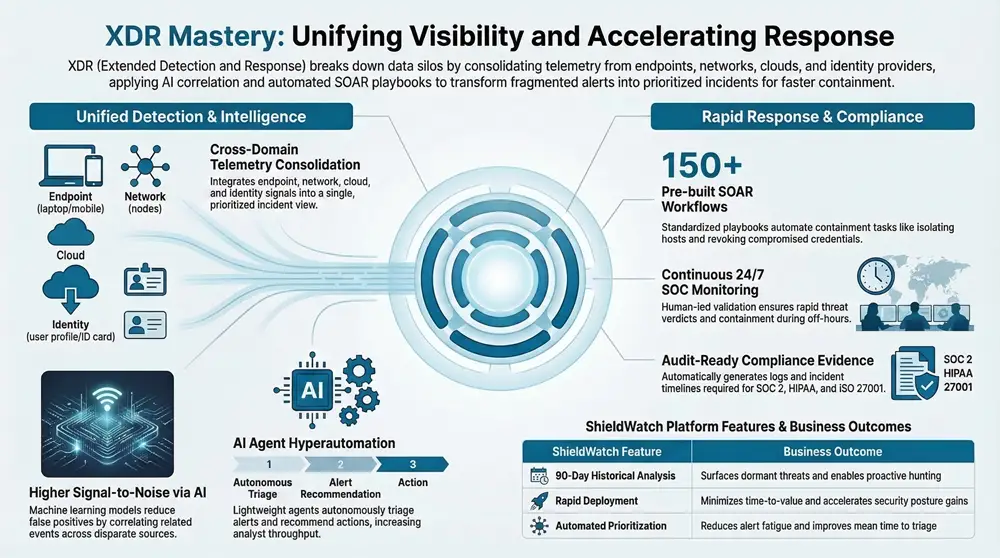
Extended Detection and Response (XDR) brings telemetry, correlation, and automated response together across endpoints, network, cloud, and identity so organizations detect and contain threats faster. As attackers use multi-vector campaigns and tool sprawl fragments visibility, XDR closes gaps with consolidated telemetry, contextualized alerts, and integrated playbooks that shorten decision loops. This article walks through how XDR creates unified visibility, how AI/ML improves detection fidelity, and how automation plus human-led SOC operations speed containment and lower business risk. You’ll get clear trade-offs between XDR, EDR, and SIEM, learn where SOAR and continuous monitoring fit, and see how XDR reduces alert fatigue, supports threat hunting, and helps satisfy compliance requirements.
Throughout, we connect telemetry sources, analytic methods, and orchestration to measurable outcomes security leaders can track—better signal-to-noise, faster time-to-triage, and quicker containment.
What Is Extended Detection and Response and Why Is It Essential for Modern Cybersecurity?
XDR is a detection-and-response architecture that pulls telemetry from multiple domains, correlates signals, and automates containment so teams can close investigations faster. It’s designed to cut through tool sprawl and data silos that hide links between an endpoint alert and concurrent identity or cloud anomalies. The approach is straightforward: collect endpoint, network, cloud, and identity telemetry, enrich events with context, and surface prioritized incidents so analysts act on what matters. That unified workflow drives measurable gains—fewer false positives, shorter time-to-detect, and consolidated operations—making XDR a practical necessity for organizations facing multi-stage, cross-domain threats.
ShieldWatch XDR implements these principles for mid-market and enterprise customers by combining cloud-native telemetry coverage with operational integrations and managed services. We pair telemetry consolidation with hands-on operational support so teams translate detection into fast, effective response without rebuilding internal SOC capacity. That vendor context helps show how XDR capabilities map directly to business outcomes like reduced exposure and smoother SOC workflows.
How Does XDR Provide Unified Security Visibility Across Endpoints, Networks, Cloud, and Identity?
Unified visibility starts by ingesting diverse telemetry—endpoint agents, network flows, cloud logs, and identity events—and then using correlation and enrichment to join related activity into single incidents. Correlation-first logic links disparate alerts when they share attributes such as IPs, user accounts, or process ancestry, producing cross-domain incidents that reveal attack chains. For example: a compromised cloud credential that spins up a suspicious VM while an endpoint shows lateral movement becomes a single, high-priority incident when those signals are correlated. That cross-source linkage improves detection fidelity and gives responders context like asset criticality and user role to guide decisions.
To make this concrete, common telemetry sources that feed an XDR pipeline include:
- Endpoint telemetry: Process launches, file changes, sensor logs, and runtime behavior that show what’s happening on the device.
- Network telemetry: Flow logs, proxy events, and DNS lookups that reveal lateral movement and command-and-control channels.
- Cloud telemetry: API calls, configuration changes, and resource provisioning that expose suspicious activity in cloud environments.
- Identity telemetry: Authentication anomalies, privilege escalations, and risky logins that signal compromised credentials.
When combined, these streams produce a single, prioritized incident that reduces analyst overhead and feeds directly into automated or human-led containment actions.
What Are the Differences Between XDR, EDR, and SIEM Solutions?
XDR, EDR, and SIEM cover overlapping needs but serve different priorities. EDR (Endpoint Detection and Response) delivers deep endpoint telemetry and host-level remediation—excellent for forensic detail on a single machine but limited for cross-domain correlation. SIEM (Security Information and Event Management) centralizes logs, supports compliance reporting, and enables custom rules but often needs significant tuning and engineering to reach high detection fidelity. XDR blends the strengths of both: it ingests endpoint data like an EDR, centralizes and correlates like a SIEM, and adds built-in automation and analytics to reduce manual investigation work.
Use these criteria to choose the right mix:
- Detection scope: Pick XDR for cross-domain detection; choose EDR when deep host forensics are the priority.
- Operational maturity: Favor SIEM when audit reporting and custom correlation rules are required alongside active response capabilities.
- Automation needs: Opt for XDR if you need integrated triage and response to lower SOC load and MTTR.
Viewed this way, many organizations adopt XDR as a consolidation layer that complements—rather than replaces—existing EDR and SIEM investments.
How Does XDR Enhance Threat Detection Using AI and Machine Learning?
XDR leverages AI and machine learning to correlate signals, spot anomalies, and prioritize alerts so analysts focus on high-confidence incidents instead of noise. Typical techniques include supervised models for known malware indicators, unsupervised anomaly detection for novel behavior, and correlation algorithms that join events across telemetry to surface multi-stage attacks. The practical outcome is a higher signal-to-noise ratio, earlier detection of sophisticated threats, and prioritized queues that guide analyst attention where it makes the biggest difference—fewer daily alerts, faster triage, and better detection of stealthy campaigns single-source tools miss.
Below is a concise mapping of common AI/ML techniques used in XDR, how they work, and the detection impact.
This table shows how specific AI/ML methods translate into detection outcomes:
Combining these approaches produces complementary improvements in detection fidelity and more actionable prioritization.
In What Ways Does AI Agent Hyperautomation Improve Alert Triaging and Threat Identification?
AI Agent Hyperautomation refers to agent-like automation that autonomously triages alerts, recommends actions, and learns from analyst validation. Practically, hyperautomation chains lightweight agents to gather context, perform enrichment lookups, score incidents, and either execute safe containment or present a recommended play to an analyst. That flow—automated triage → recommended action → human validation → learning loop—removes repetitive investigative steps while keeping analysts in control. The result: higher analyst throughput and shorter time-to-verdict.
On the ShieldWatch platform we apply these agentic workflows to alert triage and continuously learn from outcomes so recommendations get more accurate over time. The effect is faster containment and improved automation precision without sacrificing analyst oversight.
How Does XDR Detect Sophisticated Threats and Reduce False Positives?
XDR finds sophisticated threats by combining contextual scoring, cross-source correlation, and ensemble ML models that weigh evidence across telemetry before surfacing incidents. Each alert is enriched with user, asset, and historical context to compute a risk score; only incidents above confidence thresholds are elevated for immediate action. For example, a suspicious process on an endpoint that would be low priority alone becomes critical when paired with anomalous cloud provisioning and an atypical login from a new IP. This multi-factor correlation cuts false positives while ensuring stealthy campaigns are captured.
Fewer false positives mean analysts spend less time triaging noise and more time resolving real incidents—improving key metrics like mean time to triage and mean time to remediation.
How Does XDR Accelerate Incident Response and Containment?
XDR speeds response by orchestrating automated playbooks, enabling rapid containment actions, and presenting enriched incident context that shortens analyst decision cycles. SOAR-style automation handles routine containment steps while clear escalation paths bring humans into the loop for complex judgment calls. Continuous monitoring plus integrated playbooks translate detection into response—isolating hosts, revoking credentials, or blocking network paths—so organizations shorten dwell time and limit lateral movement. The net effect is lower business risk and a measurable reduction in mean time to respond (MTTR).
Connecting detection to response at machine speed is especially effective when combined with managed services that provide 24/7 coverage and rapid verdicting to maintain continuous protection.
What Role Do SOAR Workflows Play in Automating and Scaling Incident Response?
SOAR workflows automate and orchestrate common response actions so teams can scale remediation without repeating manual steps. Pre-built playbooks codify proven containment patterns—isolating compromised hosts, blocking malicious IPs, or revoking risky credentials—and include safeguards and escalation logic. Using pre-built workflows shortens deployment time for new response patterns and lets SOCs execute containment in minutes instead of hours, increasing capacity without a linear staffing increase.
Common automated actions include:
- Isolate infected hosts: Remove or restrict network access to halt lateral movement.
- Block malicious indicators: Add IPs, domains, or hashes to enforcement lists across controls.
- Revoke or reset credentials: Restrict access for compromised accounts until the investigation completes.
How Does 24/7 SOC Monitoring Support Rapid Threat Verdicts and Containment?
A 24/7 SOC pairs continuous automated detection with human validation to deliver round-the-clock verdicting and fast containment, shrinking attack windows. The hybrid model runs high-confidence automated actions through SOAR playbooks while routing ambiguous cases to on-duty analysts for rapid review. That continuous vigilance ensures suspicious activity is addressed immediately rather than waiting for business hours, significantly reducing potential impact.
In practice, faster verdicting and containment limit lateral spread and data exfiltration, materially lowering business risk. ShieldWatch’s managed 24/7 SOC combines automation with human oversight and operational metrics that include sub-8.5 second threat verdicts and containment actions executed within minutes—demonstrating how continuous monitoring shortens the detection-to-remediation timeline.
What Are the Core Advantages of XDR in Reducing Alert Fatigue and Improving SOC Efficiency?
XDR combats alert fatigue by consolidating duplicate signals, enriching alerts with context, and routing only prioritized incidents to analysts. The core mechanisms—deduplication, enrichment, and prioritization—merge similar alerts, append threat intelligence and asset context, and rank incidents so analysts focus on the highest business impact cases. That shift boosts SOC throughput, reduces burnout, and frees time for proactive tasks like threat hunting. Measuring impact with KPIs—alerts per analyst per day, false positive rate, and mean time to containment—quantifies those efficiency gains.
The following table compares core platform features to operational outcomes to illustrate these advantages.
How Does AI-Driven Analytics Minimize False Positives and Enhance Analyst Productivity?
AI-driven analytics cut false positives by combining ensemble models, contextual enrichment, and historical baselining to surface only events with corroborating evidence across telemetry. Prioritization yields a ranked queue with root-cause cues and suggested containment steps, accelerating investigations and lowering cognitive load. Analysts receive richer, action-oriented alerts that explain the “why” and the “next step,” enabling a single investigator to close more incidents in the same time window. Tracking KPIs—alerts per analyst, false-positive rate, and time-to-triage—helps quantify productivity gains and guide tuning.
By fusing multiple signals into a single risk score, XDR lets SOCs spend less time validating noise and more time hunting adversaries and strengthening defenses.
What Impact Does XDR Have on Proactive Threat Hunting and Prevention?
XDR powers proactive threat hunting with centralized, normalized telemetry and fast historical analysis that support hypothesis-driven investigations and control hardening. Hunters craft hypotheses—such as “look for atypical privileged credential use over the last 30 days”—and query indexed telemetry across endpoints, cloud logs, and identity events. Retroactive analysis uncovers dormant indicators and informs preventive controls; for example, a 90-day retrospective can reveal compromised accounts active before detection capabilities were in place, enabling containment and policy changes to prevent recurrence.
Proactive hunting closes the loop from detection to prevention: findings feed back into detection rules, SOAR playbooks, and access policies to harden the environment against similar attacks.
At the heart of effective hunting is historical visibility—the ability to search past telemetry quickly increases the chance of finding root causes and latent compromises that would otherwise remain hidden.
How Does XDR Support Compliance Readiness and Governance for Regulatory Frameworks?
XDR supports compliance by collecting and retaining the telemetry and evidence auditors expect, offering automated reporting, and mapping detection and response controls to regulatory requirements. Continuous monitoring produces incident logs, triage notes, and response artifacts that serve as audit evidence for frameworks such as SOC 2, HIPAA, CMMC 2.0, and ISO 27001. Automated report generation and role-based access to forensic evidence simplify audit prep and reduce manual effort. By linking operational controls to compliance objectives, XDR helps organizations demonstrate effective monitoring and incident response during assessments.
Before detailing specific standards, here are common audit artifacts XDR systems produce and how they map to evidence requirements.
Common compliance artifacts produced by XDR include:
- Incident logs: Chronological records of detections and actions taken.
- Triage and investigation notes: Analyst observations and rationale for decisions.
- Containment action records: Execution details from automated playbooks.
- Retention and access logs: Proof of log retention and controlled access to evidence.
Which Compliance Standards Does ShieldWatch XDR Address?
ShieldWatch XDR supports readiness for SOC 2, HIPAA, CMMC 2.0, and ISO 27001 by delivering continuous monitoring, secure logging, and reporting features that align with common control objectives in these frameworks. The platform’s telemetry capture and incident documentation produce the evidence auditors expect for monitoring, incident response, and access controls. Typical coverage includes secure event logging, retention of incident timelines, and traceable containment actions. To fully satisfy audits, organizations should pair XDR logging with policy documentation and governance practices.
How Does Continuous Monitoring and Streamlined Reporting Facilitate Compliance?
Continuous monitoring ensures relevant events are captured in real time and retained per retention policies, while streamlined reporting automates the creation of auditor-friendly summaries and detailed logs. A typical compliance checklist enabled by XDR includes incident history, response timelines, containment evidence, and access control logs. Automated reports reduce manual evidence collection and provide consistent artifacts for auditors, saving time during assessments. Recommended practices include defined log retention windows, role-based access to audit trails, and preserved triage notes for significant incidents.
By automating evidence collection and enforcing clear retention policies, XDR reduces audit prep overhead and helps demonstrate ongoing control effectiveness.
Why Choose ShieldWatch XDR as Your Advanced Cybersecurity Partner?
ShieldWatch positions XDR as an enterprise-grade solution built for mid-market and enterprise organizations, available directly and through MSP and channel partners. Our differentiators combine AI-driven automation, managed services, and operational integrations to shorten time-to-value. We emphasize fast deployment, broad visibility, and managed monitoring so teams translate platform capabilities into measurable security outcomes. These attributes help buyers evaluate how a commercial XDR offering maps to priorities like MTTR reduction and compliance readiness.
Below is a practical mapping of ShieldWatch features to business outcomes to help decision-makers compare benefits against objectives.
What Unique Features Does ShieldWatch XDR Offer, Including AI Agent Hyperautomation and Rapid Deployment?
ShieldWatch highlights several differentiated capabilities: AI Agent Hyperautomation for alert triage that learns from analyst outcomes; 150+ pre-built SOAR workflows to accelerate orchestration; retroactive 90-day historical log analysis for hunting and remediation; and rapid deployment to operational status in minutes. Each capability maps to clear business value: agentic AI reduces analyst time per alert, pre-built workflows cut playbook development overhead and speed containment, historical analysis uncovers dormant compromises, and fast deployment shortens time-to-value for security programs. Together these features help organizations reduce MTTR, increase detection confidence, and accelerate compliance readiness.
How Does ShieldWatch’s Managed 24/7 SOC Monitoring Enhance Security Operations?
ShieldWatch’s managed 24/7 SOC augments platform automation with human-led review to provide continuous protection and rapid verdicting, ensuring suspicious activity is validated and contained at any hour. The hybrid model runs clear automated actions through SOAR while routing equivocal cases to analysts for prompt investigation—maintaining both speed and accuracy. Continuous coverage prevents detection gaps during off-hours and reduces mean time to contain incidents. For teams wanting to augment internal capabilities, a managed SOC acts as an operational extension that enacts playbooks, handles escalations, and ensures incident continuity across shifts.
Engaging a managed SOC is a practical next step for organizations seeking immediate operational coverage paired with automation-led efficiency; procurement teams should request a demo or trial to validate fit and expected outcomes.
Frequently Asked Questions
What types of organizations can benefit from implementing XDR solutions?
XDR is especially valuable for mid-market and enterprise organizations facing complex, multi-vector threats. These teams benefit from unified telemetry and automated response to reduce alert fatigue and streamline incident handling. Regulated industries—finance, healthcare, and government—also gain from improved monitoring and richer audit evidence to protect sensitive data and meet compliance obligations.
How does XDR integrate with existing security tools and infrastructure?
XDR is built to complement, not replace, existing investments like EDR and SIEM. It ingests data from endpoints, networks, and cloud sources via APIs and connectors, enhancing visibility while preserving current tooling. That integration lets organizations keep their controls and workflows while gaining unified detection, correlation, and automated response.
What are the key performance indicators (KPIs) to measure the effectiveness of XDR?
Measure XDR effectiveness with KPIs such as mean time to detect (MTTD), mean time to respond (MTTR), false-positive rate, and incidents resolved per analyst. Track alert volume per analyst and time-to-triage to quantify reductions in alert fatigue and improvements in SOC productivity.
Can XDR solutions help with compliance and regulatory requirements?
Yes. XDR provides continuous monitoring, secure logging, and automated reporting that simplify audit preparation and produce evidence for frameworks like SOC 2, HIPAA, and ISO 27001. It can generate incident logs, triage notes, and containment records auditors expect—helping demonstrate effective monitoring and response practices.
What challenges might organizations face when implementing XDR?
Common challenges include integrating diverse telemetry sources and aligning XDR workflows with existing processes. Ensuring correct configuration and data flows can require engineering effort, and teams may need training to adopt new workflows. Overcoming these hurdles requires stakeholder alignment, clear communication of benefits, and focused onboarding and training.
How does XDR enhance threat hunting capabilities?
XDR strengthens threat hunting by centralizing normalized telemetry and enabling fast historical queries. Hunters can run hypothesis-driven searches across endpoints, cloud logs, and identity events to uncover patterns, surface dormant indicators, and harden controls. Findings then feed back into detection rules and playbooks for continuous improvement.
Conclusion
Extended Detection and Response (XDR) strengthens threat detection and speeds incident response by unifying telemetry, applying AI-driven analytics, and linking detection to automated and human-led response. The result is less alert noise, higher analyst productivity, and faster containment. ShieldWatch XDR combines platform capabilities with managed operations to help organizations reduce risk, meet compliance needs, and improve security outcomes. Explore ShieldWatch XDR to see how it can fit your security program and accelerate time-to-value.




Turn referrals into revenue—sign up for our affiliate program today!
Invite your network, boost your income—sign up for our affiliate program now!
Join our affiliate community and maximize your profits—sign up now!
Turn your network into income—apply to our affiliate program!
Do you have a spam problem on this website; I also am a blogger,
and I was curious about your situation; many of us have created some nice procedures
and we are looking to swap techniques with other folks, please shoot me an email
if interested.
Hi there! This is my first visit to your blog! We are a collection of volunteers and starting a new project in a community in the same niche.
Your blog provided us beneficial information to
work on. You have done a marvellous job!
Hey there, I think your site might be having browser compatibility issues.
When I look at your website in Firefox, it looks fine but when opening in Internet
Explorer, it has some overlapping. I just wanted to give you a quick heads up!
Other then that, wonderful blog!
Howdy very nice site!! Man .. Beautiful .. Amazing ..
I will bookmark your web site and take the
feeds also? I’m satisfied to seek out numerous helpful info right here within the publish, we need work out extra techniques on this regard,
thank you for sharing. . . . . .