Alert fatigue happens when security teams receive more signals than they can meaningfully investigate — producing false positives, missed detections, and burned‑out analysts. At its root, alert fatigue is a signal‑to‑noise problem driven by scale: excessive telemetry, low‑fidelity rules, and fragmented context overwhelm both people and automation. Fixing alert fatigue improves SOC performance by shortening mean time to respond (MTTR), freeing analyst capacity, and lowering business risk. This guide explains the drivers of alert overload, shows how AI and automation reshape triage, explains why XDR cuts duplicate noise, and shares practical SOC practices that reclaim analyst time.
You’ll find actionable playbooks, examples of agentic AI and SOAR‑driven hyper‑automation, and a clear view of how ShieldWatch XDR and our managed SOC services deliver measurable outcomes. Throughout, we emphasize risk‑based prioritization, contextual enrichment, and unified telemetry as durable levers for alert management and SOC efficiency gains.
What is Alert Fatigue and How Does It Impact SOC Operations?
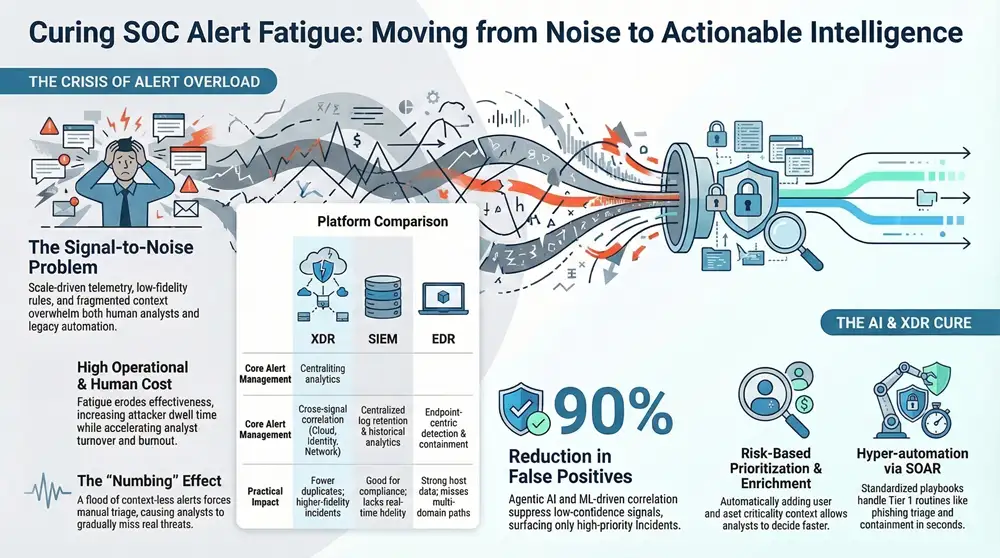
Alert fatigue is the gradual numbing of analysts caused by a flood of low‑value alerts that mask real threats. It starts when tools produce alerts without adequate context or correlation, forcing manual triage and repeated verification that slows response. The payoff from tackling alert fatigue is clearer signal — investigations finish faster and true incidents are less likely to be missed. Understanding root causes and operational effects helps SOC leaders choose where to intervene first to restore analyst focus and improve detection fidelity. The sections that follow break down common causes and the concrete operational and business impacts so teams can prioritize remediation.
What Causes Alert Overload in Security Operations Centers?
Alert overload comes from a mix of technical, process, and human factors that compound as telemetry scales. Technical sources include raw telemetry noise, overlapping rules across endpoint and network sensors, and brittle signatures that fire on benign activity. Process gaps — infrequent rule tuning, missing enrichment pipelines, and isolated escalation playbooks — turn manageable alerts into backlog. Human factors like understaffing, poor handoffs, and inadequate analyst tooling amplify fatigue and error rates. Fixing this requires both architectural consolidation and disciplined processes, which sets the stage for how automation and AI can reduce noise and speed triage.
How Does Alert Fatigue Affect SOC Analysts and Business Security?
Alert fatigue erodes analyst effectiveness by increasing cognitive load, raising mistakes, and accelerating turnover — all of which raise operational risk and costs. Overwhelmed analysts spend more time on repetitive triage and less on deep investigation or hunting, which lengthens MTTR and increases attacker dwell time. For the business, that means higher chances of missed breaches, regulatory exposure, and greater containment expenses. Bringing alert volumes back to manageable levels improves retention, preserves institutional knowledge, and strengthens compliance — so successful mitigation blends technical fixes with workforce support to sustain gains.
How Can AI and Automation Reduce Cybersecurity Alert Fatigue?

AI and automation attack alert fatigue by raising alert fidelity, adding context, and automating repetitive tasks so analysts focus on true risk. Machine learning models spot patterns across telemetry to suppress low‑confidence signals and surface correlated events with higher precision, cutting false positives. Contextual enrichment — adding user behavior, asset criticality, and threat intelligence — turns raw alerts into actionable incidents and enables risk‑based prioritization. SOAR playbooks automate Tier 1 routines (IOC enrichment, quarantine, evidence collection), accelerating response while preserving human oversight. Combined, these layers shrink volume and increase the operational value of what remains.
What Role Does Agentic AI Play in Autonomous Threat Triage?
Agentic AI describes autonomous agents that perform fast triage, enrichment, and controlled containment within defined governance limits. Practically, these agents ingest multiple signals, run ML verdict models, and either recommend or execute preapproved responses when confidence thresholds are met, delivering verdicts in seconds. Governance matters: human‑in‑the‑loop and human‑on‑the‑loop controls define thresholds, audit trails, and rollback options to balance speed with safety. Properly configured, agentic AI can eliminate many routine analyst touches while escalating uncertain cases for human review, streamlining workload and boosting throughput.
How Do Hyper-automation and SOAR Workflows Streamline SOC Operations?
Hyper‑automation uses orchestration and SOAR playbooks to stitch tools together and remove manual steps from common incident paths, creating fast, repeatable responses. Typical automated workflows include phishing triage (extract indicators, validate sender reputation, isolate accounts), IOC enrichment (query threat feeds and asset context), and automated containment for high‑confidence malware. Playbooks reduce investigation time, cut analyst touches, and produce standardized logs for post‑incident review and compliance. Best practice: version and test playbooks in staging so automation augments analyst judgment and escalation routes stay clear.
Why Use XDR Platforms for Efficient Alert Management in SOCs?

XDR platforms provide unified telemetry, cross‑signal correlation, and built‑in response capabilities that cut duplicated alerts and improve incident fidelity. Architecturally, XDR ingests endpoint, network, cloud, and identity signals, normalizes them, and correlates events into higher‑confidence incidents — reducing noise and speeding root‑cause analysis. Consolidating correlation and response shortens the detection‑to‑containment loop and enables automated containment where appropriate. The table below contrasts XDR with traditional SIEM and EDR approaches for alert management and automation.
Because XDR correlates signals that would otherwise appear as separate low‑confidence alerts, it reduces false positives and surfaces multi‑stage incidents. The following section explains how XDR achieves unified visibility and why pairing SIEM and SOAR with XDR yields operational synergy.
How Does XDR Provide Unified Visibility Across Endpoints, Networks, and Cloud?
XDR delivers unified visibility by ingesting diverse telemetry, applying normalization and semantic mapping, then correlating events into contextual incidents for triage. Typical sources include endpoint agents, network sensors, cloud logs, identity/auth events, and threat feeds that together reveal attacker behavior across stages. Correlation engines link events — for example, a suspicious login followed by anomalous process activity — to surface multi‑stage incidents with higher confidence. That reduces time analysts spend stitching evidence and increases time validating and containing confirmed threats, shortening MTTR and enabling proactive hunting.
What Are the Benefits of Integrating SIEM and SOAR with XDR?
Integrating SIEM and SOAR with XDR yields a complete detection‑investigation‑response stack: SIEM provides long‑term retention and compliance, XDR supplies cross‑signal detection, and SOAR brings orchestration and automation. Detection: XDR raises alert fidelity through correlation. Investigation: SIEM retains historical logs for forensic queries. Response: SOAR automates repetitive remediation and creates auditable action trails. Together they reduce false positives, standardize workflows, and simplify reporting for auditors and executives — producing measurable gains in analyst productivity, incident consistency, and regulatory readiness.
What Are Best Practices to Optimize SOC Efficiency and Combat Alert Fatigue?
Optimizing a SOC blends tuning, prioritized alerting, enrichment, automation, and proactive hunting to reduce noise and improve outcomes. Begin with risk‑based alert prioritization that weights asset criticality, user context, and business impact. Build enrichment pipelines that attach identity, vulnerability, and threat‑intel context to alerts so triage is faster and more decisive. Maintain SOAR playbooks for repetitive tasks and invest in regular hunting cadences to expose patterns that evade rules. The table below maps specific practices to expected SOC outcomes to guide prioritization and KPI selection.
Mapping practices to outcomes clarifies which changes deliver the biggest operational improvements and highlights the KPIs SOCs should track. The following subsections translate prioritization and hunting tactics into actionable steps.
How Can Security Alert Prioritization and Contextual Enrichment Improve Analyst Focus?
Prioritization and enrichment convert raw alerts into risk‑scored incidents that are actionable on first glance. A robust model combines signal confidence, asset criticality, patch and vulnerability status, and user‑behavior anomalies to produce a composite risk score that drives triage order. Enrichment fields — asset owner, recent patch state, geolocation, and threat‑intel confidence — let analysts assess impact without jumping between tools. Implementing these elements reduces average triage time and focuses analyst effort on incidents with the highest business impact, enabling more precise automation and hunting.
What Proactive Threat Hunting Strategies Enhance SOC Performance?
Proactive hunting augments alert‑driven work by testing hypotheses across telemetry to find attacker activity before alerts fire. Effective hunting frameworks use MITRE ATT&CK mappings, prioritized hypotheses (for example, lateral movement in privileged subnets), and scheduled cadences for endpoint, network, and cloud reviews. Hunters build queries that correlate unusual sequences, validate suspicious findings with enrichment sources, and feed results back into detection rules and SOAR playbooks. Regular hunting lowers surprise incidents, sharpens detection logic, and shifts the SOC from reactive triage to anticipatory defense.
How Does ShieldWatch XDR Address Alert Fatigue and Improve SOC Operations?
ShieldWatch XDR combines agentic AI, hyper‑automation, and managed SOC services to cut false positives and compress investigation cycles. The platform unifies telemetry ingestion, applies ML‑driven correlation, and offers a broad SOAR workflow library to scale verdicting and enrichment. ShieldWatch frames the solution as an autonomous cybersecurity platform that pairs AI‑driven triage with 24/7 SOC expertise to reduce noise and accelerate containment. The table below maps ShieldWatch capabilities to business impact so teams can see how features translate to operational outcomes.
This mapping shows how specific components — ML correlation, automation, and managed services — produce measurable SOC improvements and help meet compliance obligations. The H3 sections that follow describe feature mechanics and service delivery in more detail.
What Features Enable ShieldWatch XDR to Reduce False Positives by Up to 90%?
ShieldWatch reduces false positives by combining ML correlation across domains, threat‑intel enrichment to validate indicators, and automated deduplication and verdicting that suppress repeat noise. Agentic AI enforces confidence thresholds and contextual checks before issuing automated actions, while the correlation engine consolidates events that would otherwise trigger separate low‑fidelity alerts. Retrospective analysis re‑evaluates historical logs to reveal latent patterns and improve detection rules over time. Together, these mechanisms raise incident fidelity and minimize noisy alerts that waste analyst time.
How Do Managed SOC Services by ShieldWatch Support 24/7 Monitoring and Analyst Burnout Reduction?
ShieldWatch’s managed SOC model pairs continuous monitoring with analyst augmentation and clear escalation ownership to reduce the load on internal teams. High‑confidence incidents are handled immediately; lower‑confidence events receive automated triage, with joint escalation for complex cases. This approach cuts the number of after‑hours alerts requiring internal attention, lowers burnout, and lets organizations scale coverage without linear headcount increases. Operational learnings from the managed service also feed back into detection tuning and playbook refinement, reinforcing long‑term SOC efficiency.
What Business Benefits Do CIOs, CISOs, and MSP Owners Gain from Combating Alert Fatigue?
Addressing alert fatigue delivers executive‑level benefits: reduced breach risk, higher operational ROI, and easier compliance reporting. Cutting false positives and automating routine responses shortens MTTR, which lowers potential breach impact and remediation costs. ROI shows up as fewer analyst hours per incident, less reliance on temporary staffing, and faster incident closure — all measurable reductions to security operations TCO. Unified platforms and managed services also simplify audit prep and continuous compliance, reducing the effort required for regulatory reporting. The list below summarizes primary business advantages for decision‑makers considering alert‑fatigue investments.
- Lowered Risk Exposure: Faster detection and containment limit attacker dwell time and potential breach costs.
- Improved Operational ROI: Reduced analyst hours and automated workflows lower operational expenses.
- Stronger Compliance Posture: Consolidated logging and reporting streamline audits and continuous monitoring.
- Better Workforce Retention: Less burnout improves analyst retention and preserves institutional expertise.
These outcomes link operational changes to financial and governance results, helping leaders prioritize investments that deliver measurable returns.
How Does Reducing Alert Fatigue Improve Risk Management and ROI?
Reducing alert fatigue improves risk management by lowering MTTR and increasing the chance that true incidents are detected and contained quickly. Faster containment limits lateral movement and data exfiltration, directly cutting business impact and the risk of regulatory penalties. ROI shows up as fewer investigation hours, lower contractor costs during spikes, and less need for redundant tooling. Presenting metrics — MTTR improvements, analyst touches saved, and false‑positive reduction — helps CIOs and CISOs justify security investments with concrete cost‑avoidance figures and board‑ready KPIs.
How Does Compliance Readiness with ShieldWatch XDR Streamline Security Reporting?
ShieldWatch XDR supports compliance readiness by consolidating telemetry, preserving historical logs, and producing standardized reports aligned to frameworks such as SOC 2, HIPAA, CMMC 2.0, and ISO 27001. Continuous monitoring and automated evidence collection reduce manual audit prep and demonstrate control effectiveness over time. Built‑in report templates and retained 90‑day retrospective visibility simplify incident timelines and audit trails for assessors. Together, these features cut compliance workload and shorten audit cycles so security and compliance teams can focus on strategic control improvements instead of manual report assembly.
Conclusion
Reducing alert fatigue is central to running an effective SOC: clearer signals mean faster investigations and fewer missed incidents. By combining AI‑driven triage, risk‑based prioritization, enrichment, and automation, organizations can substantially cut false positives and restore analyst focus. Those changes lower operational risk, simplify compliance, and improve workforce retention. Learn how ShieldWatch’s platform and managed SOC services can help you reclaim analyst time and measurably improve SOC outcomes.



Earn recurring commissions with each referral—enroll today!
Share our products, reap the rewards—apply to our affiliate program!
Your audience, your profits—become an affiliate today!
Start earning passive income—become our affiliate partner!
Start earning on autopilot—become our affiliate partner!
Join our affiliate community and earn more—register now!
Partner with us and enjoy high payouts—apply now!
Partner with us and enjoy high payouts—apply now!
Drive sales and watch your affiliate earnings soar!
Join our affiliate community and maximize your profits—sign up now!