentage improvements in MTTR and false positives to generate defensible outputs.
Below is a concise checklist of required inputs and typical outputs to prepare for a platform-specific ROI tool.
- Inputs required: current annual incident count, average incident cost, SOC FTE count and fully-burdened costs, current tooling/licensing spend.
- Expected improvements: projected % reduction in MTTR, % false positive reduction, number of FTEs avoided or redeployed.
- Outputs produced: estimated annual savings, payback period, ROSI percentage.
With these inputs defined, run sensitivity analyses to show best-case, expected, and conservative outcomes and present the results to stakeholders for approval.
What Metrics and Frameworks Are Used for ROI and Risk Reduction Analysis?
Key metrics are ROSI (Return on Security Investment), ALE (Annualized Loss Expectancy), MTTD (Mean Time to Detect), and MTTR (Mean Time to Respond). The mechanism is applying observed or estimated percentage improvements to baseline values to calculate financial delta. ROSI formula: . ALE formula: . Use conservative ARO assumptions and validated SLE inputs (remediation, legal, notification, business interruption) to avoid optimistic projections.
When presenting results, include scenario ranges and sensitivity tables so stakeholders can see how MTTR improvements or different FTE assumptions affect payback and ROSI.
How to Use the Interactive ShieldWatch XDR ROI Calculator for Personalized Estimates
The ShieldWatch XDR ROI calculator asks for executive and technical inputs—annual incident frequency, average incident cost, current SOC FTE count and fully-burdened cost, and annual tooling spend—to estimate annualized savings, payback period, and ROSI. The tool applies assumed percentage improvements (detection speed, containment time, false positive reduction, and FTE avoidance) to your inputs to produce an estimated annual savings figure and a clear payback timeline. To get accurate results, provide median incident costs that include business interruption and legal exposure, while technical leads supply realistic improvement percentages based on platform capabilities.
After reviewing outputs, run sensitivity analyses by varying MTTR and incident frequency to see how outcomes change, then use those results to request a tailored demo or procurement conversation based on the modeled ROI.
Why Choose Managed XDR Over Traditional SOC Models for Better ROI?
Managed XDR often delivers better ROI than traditional in-house SOC models by replacing high upfront CAPEX, long hiring timelines, and fragmented tooling with predictable OPEX and measurable SLAs. The mechanism is outsourcing continuous, complex tasks to a platform that leverages automation and a pooled SOC team, reducing total cost of ownership (TCO) while improving time-to-value and operational resilience. For executives, the key differences are predictable spend, faster deployment, and demonstrable reductions in incident impact and headcount risk.
What Are the Cost and Efficiency Differences Between Managed XDR and In-House SOC?
Cost differences focus on CAPEX versus OPEX, hiring and training overhead, and tooling complexity; efficiency differences come from automation, centralized expertise, and vendor playbooks. In-house SOCs require recruiting specialized analysts, ongoing training, and investments in multiple point products—creating unpredictable budgets and slower time-to-value. Managed XDR consolidates many of those variables into a single subscription while delivering packaged playbooks and continuous improvement from pooled threat intelligence, raising detection quality and lowering per-incident labor hours.
When modeling TCO over a three-year horizon, include hiring ramp risk, turnover, and tooling refresh cycles for in-house SOCs; those factors often favor Managed XDR for mid-market and enterprise organizations planning to scale.
How Does Managed XDR Address the Cybersecurity Talent Gap and Alert Fatigue?
Managed XDR helps close the talent gap by augmenting teams with provider SOC analysts, AI-assisted triage, and automated playbooks that remove routine work and let internal staff focus on higher-value projects. The mechanism—analyst augmentation plus hyperautomation—increases effective analyst throughput and lowers turnover caused by repetitive, low-value tasks. A platform that significantly reduces false positives and automates common response steps can free dozens of analyst hours per week, translating to delayed hiring or redeployed personnel.
Beyond immediate labor savings, this capability improves retention and operational maturity—strengthening the long-term ROI case for Managed XDR.
Frequently Asked Questions
What types of organizations can benefit from Managed XDR services?
Managed XDR is a fit for a wide range of organizations—from growing SMEs to large enterprises—across most industries. Any business that depends on digital systems and data benefits from improved threat detection and response. Industries with high regulatory or data-sensitivity needs (finance, healthcare, retail) often see the biggest upside, but organizations seeking to lower operational overhead and speed incident response will find value regardless of sector.
How does Managed XDR improve compliance with cybersecurity regulations?
Managed XDR supports compliance by providing continuous monitoring, centralized logs, and automated reporting. Those capabilities make it easier to collect evidence for audits, shorten audit prep, and speed remediation. Proactive detection and rapid response also reduce the likelihood and impact of reportable incidents—helping organizations meet regulatory obligations and avoid fines.
What are the key performance indicators (KPIs) to measure the success of Managed XDR?
KPIs to track include Mean Time to Detect (MTTD), Mean Time to Respond (MTTR), the number of incidents detected and mitigated, and reduction in false positives. Financial KPIs—cost savings from reduced incident response time and lower operational spend—are also important. Compliance metrics (audit readiness, regulatory adherence) provide another view of success. Together, these KPIs show both technical effectiveness and business value.
Can Managed XDR integrate with existing security tools and infrastructure?
Yes. Managed XDR is built to integrate with existing security stacks—firewalls, EDRs, SIEMs, identity systems—via APIs and connectors. That allows organizations to leverage current investments while improving detection and response. Integration reduces migration risk and helps maintain a cohesive security ecosystem for faster, more accurate threat handling.
What is the typical implementation timeline for Managed XDR?
Implementation timelines vary by organization complexity, but deployments often complete in a few weeks to a few months. Typical phases include environment assessment, platform configuration, and tool integrations, followed by a tuning period. Fast-deploy options, retroactive log analysis, and pre-built playbooks can shorten time-to-value. Ongoing support and optimization help teams get the most from the service.
How does Managed XDR handle evolving cyber threats?
Managed XDR addresses evolving threats through continuous monitoring, analytics, and machine learning, backed by threat intelligence and behavioral analysis. Automated response capabilities enable rapid containment, and regular platform updates ensure defenses adapt to new tactics. The result is a proactive, adaptive defense that minimizes damage from emerging threats.
Conclusion
Managed XDR delivers both stronger security and measurable cost benefits. By combining automation, continuous monitoring, and centralized analysis, organizations shorten response times, reduce breach exposure, and realize operational savings. The ROI frameworks and metrics covered here give decision-makers a practical way to model those benefits. If you’re ready to quantify potential savings and build a business case, explore ShieldWatch Managed XDR and our ROI tools to estimate impact for your environment.




Refer friends and colleagues—get paid for every signup!
Get paid for every referral—enroll in our affiliate program!
I really enjoyed playing. tacorita bicicleta steal a brainrot has some interesting mechanics that keep you coming back for more.
Share our products and watch your earnings grow—join our affiliate program!
Partner with us for generous payouts—sign up today!
Share our offers and watch your wallet grow—become an affiliate!
Turn referrals into revenue—sign up for our affiliate program today!
Join our affiliate program and start earning today—sign up now!
Turn your audience into earnings—become an affiliate partner today!
Unlock exclusive affiliate perks—register now!