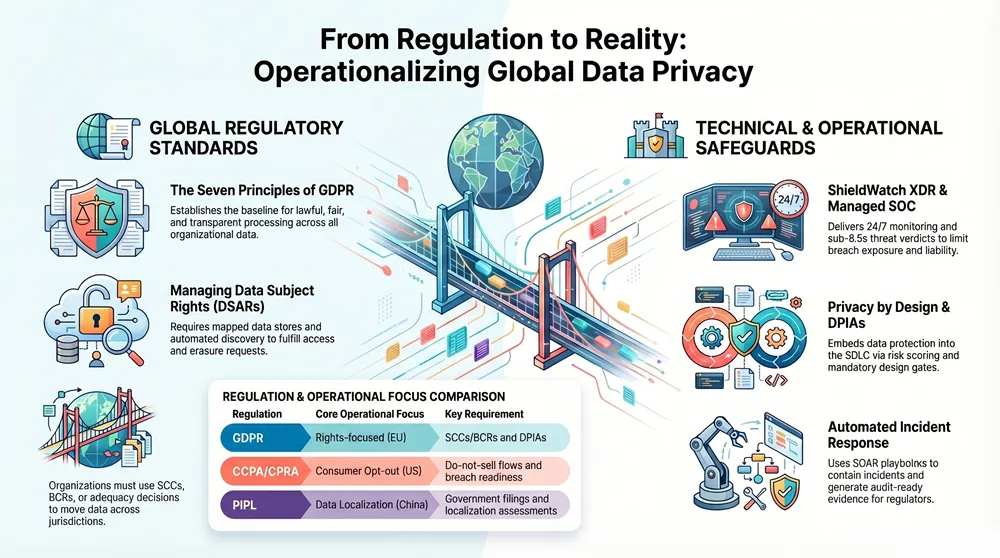
Organizations that handle personal data face a fast-growing and fragmented regulatory landscape — from the EU’s GDPR to California’s CCPA/CPRA and a wave of national privacy laws worldwide. This guide breaks down the legal principles, operational duties, and practical controls security and privacy teams need to meet data subject rights, breach-notification windows, and cross-border transfer rules without disrupting business operations. You’ll get a clear summary of the seven core GDPR principles, a focused CCPA/CPRA checklist, a concise comparison of GDPR/CCPA/LGPD/PIPL for cross-border activity, and actionable best practices for privacy-by-design, DPIAs, vendor risk and staff training.
Where it matters, we tie technical controls to compliance obligations and show how enterprise XDR and a managed SOC can limit breach impact and produce evidence for regulators. The guide ends with concrete detection, automation, and reporting steps CISOs and privacy leaders can use to strengthen their data protection posture.
What Are the Core Principles and Requirements of GDPR Compliance?
GDPR compliance means adopting lawful processing, clear accountability, and appropriate technical and organizational measures that protect data subjects and show demonstrable compliance. At its heart, the regulation sets principles that dictate how personal data must be treated, the lawful bases for processing, and obligations such as maintaining processing records, performing DPIAs for high-risk activities, and applying secure processing under Article 32. Practically, meeting these obligations reduces breach risk, speeds DSAR handling, and creates clearer audit trails for supervisory authorities.
The section below restates the seven principles in operational terms that governance and engineering teams can act on.
What Are the Seven Fundamental GDPR Data Protection Principles?
The seven GDPR principles set the baseline for lawful processing and privacy governance and map directly to tasks for security and data teams. Processing must be lawful, fair and transparent — which means clear privacy notices and logged legal bases or consent records. Purpose limitation and data minimization mean scoped collection, strict retention rules and automated deletion where appropriate. Accuracy, storage limitation, and integrity/confidentiality require validation checks, retention enforcement and strong encryption or access controls. Accountability requires documented processing records, DPIAs where needed and demonstrable technical and organizational measures (TOMs) like monitoring and incident logs that auditors can review.
How each principle translates into operational controls:
- Lawfulness, fairness, transparency: Publish clear purposes, record legal bases and log consent or contractual grounds.
- Purpose limitation: Tag data by purpose and block secondary uses without a new lawful basis.
- Data minimization: Limit fields collected and enforce automated retention rules.
- Accuracy: Provide correction workflows and run regular data quality checks.
- Storage limitation: Apply retention schedules and automated erasure where required.
- Integrity and confidentiality: Use encryption, strict access controls and active monitoring.
- Accountability: Keep processing records, conduct DPIAs and maintain audit trails.
Linking these principles to concrete engineering and governance tasks, and pairing them with monitoring, speeds verification during audits and improves DSAR response times.
How Do Data Subject Rights Under GDPR Impact Organizations?
GDPR’s data subject rights demand timely, verifiable responses that span privacy and security workflows. Rights like access, rectification, erasure, portability, restriction and objection create SLA-style obligations, usually measured in calendar days, and require coordinated processes across data owners, IT and security to locate, authenticate and action requests. Practically, that means mapping repositories, indexing subject identifiers across systems, and using role-based authentication to prevent fraudulent disclosures while preserving audit trails. Automating parts of DSAR handling — indexed searches, templated notices and redaction tools — reduces manual work, improves consistency and strengthens your regulatory position.
DSAR operational checklist for teams:
- Map data stores: Maintain an up-to-date inventory of repositories and data flows for rapid lookup.
- Authenticate requestors: Apply risk-based verification, including MFA where appropriate.
- Locate and export: Use automated search and export tools with redaction controls.
- Document actions: Keep tamper-evident audit logs to demonstrate compliance.
Following these steps helps ensure DSARs are handled within required timeframes while limiting exposure and operational friction.
CCPA and CPRA compliance starts with scoping: determine whether your processing meets applicability thresholds, then operationalize consumer rights and reasonable security measures under California law. Implement discovery and request workflows for rights to know, delete and opt out of sale or sharing, and incorporate CPRA’s additional protections for sensitive data and automated decision-making disclosures. Security obligations under CCPA center on “reasonable” safeguards and timely breach notifications — operational controls like logging, network segmentation and IR playbooks support those expectations. The checklist below highlights priority actions privacy and security teams should take to align operations with CCPA/CPRA.
CCPA/CPRA compliance checklist:
- Scope assessment: Confirm whether revenue, consumer volume or activity thresholds apply.
- Consumer rights workflow: Build verification, discovery and deletion pipelines.
- Opt-out mechanisms: Implement clear opt-out and do-not-sell/sharing controls.
- Security safeguards: Deploy least-privilege access, monitoring and encryption.
- Breach readiness: Maintain incident triage, notification and remediation timelines.
Applying this checklist reduces regulatory exposure and brings privacy and security processes into alignment.
What Consumer Rights Does CCPA and CPRA Grant?
CCPA and CPRA give consumers practical rights that require operational systems for discovery, verification and remediation. These include the right to know categories and specific pieces of personal data collected, the right to delete (with statutory exceptions), the right to opt out of sale or sharing, and protections against discrimination for exercising rights. CPRA expands protections for sensitive personal information and adds obligations around risk assessments for certain automated decision-making, so teams need updated data maps and record-keeping to demonstrate compliance. Operationalizing these rights means building authentication workflows, cross-system discovery tools, standardized deletion procedures and monitoring to ensure nondiscriminatory outcomes.
Operational steps to handle requests:
- Verify identity: Use risk-based verification methods appropriate to the request.
- Perform discovery: Use indexed searches and tagged categories to gather responsive records.
- Execute actions: Apply deletion or opt-out controls with rollback safeguards and thorough documentation.
These measures help deliver consistent consumer responses while preserving security and auditability.
What Are the Key Data Security and Incident Response Requirements Under CCPA?
CCPA frames data security around a “reasonable security” standard and sets breach notification expectations that require prompt investigation, containment and notification where applicable. Reasonable safeguards commonly include encryption in transit and at rest, strong access controls, segmentation, centralized logging and vulnerability management — all of which reduce unauthorized access and bolster forensic capability. Incident response must cover detection, containment, root-cause analysis, remediation and timely notifications; documenting every step is crucial for regulators and for mitigating liability. Detection and containment tools that shorten time-to-discovery directly cut breach impact and are central to meeting CCPA expectations.
Key technical controls for CCPA readiness:
- Encryption and key management: Protect data in transit and at rest with robust key controls.
- Access governance: Enforce least privilege and run continuous entitlement reviews.
- Monitoring and detection: Centralize logs and correlate events for faster detection.
- IR playbooks: Keep documented procedures for containment, forensics and notification.
These controls shrink breach scope and support a defensible posture when incidents occur.
How Do Global Data Privacy Laws Compare and Affect Cross-Border Compliance?
Global privacy regimes share the goal of protecting personal data and granting individual rights, but they differ on scope, legal bases, enforcement and cross-border transfer rules — creating operational complexity for multinational controllers and processors. GDPR focuses on lawful bases and strict transfer mechanisms like adequacy decisions and Standard Contractual Clauses (SCCs). CCPA/CPRA centers on consumer rights and opt-outs with territorial triggers. Other regimes such as Brazil’s LGPD and China’s PIPL bring region-specific transfer and localization requirements. Operationally, organizations should map transfers, apply technical controls (encryption, access restrictions) and maintain legal instruments (SCCs, BCRs) or rely on adequacy where available to move data lawfully across borders.
The table below summarizes practical operational implications for common global regulations.
This comparison shows that transfer rules and local obligations must be embedded into vendor contracts, technical controls and incident workflows to avoid regulatory friction and preserve lawful processing.
What Are the Differences and Similarities Between GDPR, CCPA, LGPD, and PIPL?
GDPR centers on lawful bases and strong individual rights with explicit cross-border safeguards. CCPA/CPRA emphasizes consumer choice and opt-out rights. LGPD and PIPL mix those approaches with local nuances that affect transfers and enforcement. Common ground includes transparency, data minimization and breach response; divergences appear around consent models, territorial scope and penalties. From an operational view, these regimes converge on practical controls — data mapping, DPIAs, logging, encryption and incident response — that can be implemented as baseline TOMs across jurisdictions to cut duplication and increase efficiency. Harmonizing legal differences into a common control set lets security teams build unified monitoring and reporting pipelines.
Operational takeaways:
- Align baseline TOMs: Use encryption, logging and IR playbooks as common controls.
- Document variations: Maintain a legal matrix that captures jurisdictional exceptions.
- Centralize transfer governance: Standardize contract templates and combine legal and technical controls for portability.
These steps create a scalable compliance program that respects regional differences while minimizing operational fragmentation.
How Do Cross-Border Data Transfer Regulations Influence Global Compliance?
Cross-border transfer rules force organizations to pair legal instruments with technical and contractual safeguards when moving personal data and to keep evidence of those safeguards for oversight or incident response. Mechanisms like adequacy decisions, SCCs and Binding Corporate Rules provide legal grounds for transfer; technical measures — encryption, pseudonymization and strict access controls — and contractual SLAs reduce residual risk. Operational transfer governance requires mapping flows, tracking the legal basis for each transfer and maintaining documentation aligned with DPIAs and vendor assessments to show regulators that transfers were risk-assessed. Continuous monitoring of transfer activity and automated alerts for anomalous large transfers help teams detect potential noncompliant movement quickly.
Combining legal and technical controls properly reduces transfer risk and gives regulators demonstrable evidence of deliberate governance.
How Does ShieldWatch XDR Support Data Privacy Compliance and Breach Prevention?
ShieldWatch XDR delivers unified visibility, continuous monitoring and automated response capabilities that directly support compliance needs: breach detection, containment, audit trails and evidence collection for regulatory reporting. The platform consolidates telemetry across endpoints, cloud and identity so teams can quickly scope incidents and produce the logs needed for DSARs and breach notices. With AI-driven hyperautomation and pre-built SOAR workflows, ShieldWatch accelerates containment and shortens mean time to verdict and response, which reduces data exposure and helps meet GDPR and CCPA notification expectations.
ShieldWatch capabilities that matter for compliance:
- Unified visibility: Consolidates telemetry across endpoints, cloud and identity for faster impact assessment.
- AI-driven detection: Delivers rapid threat verdicts to shorten detection windows and limit exposure.
- Automated incident response: Executes SOAR playbooks to contain incidents and preserve evidence.
- 24/7 SOC monitoring: Provides continuous oversight to detect anomalous activity outside business hours.
Those capabilities turn security events into structured evidence and actions privacy teams can use to fulfill notification and reporting obligations.
The table below maps ShieldWatch XDR features to operational compliance outcomes, showing alignment with GDPR and CCPA obligations.
This mapping illustrates how technical capabilities translate into demonstrable TOMs and operational outcomes regulators expect to see during incident reviews.
In What Ways Does ShieldWatch XDR Enable GDPR and CCPA Compliance?
ShieldWatch XDR helps meet GDPR and CCPA obligations by supplying consolidated logs, automated workflows and continuous monitoring that cut detection time and produce auditable evidence for regulatory filings and consumer notices. Unified visibility across endpoints, cloud workloads and identity simplifies discovery in DSARs and breach investigations, making it easier to identify affected datasets and timelines. Automated playbooks and hyperautomation speed containment and remediation, shortening the exposure window and supporting timely notifications under GDPR Articles 33/34 and CCPA expectations. ShieldWatch’s compliance-ready posture for frameworks like SOC 2 and ISO 27001 also aligns telemetry and reporting with common audit requirements.
Practical benefits for compliance teams:
- Faster forensic timelines: Consolidated telemetry accelerates root-cause analysis.
- Automated playbooks: Consistent containment reduces human error and improves documentation.
- Audit-ready logs: Structured evidence that supports regulatory reporting and DSAR responses.
These capabilities reduce operational friction between security operations and privacy teams during high-pressure events.
How Does AI-Driven Threat Detection and Automated Incident Response Enhance Data Protection?
AI-driven detection and automated incident response shorten mean time to detect and contain incidents, reduce manual triage and produce structured action logs that are essential for regulatory compliance and post-incident review. Agentic AI and hyperautomation correlate signals across telemetry sources and execute pre-approved SOAR workflows to limit blast radius and preserve chain-of-custody for evidence. Governance and auditability are maintained through human-AI collaboration models that log decisions, allow analyst overrides and retain playbook execution records for auditors. These automated controls not only strengthen defenses but also provide privacy teams with the timelines and evidence needed for breach notifications and regulatory inquiries.
These automated mechanisms measurably reduce incident impact and create defensible records for compliance processes.
What Are Best Practices for Building a Robust Data Privacy Framework?
A strong privacy program layers privacy by design, DPIAs, continuous monitoring, vendor risk management and workforce training into an integrated framework that aligns legal, engineering and security controls. Privacy by design embeds minimization, purpose constraints and retention controls into the SDLC; DPIAs identify and mitigate high-risk processing before launch. Vendor risk management enforces contractual SLAs and continuous monitoring for third-party processors, while regular training and tabletop exercises ensure people and processes support technical controls. The checklist below prioritizes steps to operationalize a practical, auditable privacy program.
Best-practice implementation checklist:
- Privacy by design in SDLC: Require data protection reviews at design gates.
- Conduct DPIAs: Assess risks and record mitigations for high-risk flows.
- Vendor due diligence: Run assessments, include SLAs and enable continuous monitoring.
- Continuous monitoring and IR testing: Maintain alerts, drills and post-incident reviews.
- Employee training: Deliver regular awareness, phishing simulations and role-specific guidance.
These layered controls build preventive and detective capabilities regulators expect from mature programs.
The table below maps common privacy controls to implementation steps, accountable roles and where managed XDR/SOC capabilities contribute operationally.
This mapping clarifies responsibilities and shows how managed monitoring and automated response fit into a defensible privacy program.
How to Implement Privacy by Design and Conduct Data Protection Impact Assessments?
Start privacy by design and DPIAs by placing privacy gates into the SDLC: require data flow diagrams, risk scoring and documented mitigation plans before deployment. A DPIA should cover scoping, data flow mapping, likelihood and impact assessment, selection of technical and organizational measures, and thorough documentation of decisions for auditors and supervisory authorities. Engineering teams must convert DPIA mitigations into concrete TOMs — pseudonymization, encryption, access controls and monitoring — and validate these controls post-deployment. Regular reviews keep DPIAs current with evolving processing activities and threat landscapes, creating an auditable lifecycle that aligns privacy governance with security operations.
DPIA checklist:
- Scope processing and data flows: Identify categories, purposes and touchpoints.
- Assess likelihood and severity: Score risk and prioritize mitigations.
- Select TOMs: Choose encryption, access controls, monitoring and retention changes.
- Document outcomes: Maintain records to demonstrate supervisory due diligence.
Embedding these steps into development workflows protects data subjects and provides regulators with evidence of proactive risk management.
What Role Do Vendor Risk Management and Employee Training Play in Data Privacy?
Vendor risk management and employee training are essential non-technical pillars of any privacy program: third-party processors and human error are common breach sources. Vendor assessments should confirm contractual obligations, security practices and monitoring capabilities; SLAs should include breach reporting and audit support. Employee programs should combine role-specific training, phishing simulations and tabletop exercises that rehearse incident roles and communications, using SOC findings to close the loop. Integrating managed SOC capabilities into vendor oversight and feeding incident learnings into training turns incidents into organizational improvement.
Vendor and training action items:
- Onboard vendors with security checklists and contracts: Include audit and breach-reporting clauses.
- Monitor vendor activity continuously: Use telemetry to detect anomalies.
- Train employees regularly: Deliver role-based modules, simulations and tabletop exercises.
- Integrate SOC findings into training: Use real incident data to sharpen awareness and response.
These practical measures reduce supplier-related risk and strengthen the human elements of your privacy program.
Frequently Asked Questions
What are the consequences of non-compliance with data privacy regulations?
Non-compliance with laws like GDPR and CCPA can lead to significant penalties, legal action and reputational harm. Under GDPR, fines can reach up to 4% of global annual turnover or €20 million, whichever is higher. Beyond fines, affected individuals may bring claims and customers can lose trust, which harms long-term business viability. Maintaining compliance is therefore both a legal necessity and a business imperative.
How can organizations ensure ongoing compliance with evolving data privacy laws?
Ongoing compliance requires a proactive program: regular audits, continuous training and timely updates to privacy policies. A dedicated compliance function should monitor legal changes and assess operational impact. Strong data governance — including regular DPIAs and risk assessments — helps identify gaps. Technology that automates compliance tracking and reporting can simplify upkeep and ensure timely action as laws evolve.
What role does employee training play in data privacy compliance?
Employee training is critical because human error is a frequent cause of breaches. Regular, role-specific training should cover data protection principles, employee responsibilities and the consequences of non-compliance. Phishing simulations and tabletop exercises prepare staff for real incidents and reinforce good practices. Well-trained teams reduce risk and improve incident response.
How can organizations effectively manage vendor risk in relation to data privacy?
Manage vendor risk by performing thorough due diligence before onboarding, embedding clear contractual obligations and requiring evidence of security controls. Assess vendors’ compliance history and operational maturity, and set SLAs that include breach notification and audit rights. Continuous monitoring of vendor activity via telemetry helps detect anomalies and enforces accountability.
What are the best practices for conducting Data Protection Impact Assessments (DPIAs)?
Good DPIA practice starts with a clear scope of processing and a mapped data flow. Assess the likelihood and severity of risks, choose proportionate TOMs, and document decisions and residual risk. Review DPIAs whenever processing changes or new threats emerge. Detailed documentation demonstrates due diligence to auditors and supervisory authorities.
How does technology support data privacy compliance efforts?
Technology is a force-multiplier for privacy: data discovery tools identify and classify personal data, automated workflows speed DSARs and breach notices, and advanced monitoring provides real-time alerts for suspicious activity. Combined with playbooks and centralized logging, these tools reduce manual effort, accelerate response and create the audit trails regulators expect.
Conclusion
Complying with data privacy rules like GDPR and CCPA protects people and preserves trust. By embedding privacy-by-design principles, running DPIAs, enforcing vendor controls, training staff and using technology like unified XDR and managed SOCs, organizations can streamline compliance and reduce breach risk. Taking these practical steps now strengthens your operational resilience and regulatory readiness. Explore our resources to sharpen your privacy program and stay aligned as rules evolve.




https://shorturl.fm/hDVUd
https://shorturl.fm/GIZ0S