Combating APTs: Practical XDR and Managed SOC Strategies for Enterprise Protection
Advanced persistent threats (APTs) are targeted, stealthy campaigns that seek long-term access to high-value enterprise assets. Defending against them requires layered detection, rapid response, and resilient architecture. This article shows why combining Extended Detection and Response (XDR) with a 24/7 managed Security Operations Center (SOC) is the practical, modern approach to APT protection. You’ll learn how APTs move through the kill chain, why unified telemetry and automation matter for zero‑day and lateral‑movement detection, and how proactive threat hunting plus Zero Trust reduce dwell time and exfiltration risk.
We map XDR capabilities to lifecycle stages, explain the value a managed SOC brings for continuous monitoring and fast response, and provide vendor-evaluation guidance and procurement checklists. Along the way we cover concrete tactics—network segmentation, supply‑chain controls, and anti‑espionage defenses—and where ShieldWatch XDR and a 24/7 managed SOC fit into an enterprise-grade strategy.
What Are Advanced Persistent Threats and Why Do They Matter for Enterprise Security?
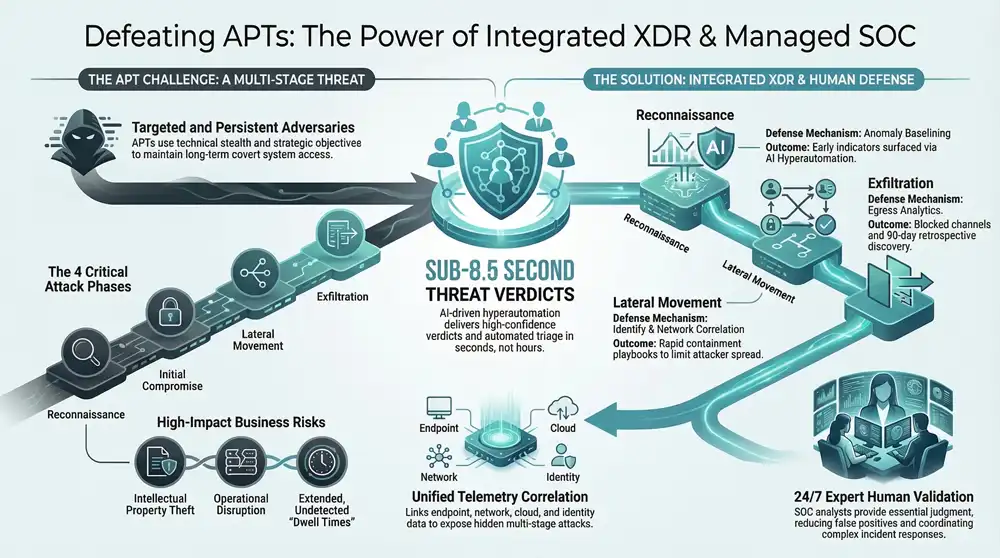
APTs are prolonged, targeted attacks by skilled adversaries that aim to maintain covert access to systems to steal data, monitor activity, or disrupt operations. Their defining trait is persistence: attackers establish footholds, escalate privileges, and move laterally while avoiding detection. Detecting APT activity early reduces dwell time and limits data loss. APTs are distinct from commodity malware because they combine technical stealth with strategic objectives—espionage, intellectual property theft, or long‑term sabotage. Current trends show attackers abusing supply‑chain weaknesses and zero‑day flaws, which raises the need for integrated telemetry and active hunting. Framing the APT threat model makes clear why organizations must prioritize cross‑signal correlation, continuous monitoring, and architecture‑level mitigations for effective defense.
APTs create business impacts that justify investing in advanced controls and specialized staffing. Those impacts drive choices about telemetry, retention, and incident response SLAs—and set up the tactical measures we describe below.
Typical business impacts from APTs include:
- Data theft and loss of intellectual property that erodes competitive advantage.
- Operational disruption and heightened compliance exposure.
- Extended dwell times that enable complex, staged exfiltration.
Those consequences underline why a lifecycle‑focused defense—mapping detection and response to each kill chain stage—is essential for APT protection.
How Do APTs Operate Through Their Lifecycle Stages?
APTs typically move through reconnaissance, initial compromise, persistence, lateral movement, privilege escalation, command & control, exfiltration, and cover‑up. During reconnaissance attackers collect open‑source intelligence and craft spear‑phishing profiles—early signals may look like targeted scanning or unusual email behavior. Initial compromise often uses spear‑phishing or supply‑chain vectors, producing indicators such as anomalous email activity or unexpected binary installs. For persistence and lateral movement, adversaries rely on credential theft and living‑off‑the‑land tools; those activities surface as abnormal authentications, unusual process trees, and unexpected network connections.
Mapping these stages to detection priorities is critical because early signals are subtle but actionable. Alerts that correlate endpoint, identity, and network telemetry reduce missed detections. Lifecycle mapping also informs response playbooks that prioritize quick containment to prevent escalation and exfiltration—an approach we build on when we discuss favored attack vectors and mitigations.
What Are the Common Attack Vectors and Tactics Used by APT Groups?
APTs commonly exploit spear‑phishing, supply‑chain compromise, zero‑day vulnerabilities, misconfigurations, and credential theft to gain and expand access. Spear‑phishing succeeds because it’s tailored to bypass bulk defenses; supply‑chain risks require vendor controls and dependency vetting to block downstream compromise. Zero‑day detection benefits from behavioral baselining, since signature‑based tools often miss novel exploits. Tactics such as lateral movement and living‑off‑the‑land hide malicious activity inside legitimate administrative tools, so detecting horizontal movement depends on correlating identity and endpoint telemetry.
Operational mitigations include enforcing multi‑factor authentication, accelerating patching for high‑risk assets, applying network segmentation, and running continuous monitoring with threat intelligence correlation.
These measures feed detection design: telemetry must cover endpoints, network, cloud, and identity to surface stealthy vectors—exactly why unified telemetry and automated orchestration in XDR strengthen enterprise APT defenses.
How Does XDR Enhance Detection and Response Against Advanced Persistent Threats?
XDR (Extended Detection and Response) strengthens APT defenses by aggregating telemetry from endpoints, network, cloud, and identity, correlating events to reveal multi‑stage attacks, and automating vetted response playbooks to shorten time‑to‑containment. The key is cross‑signal correlation: XDR ingests endpoint, network, cloud, and identity signals and applies analytics that expose the relationships attackers use to move and persist. The result is fewer false positives, faster triage, and measurable reductions in mean time to detect (MTTD) and mean time to respond (MTTR)—all core to effective APT defense.
XDR outperforms siloed EDR or traditional log‑centric systems by delivering context‑rich alerts and orchestration for containment. Correlation improves zero‑day detection through behavioral models and enables proactive threat hunting by retaining long‑term telemetry. Below are the core mechanisms that make XDR effective against stealthy APTs.
- Unified telemetry correlation: Link endpoint, network, cloud, and identity data to expose multi‑stage attacks.
- Automated orchestration and response: Run vetted containment playbooks to shrink exposure windows.
- Retrospective hunting and analytics: Use historical telemetry to detect dormant or slow‑moving threats.
Those mechanisms explain how AI and unified telemetry work together in practice—and how ShieldWatch XDR implements them.
What AI-Driven Features Does ShieldWatch XDR Use for APT Detection?
ShieldWatch XDR applies AI Agent Hyperautomation, behavioral anomaly detection, and automated triage to highlight APT indicators and accelerate analyst workflows while lowering alert noise. Behavioral baselining and periodic model retraining separate benign anomalies from malicious activity, delivering faster, higher‑confidence verdicts for SOC teams. AI‑driven playbooks automate initial containment and build contextualized cases for analysts—enabling sub‑8.5‑second verdicts in high‑confidence automated triage scenarios and escalation when human review is required. For example, an anomalous endpoint process can trigger a model, the platform correlates network egress and identity anomalies, a provisional verdict issues, and a SOC analyst validates and authorizes containment.
That hybrid AI‑plus‑human model keeps analysts in control while scaling triage efficiency, directly reducing dwell time and enabling more effective threat hunts. Next, we explain how unified telemetry supplies the signals that power these AI features.
How Does Unified Telemetry Improve Visibility Across Endpoints, Networks, and Cloud?
Unified telemetry aggregates endpoint, network, cloud, and identity signals into correlated events that reveal cross‑vector attacks single‑signal tools miss. Semantic correlation—linking a suspicious process to unusual network egress or atypical cloud API calls—creates high‑fidelity indicators of compromise, making lateral movement and exfiltration detectable. For example, a process spawning suspicious child processes, paired with an identity logging in from multiple geographies, points to credential compromise and lateral activity and should be prioritized. Unified telemetry also supports historical hunting by preserving a 90‑day activity window for retrospective detection of long‑running persistence.
Operational integrations with telemetry sources and SOAR workflows let orchestration scope containment across clouds and endpoints, while retention and indexing enable fast forensic queries.
This visibility is foundational to comprehensive APT defense and directly informs the role of managed SOC services, discussed next.
Why Are Managed SOC Services Critical for Continuous APT Monitoring and Rapid Incident Response?
A managed SOC delivers 24/7 monitoring, expert validation, and coordinated incident response—capabilities that significantly reduce detection gaps and dwell time for APTs. APTs exploit time windows and subtle signals that need persistent observation and human judgment to validate machine findings. A managed SOC is an operational safety net: continuous monitoring catches off‑hour or slow‑moving attacks, analysts enrich AI alerts with threat intelligence and business context, and the SOC executes containment and escalation workflows aligned to enterprise SLAs. Together, these capabilities shorten detection‑to‑containment timelines and help organizations meet compliance and reporting obligations after incidents.
Beyond alerting, a managed SOC provides runbooks, persistence eradication plans, and post‑incident recommendations that improve future detection sensitivity.
- Continuous monitoring to eliminate blind spots and limit dwell time.
- Human validation and contextual investigation to reduce false positives.
- Coordinated escalation and containment that align to business impact and compliance needs.
Those benefits explain why technical controls should be paired with managed detection and response.
What Is the Role of 24/7 Expert Analysts in APT Defense?
24/7 SOC analysts handle triage, enrichment, deep investigation, and stakeholder coordination to turn alerts into actionable incidents. Human‑in‑the‑loop analysis means analysts validate AI verdicts, correlate threat intelligence, and collect forensics to inform containment and eradication. They also manage escalation to application owners or executives, ensuring containment actions respect business continuity and regulatory requirements. In practice an analyst triages an alert, enriches it with telemetry and intel, models containment scenarios, and then executes or recommends actions while documenting evidence for compliance.
This human judgment is essential in high‑risk APT cases where automated containment might disrupt critical operations—so AI agent hyperautomation must collaborate with SOC teams to balance speed and governance.
How Does AI Agent Hyperautomation Collaborate with Human SOC Teams?
AI agent hyperautomation automates routine triage, evidence collection, and initial containment steps while deferring critical decisions to analysts, creating a hybrid workflow that improves speed without sacrificing governance. Automated playbooks and decision thresholds let high‑confidence detections trigger containment, while lower‑confidence cases escalate to analysts with preassembled case artifacts. This reduces manual toil and shortens MTTR, and governance is preserved through audit trails, playbook versioning, and analyst override controls. For instance, an AI agent may quarantine an endpoint automatically when telemetry and scoring meet thresholds, then notify analysts who review and perform deeper forensics if needed.
These hybrid workflows balance rapid containment with human validation and align directly with enterprise audit and compliance requirements.
What Enterprise Strategies Strengthen APT Protection Beyond Detection and Response?
Strategies that shrink attack surface and limit attacker mobility—Zero Trust, network segmentation, and disciplined vulnerability management—complement detection and response to materially improve APT resilience. Zero Trust enforces least privilege, continuous authentication, and micro‑segmentation to block lateral movement and reduce escalation paths. Network segmentation and micro‑segmentation partition environments so an initial compromise cannot freely reach critical assets. Vulnerability management shortens exploitable windows by prioritizing patches for high‑risk systems. Together these architectural controls raise the cost of attack and narrow the adversary’s operational space.
Operationalizing these strategies requires cross‑team coordination between identity, network, cloud, and security operations and integration with telemetry so XDR can enforce and verify controls. The table below maps strategies to implementation best practices to help prioritize actions.
How Does Implementing Zero Trust Architecture Mitigate APT Risks?
Zero Trust reduces APT risk by replacing implicit trust with continuous verification of identity and device posture, making lateral movement and privilege escalation harder after an initial compromise. Policy enforcement—continuous authentication, device health checks, and contextual access decisions—limits escalation paths and forces attackers to overcome granular controls for each resource. Quick wins include enforcing multi‑factor authentication, applying conditional access for cloud apps, and feeding device telemetry into access decisions. Prioritize high‑value assets and service accounts, and integrate XDR telemetry so security teams can detect policy violations and anomalous access patterns.
A phased rollout with pilot segments and clear remediation SLAs preserves stability while gradually lowering APT risk. Those implementation steps lead into segmentation and vulnerability‑management best practices.
What Are Best Practices for Network Segmentation and Vulnerability Management?
Effective segmentation and vulnerability management pair accurate asset classification, prioritized patching, and monitoring to reduce exposure to APT techniques. The principle is layering controls: segment by function and criticality, apply firewall and host‑based micro‑segmentation rules, and instrument east‑west traffic for anomalies. Vulnerability management should prioritize risks tied to high‑value assets using risk‑based scoring, enforce patch SLAs, and track mean time to patch and exposure windows. Operational metrics—segmentation burn‑down and remediation SLAs—give visibility into risk reduction over time.
Concrete steps include maintaining an up‑to‑date asset inventory, segmenting around sensitive data stores, and integrating vulnerability scanners into the XDR and SOC workflow so critical patches are verified and exceptions monitored. These practices prepare teams to map controls to kill chain stages and vendor capabilities.
The following EAV table translates strategies into implementation practices and tooling examples.
How Does ShieldWatch XDR Address Each Stage of the APT Kill Chain Effectively?
ShieldWatch XDR aligns detection and response controls to each APT kill chain stage by combining unified telemetry, AI‑driven triage, rapid automated verdicts, and historical threat hunting to reduce dwell and contain incidents. Stage‑specific controls look like this: reconnaissance detection via anomaly baselines; initial compromise detection through endpoint and cloud/email correlation; persistence and lateral movement detection using identity and network correlation; and exfiltration detection with egress analytics and behavioral models. Expected outcomes include sub‑8.5‑second threat verdicts on high‑confidence detections, containment actions within minutes in orchestrated workflows, and a 90‑day retention window for retrospective hunting.
The table below maps ShieldWatch capabilities to kill chain stages and expected outcomes.
What Are ShieldWatch’s Capabilities for Rapid Threat Verdicts and Containment?
ShieldWatch drives rapid verdicts and containment with AI scoring, automated SOAR workflows, and pre‑approved containment playbooks that reduce exposure while preserving analyst control. The decision model layers AI Agent Hyperautomation confidence scores with SOAR execution: when thresholds are met, containment runs automatically and analysts receive a full audit trail for review. The tangible result is sub‑8.5‑second verdicts on high‑confidence detections and containment within minutes for common attack patterns—substantially lowering attacker dwell time.
These capabilities preserve governance through playbook versioning and analyst override points, keeping containment aligned with business continuity and priorities.
How Does Historical Threat Hunting Support Proactive APT Defense?
Historical threat hunting uses long‑retention telemetry—ShieldWatch’s 90‑day window—to perform retrospective analysis that uncovers dormant implants, slow persistence, and previously missed indicators. Retrospective correlation re‑evaluates past telemetry with updated rules and threat intelligence to surface latent compromises. Standard hunting workflows include hypothesis development, query searches across endpoint/network/cloud logs, enrichment with threat intel, and actionable findings that drive containment and rule creation. Outcomes include removal of dormant backdoors, strengthened detection rules, and fewer future false negatives.
Retrospective hunting converts retained telemetry into proactive detections and improves detection engineering, complementing real‑time detection and automated response.
How Can Enterprises Evaluate and Select the Right APT Protection Solutions?
When evaluating APT protection, prioritize telemetry breadth, detection latency, automation safeguards, analyst support, integration points, and compliance capabilities. Start with a requirements‑first procurement: define required telemetry sources (endpoint, network, cloud, identity), desired retention windows for hunting, acceptable detection‑to‑verdict and verdict‑to‑containment SLAs, and the analyst engagement model for 24/7 coverage. Operational factors include integrations with existing agents and cloud platforms, the vendor’s SOAR workflow library, and compliance‑ready evidence collection for SOC 2, HIPAA, CMMC 2.0, and ISO 27001 reporting. Use the checklist below during demos and proofs‑of‑concept to compare offerings objectively.
- Does the solution ingest and correlate endpoint, network, cloud, and identity telemetry? Verify depth and native integrations.
- What are typical detection‑to‑verdict and verdict‑to‑containment times? Request measured SLAs or benchmark data.
- How does automation handle false positives and analyst overrides? Confirm governance controls and audit trails.
- What hunting windows and retention do you provide for retrospective detection? Ensure retention meets your hunting needs.
- What analyst access and 24/7 coverage options exist? Validate SOC model, escalation paths, and SLAs.
- Which compliance frameworks does the vendor support for reporting? Confirm evidence collection and reporting templates.
That checklist helps procurement teams compare XDR, EDR, SIEM, and managed SOC combinations. The table below summarizes solution strengths and key vendor questions.
What Are Key Considerations When Comparing XDR, EDR, and SIEM for APT Defense?
Compare XDR, EDR, and SIEM on telemetry scope, correlation power, retention for hunting, detection sophistication, and the operational overhead to run the tool effectively. Coverage is the key differentiator: EDR gives deep endpoint visibility but needs integration for cross‑signal correlation; SIEM centralizes logs but often requires heavy tuning and staffing; XDR is built to combine signals and automate response to reduce operational burden. Consider integration costs, analyst staffing needs, and hidden engineering effort for custom rules. Hybrid approaches—feeding EDR telemetry into XDR or using SIEM alongside XDR alerts—can be pragmatic transition strategies.
The right combination depends on existing investments, staffing capacity, and required SLAs for detection and containment. The next section lists concise vendor questions to surface those details.
Which Questions Should Executive and Technical Buyers Ask Potential Vendors?
- What is your detection‑to‑verdict and verdict‑to‑containment SLA?
- Which telemetry sources do you natively ingest and correlate?
- How many prebuilt SOAR workflows and integrations do you provide?
- What hunting windows and retention do you offer for retrospective analysis?
- How is 24/7 analyst access structured and what escalation paths exist?
Frequently Asked Questions
What are the key differences between XDR and traditional EDR solutions?
XDR (Extended Detection and Response) extends EDR by integrating and correlating data across multiple layers—endpoints, networks, cloud, and identity. EDR focuses on endpoint telemetry and deep forensics; XDR combines those signals for a holistic view of multi‑stage attacks. That cross‑signal correlation improves detection fidelity, reduces false positives, and enables faster, more automated response—important advantages when combating APTs.
How can organizations measure the effectiveness of their APT defense strategies?
Measure effectiveness with KPIs such as mean time to detect (MTTD), mean time to respond (MTTR), number of true incidents versus false positives, and remediation SLAs. Regular pen tests, red‑team exercises, and threat‑hunting campaigns validate controls. Compliance audits and post‑incident reviews also surface operational gaps and improvement opportunities.
What role does threat intelligence play in APT protection?
Threat intelligence informs detection and prioritization by surfacing indicators, TTPs (tactics, techniques, and procedures), and emerging adversary trends. Integrated intel sharpens alert context, helps prioritize hunting and patching, and guides containment choices—turning raw telemetry into actionable investigations.
How often should organizations conduct security assessments for APT vulnerabilities?
At minimum, perform security assessments quarterly; for high‑risk environments or after major infrastructure changes, increase frequency. Regular assessments help find new vulnerabilities, validate controls, and ensure compliance. Also run targeted assessments after incidents or when threat intelligence indicates changing adversary activity.
What are the benefits of integrating AI into APT detection and response?
AI accelerates detection and triage by analyzing large volumes of telemetry, surfacing patterns and anomalies that humans might miss. AI reduces analyst toil through automated evidence collection and playbook execution, shortens verdict times, and improves accuracy when paired with human validation. The right AI design improves operational efficiency without replacing analyst judgment.
How can organizations ensure compliance with regulations while implementing APT defenses?
Align defenses with applicable frameworks (GDPR, HIPAA, PCI DSS, etc.), maintain clear documentation of security policies and incident procedures, and ensure evidence collection meets audit requirements. Regular audits, training, and integrating compliance checks into SOC playbooks make regulatory obligations part of day‑to‑day operations.
Conclusion
Combining XDR with a 24/7 managed SOC gives organizations the telemetry, automation, and expert judgment required to detect, contain, and hunt advanced persistent threats. Unified telemetry and human‑augmented AI shorten dwell time and reduce data‑exfiltration risk while preserving governance and compliance. Strengthening architecture through Zero Trust, segmentation, and disciplined vulnerability management further limits attacker options. If you’re evaluating enterprise APT protections, use the guidance and checklists above to benchmark vendors and prove capability. To learn how ShieldWatch XDR and managed SOC services can fit your environment, explore our solutions or contact our team for a tailored assessment.
**




Unlock exclusive affiliate perks—register now!
Start earning on autopilot—become our affiliate partner!