Rapid XDR deployment means standing up an extended detection and response capability that’s operational and delivering real detection, investigation, and containment in hours — not the weeks or months legacy approaches demand. Shrinking that window reduces exposure, speeds time-to-value, and turns security tools into active business controls almost immediately. This article explains why speed matters in today’s threat landscape, how a focused five‑phase deployment compresses onboarding, and how AI, hyperautomation, and managed SOC practices remove the usual go‑live bottlenecks.
You’ll get a practical five‑phase playbook for accelerated onboarding, a technical look at agentic AI and SOAR workflows, comparisons to SIEM/XDR benchmarks, and an executive view of business benefits and ROI. Where useful, we cite vendor proof points to show rapid XDR is attainable without sacrificing accuracy, compliance readiness, or operational control.
Why Is Rapid XDR Deployment Critical for Modern Cybersecurity?
Rapid XDR deployment is about getting detection, correlation, and automated response running quickly so organizations close gaps and cut attacker dwell time. Speed works because it removes long manual steps — data normalization, tuning, and staffing — letting automated triage and containment start delivering measurable risk reduction immediately. The benefits are tangible: shorter breach windows, lower remediation costs, and immediate visibility across endpoints, network, cloud, and identity. Those outcomes strengthen resilience, improve regulatory posture, and protect business continuity.
Track a few core metrics to measure the impact of deployment speed:
- Faster mean time to detect (MTTD) shortens attacker dwell time and limits lateral movement.
- Lower mean time to respond (MTTR) cuts remediation expense and operational disruption.
- Shorter time to compliance evidence supports audit readiness and reduces regulatory exposure.
Those metrics make clear the business risks of delayed XDR and how accelerated deployment materially reduces them.
What Are the Business Risks of Delayed XDR Implementation?
Delaying XDR adoption lengthens the window attackers can operate undetected, which raises remediation costs and increases business disruption. Without mature detection and correlation, organizations rely on manual forensics, creating longer investigations, higher third‑party bills, and greater reputational risk. Slower evidence collection and fractured logs also complicate audits and breach investigations, driving insurance and regulatory consequences. In short, slow integration compounds operational and compliance risk and elevates executive exposure.
Mitigating those risks requires a deployment approach that emphasizes fast visibility and automated containment from day one. The next section outlines a practical five‑phase method designed to do exactly that and minimize the exposure of slow rollouts.
How Does Fast Deployment Reduce Breach Costs and Risk Exposure?
Faster deployment lowers breach costs by shrinking the time between compromise and containment through earlier detection, automated triage, and immediate containment steps. Early detection reduces the volume and complexity of investigation artifacts, cutting analyst hours and external forensic fees. Automated containment—endpoint isolation, credential revocation, and similar actions—limits lateral movement and reduces data exfiltration, directly lowering financial and reputational impact. Ready access to historical logs shortens investigations by providing retroactive context without long log collection projects.
Those operational efficiencies add up: fewer incident hours, lower third‑party invoices, and less downtime for critical systems. Faster deployment therefore not only reduces technical risk but creates a measurable path to positive security ROI and a stronger executive risk posture. We connect those gains to specific deployment phases below.
What Is the ShieldWatch XDR 5-Phase Deployment Process?
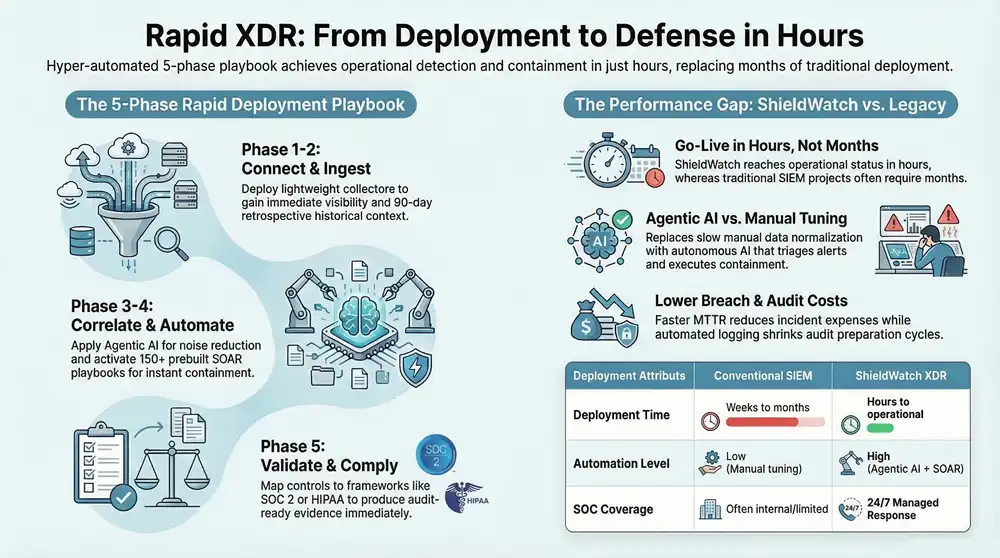
A repeatable five‑phase deployment compresses setup work into parallel tracks so teams reach operational detection and response quickly. The five phases are: 1) Connect, 2) Ingest & Observe, 3) Correlate & Tune, 4) Automate Response, and 5) Validate & Comply. Each phase targets specific technical activities — connectors, collectors, correlation rules, playbooks, and audit‑ready evidence — and combines hands‑on collaboration between customer and provider to deliver incremental time‑to‑value. This structured approach avoids long sequential projects by using default automation and retrospective analysis to enable immediate detection while deeper tuning continues.
Below is a concise breakdown of the five phases and expected outcomes to illustrate how this method supports go‑live in hours.
This phased view shows how overlapping work shortens elapsed time to effective detection. The next section explains the technical choices — connectors, retrospective analysis, and default playbooks — that make onboarding in hours achievable.
How Does Onboarding to Go-Live Happen in Hours?
Getting to go‑live in hours relies on lightweight collectors, preconfigured connectors for endpoints, cloud, and identity, and sensible default tuning that avoids lengthy manual rule creation. Prerequisites are straightforward: enable log forwarding, deploy small agents where required, and grant read‑only access to cloud and identity telemetry. Once collectors stream data, a 90‑day retrospective analysis surfaces historical indicators and context for immediate triage. Default SOAR playbooks and AI‑driven prioritization reduce the need to build bespoke playbooks in the first days.
A brief readiness checklist speeds setup: prioritize log sources, confirm credentials for cloud/identity connectors, and identify SOC escalation contacts. With those items in place, teams move from install to validation quickly, enabling containment actions and alerting within the same operational window.
What Are the Key Steps from Integration to Threat Containment?
Integration to containment follows a tight cycle: onboard data sources, normalize events, correlate incidents with AI prioritization, execute automated playbooks, and route results to human analysts for validation. Coverage includes endpoints, network telemetry, cloud logs, and identity signals — each mapped into correlation pipelines so cross‑domain detection works immediately. Correlation surfaces prioritized incidents and triggers prebuilt playbooks that enrich data, contain affected resources, and create investigation artifacts. Analysts receive concise context and remediation steps, shortening the decision loop and speeding containment.
This automated chain enables containment actions in operational minutes while human analysts supervise and validate outcomes. The approach ensures integration yields protective actions quickly rather than a long tuning cycle and supports ongoing refinement as environment‑specific rules are introduced.
How Does AI and Hyperautomation Accelerate XDR Setup and Response?
AI and hyperautomation speed setup and response by automating triage, enriching alerts, and executing containment with minimal manual work. Agentic AI acts like a digital analyst: it ingests telemetry, correlates multi‑source events, and recommends or executes actions based on confidence thresholds. Hyperautomation links AI decisions to SOAR playbooks so repetitive tasks — enrichment, IOC lookups, asset context gathering, and containment — run automatically, tightening feedback loops and improving accuracy through outcome‑driven learning. The result is faster time‑to‑value and a detection posture that keeps improving over time.
AI‑driven automation reduces manual triage load so human analysts can focus on complex investigations and strategy. The following subsections define agentic AI and show how prebuilt SOAR workflows make these gains repeatable and auditable.
What Is Agentic AI and Its Role in Rapid Deployment?
Agentic AI is an autonomous AI layer that performs analyst‑like tasks — triaging alerts, enriching evidence, and initiating containment — under safety controls and human oversight. In rapid deployment scenarios, agentic AI speeds maturity by applying standard correlation logic, learning from validated outcomes, and lessening the need for manual rule writing. Secure‑by‑design controls — confidence thresholds, human approval gates, and audit trails — reduce AI risk while allowing automated operations to start early. That lowers the initial burden on internal teams and lets detection and response scale from day one.
Paired with retrospective log analysis and prebuilt playbooks, agentic AI delivers prioritized, contextual alerts with recommended containment actions, enabling faster containment with fewer analyst hours than manual triage approaches.
How Do SOAR Workflows Streamline Incident Response?
Prebuilt SOAR workflows turn detection into consistent, auditable actions by chaining detection, enrichment, containment, and ticketing automatically. A typical playbook flow follows detect → enrich → contain → notify, where enrichment adds asset and threat context and containment performs tasks like endpoint isolation or credential revocation. A library of mature, customizable playbooks accelerates time‑to‑value because common scenarios are covered out of the box and only need policy‑level adjustments.
These workflows reduce response variability, cut false positives through enrichment, and produce compliance‑ready logs of actions taken. Customization lets enterprises align playbooks with policy or regulatory needs while keeping the rapid response benefits of automation.
How Does ShieldWatch XDR Compare to Industry Deployment Benchmarks?
Putting platform claims next to industry benchmarks clarifies procurement expectations and timelines. Traditional SIEM projects often run for months because of manual normalization, tuning, and staffing gaps. High‑performing XDR implementations aim for initial detections in hours to days. ShieldWatch XDR positions itself among the fast cohort by combining agentic AI, hyperautomation, retroactive log analysis, prebuilt SOAR playbooks, and 24/7 SOC support to materially compress time‑to‑go‑live and time‑to‑value.
The table below summarizes deployment attributes for a conventional SIEM, a typical XDR, and ShieldWatch XDR to help decision makers evaluate trade‑offs.
This comparison shows how automation and managed SOC support shorten deployment time and improve immediate detection effectiveness. The next section looks at market norms that drive long timelines and what enables elite performers to move faster.
What Are Typical SIEM and XDR Deployment Times?
SIEM deployments often take months because they require extensive data normalization, heavy tuning to reduce noise, and staffing for alert triage. Factors include custom log parsing, complex rule development, and integrating diverse telemetry from endpoints, network devices, cloud services, and identity systems. By contrast, modern XDRs that emphasize connectors, default correlations, and automation can cut elapsed time dramatically — elite implementations reach meaningful coverage in under 24 hours to a week. Operational readiness depends on technology fit and vendor experience executing parallel onboarding tasks.
These benchmarks show why some providers hit rapid go‑live and others don’t: automation, retrospection, and managed SOC involvement are decisive.
How Does ShieldWatch Achieve Go-Live in Hours Versus Weeks?
ShieldWatch reaches accelerated go‑live through autonomous AI, extensive prebuilt automation, and SOC‑assisted onboarding. Key capabilities include rapid deployment to operational status in hours, 90‑day retroactive log analysis for immediate historical context, an agentic AI layer acting as a digital analyst, and a library of 150+ prebuilt SOAR workflows that automate common responses. Paired with 24/7 SOC monitoring, these elements reduce the need for long tuning cycles and staffing ramps, enabling containment and verdicting workflows to run in operational minutes rather than after protracted setup.
Those proof points illustrate how automation, retrospective visibility, and continuous human‑AI partnership create a measurable gap between conventional deployments and accelerated XDR go‑lives.
What Are the Business Benefits of Fast XDR Implementation for Executives?
Fast XDR implementation turns technical speed into executive outcomes: lower breach costs, improved compliance readiness, and reduced operational burden. Executives see faster demonstration of security value through shorter detection times and fewer incident hours charged to the business. Accelerated XDR also shrinks the timeline for gathering compliance evidence and remediating control gaps, lowering audit risk and helping close deals with regulated customers. Finally, quicker deployment enables predictable SLAs and clearer resource planning for CIOs and CISOs.
To make benefits actionable, the table below maps business gains to measurable mechanisms and executive outcomes.
This mapping helps executives prioritize investments that produce measurable improvements in risk, cost, and predictability. The next sections explain ROI and leadership perspectives on accelerated XDR adoption.
How Does Rapid Deployment Improve ROI and Compliance Readiness?
Rapid deployment improves ROI by turning security tooling into actionable controls quickly, shortening the time between purchase and measurable risk reduction. Faster detection and automated containment reduce investigation hours and third‑party remediation fees, delivering direct cost savings. On compliance, immediate log availability and mapped control evidence accelerate audit responses for SOC 2, HIPAA, CMMC 2.0, and ISO 27001, cutting audit prep time and enabling faster certification cycles. These effects deliver both near‑term cost avoidance and longer‑term risk reduction.
Overall, accelerated XDR moves projects from cost centers toward demonstrable risk management investments, letting leadership justify spending with clear timelines and measurable metrics.
Why Do CIOs, CISOs, and MSPs Prefer Accelerated XDR Solutions?
CIOs, CISOs, and MSPs choose accelerated XDR because it simplifies operations, enables predictable service delivery, and shortens the feedback loop for measurable security outcomes. Faster implementations let MSPs onboard more customers without proportional staffing increases, while internal teams avoid hiring large analyst pools for manual triage. Predictable SLAs and automated playbooks make it easier to report security posture to stakeholders and show continuous improvement. For decision makers, speed equals reduced exposure and faster returns on security investments.
Those leadership priorities explain the growing demand for platforms and service models that emphasize rapid deployment, automation, and managed SOC partnership.
How Can Managed XDR Services Ensure Fast Deployment and Continuous Protection?
Managed XDR combines technology, playbooks, and human analysts to accelerate deployment while maintaining continuous protection. The managed model shifts connector management, tuning, and analyst staffing to a provider operating 24/7, letting organizations start with strong protection and adopt a shared operating model. Typical service components include onboarding, continuous monitoring, threat hunting, incident response, and compliance reporting — all orchestrated to minimize customer operational burden. This service model turns platform capabilities into operational outcomes without requiring the customer to build and staff a mature SOC.
What Is the Role of 24/7 SOC Monitoring in Rapid XDR Go-Live?
24/7 SOC monitoring adds human validation, escalation, and proactive threat hunting during the critical early days of deployment, reducing false positives and speeding containment. Analysts work with AI prioritization to validate alerts, tune playbooks, and confirm containment actions, ensuring automated responses operate safely. Continuous coverage guarantees incidents detected during onboarding are acted on immediately, avoiding overnight gaps. The human+AI partnership shortens the learning curve and raises confidence that rapid deployment delivers dependable protection.
The SOC’s role is operational — executing escalations and containment — and strategic — feeding validated outcomes back into automation to improve future detection.
How Do Managed Services Reduce Operational Burden and Speed Setup?
Managed providers cover the repetitive parts of XDR deployment: installing connectors, normalizing data, applying default correlations, and tuning playbooks, which cuts internal labor and speeds time‑to‑maturity. By owning analyst staffing and escalation processes, managed services let customers avoid hiring large SOC teams and deliver services with predictable SLAs. A clear division‑of‑responsibility checklist clarifies what the managed provider handles versus what the customer retains: providers manage integration, monitoring, and initial containment, while customers retain policy approval and final remediation decisions.
ShieldWatch pairs an autonomous platform — agentic AI, 150+ prebuilt SOAR workflows, and 90‑day retrospective analysis — with 24/7 SOC services to accelerate go‑live and sustain protection through continuous optimization. That managed approach reduces time‑to‑value and operational overhead while keeping executives in control of policy and compliance.
- Provider responsibilities include: connector deployment, playbook activation, continuous monitoring, and initial containment actions.
- Customer responsibilities include: policy approval, escalation contacts, and final remediation decisions.
- Operational result: predictable, rapid onboarding and ongoing improvement without a large internal SOC.
This division ensures customers see protective actions and audit artifacts quickly while the provider optimizes detections and playbooks in production. ShieldWatch’s managed model shows how tight integration between automation and staffed SOC services delivers accelerated, continuous protection.
To see how an enterprise‑grade platform combining autonomous AI, hyperautomation, and 24/7 SOC services accelerates XDR deployment and time‑to‑value, contact ShieldWatch for a demo or consultation.
Frequently Asked Questions
What types of organizations benefit most from rapid XDR deployment?
Organizations with high cyber risk — finance, healthcare, critical infrastructure, and other regulated industries — gain the most from rapid XDR. These sectors handle sensitive data and face strict rules, so quick detection and response matter. Smaller IT teams and fast‑growing businesses also benefit: rapid XDR delivers strong protection without heavy hiring or long implementation timelines.
How does rapid XDR deployment impact compliance with regulations?
Rapid XDR improves compliance by providing immediate visibility and faster evidence collection for audits. Automated logging and reporting make it easier to demonstrate controls for frameworks like HIPAA, SOC 2, and ISO 27001. That reduces audit preparation time, lowers regulatory risk, and protects reputation and finances.
What role does training play in the successful implementation of rapid XDR?
Training is essential. Effective programs ensure teams know how to use automation, interpret alerts, and run incident response protocols. Well‑scoped training accelerates adoption, shortens time‑to‑value, and helps teams get the most from automated features and playbooks.
Can rapid XDR deployment be integrated with existing security tools?
Yes. Rapid XDR is designed to interoperate with existing security investments — SIEMs, endpoint protection, cloud tooling, and more. Integration lets organizations keep what works while adding advanced detection and response across domains, creating a more cohesive security stack.
What are the common challenges organizations face during rapid XDR deployment?
Common challenges include change resistance, legacy integration issues, and the need for adequate training. Data normalization and ensuring all telemetry sources are connected can also be hurdles. Overcoming these challenges requires a clear deployment plan, early stakeholder engagement, and targeted training so teams are ready to operate the new system effectively.
How does the cost of rapid XDR deployment compare to traditional methods?
While initial costs vary by vendor and scope, rapid XDR often delivers lower total cost of ownership over time. Automation reduces implementation and operating effort, faster detection cuts remediation fees, and improved compliance lowers audit and regulatory costs. Those savings can make rapid XDR more cost‑effective than traditional, manual approaches.
Conclusion
Rapid XDR deployment gives organizations a practical way to reduce breach costs and improve compliance readiness by turning security investments into active controls in hours rather than weeks. By combining automation with 24/7 SOC support, teams get operational protection fast while keeping policy and compliance under executive control. If you want to see how ShieldWatch can accelerate your XDR journey and deliver measurable time‑to‑value, request a demo or consultation today.




Join our affiliate program and start earning commissions today—sign up now!
Join our affiliate community and maximize your profits!
Promote our products—get paid for every sale you generate!
Sign up for our affiliate program and watch your earnings grow!
Promote our products—get paid for every sale you generate!
Earn up to 40% commission per sale—join our affiliate program now!
Refer and earn up to 50% commission—join now!