ISO 27001 defines how to build and run an Information Security Management System (ISMS) that’s auditable, repeatable, and focused on reducing cyber risk. This guide walks through what ISO 27001 certification requires, the ISMS lifecycle, the controls and documents auditors expect, and the practical steps teams use to achieve audit readiness. You’ll find a clear overview of the standard, a mapped set of Annex A controls with evidence examples, a six-stage certification pathway, and recommendations for how continuous monitoring platforms and managed services can ease implementation. We also show where ShieldWatch XDR and a Managed SOC can cut operational effort by aligning product features to control objectives and executive metrics to support vendor selection and ROI decisions.
What is ISO 27001 and Why is it Essential for Information Security?
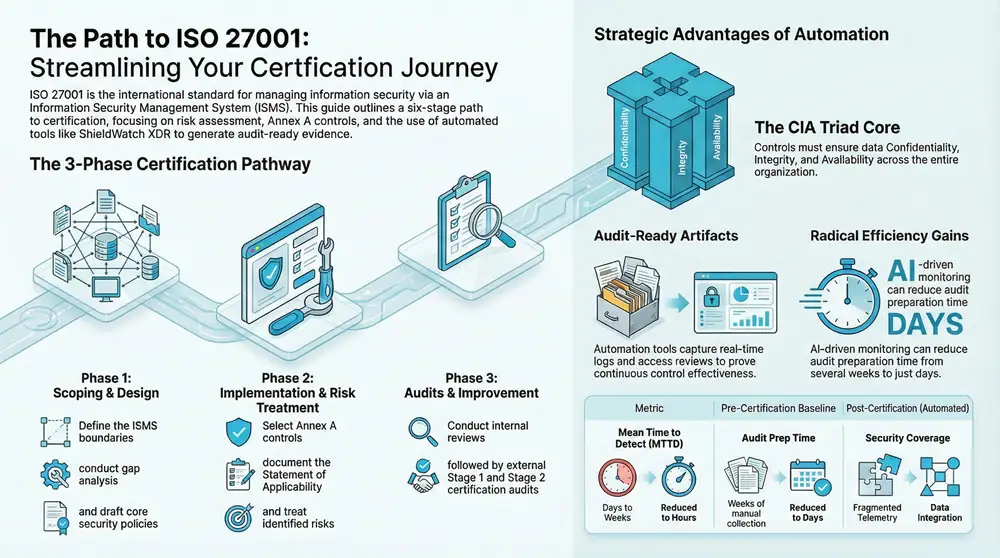
ISO 27001 is the international specification for an ISMS that brings people, processes, and technology together to manage information risk in a structured, auditable way. The standard requires organizations to run risk assessments, justify chosen controls from Annex A, and keep a Statement of Applicability and a risk treatment plan to explain those choices. The main advantage is independent, auditable assurance that security is being managed consistently—lowering residual risk and helping meet regulatory or contractual requirements. In practice, adopting ISO 27001 improves incident response readiness and creates repeatable evidence streams for audits. Grasping these basics prepares teams to define ISMS principles and the business outcomes that drive certification.
What are the core principles of ISO 27001’s Information Security Management System?
At its center, an ISMS implements the CIA triad—confidentiality, integrity, and availability—which are the control objectives Annex A helps organizations address. Confidentiality protects data from unauthorized access; integrity preserves accuracy and trustworthiness; availability ensures authorized users can access resources when needed. Governance and continual improvement are equally important: risk assessments reveal threats and weaknesses, leadership provides policy and resources, and the Plan-Do-Check-Act cycle drives regular improvement. Together these elements clarify roles, define monitoring and reporting, and establish how incidents are handled and remediated.
What business benefits does ISO 27001 certification provide to organizations?
ISO 27001 certification delivers measurable business value by lowering the likelihood and impact of security incidents through documented controls and auditable evidence. Certification signals credibility to customers and partners because it’s a third-party validation of repeatable security management. Internally, an ISMS brings operational discipline—clear procedures, defined responsibilities, and scheduled management reviews—which speeds response and sharpens accountability during incidents. Over time, certification can become a procurement differentiator where information security is a contract requirement.
What are the Key ISO 27001 Requirements and Controls?
ISO 27001 separates requirements into normative clauses and Annex A control objectives. The clauses set out what an ISMS must achieve; Annex A offers control categories to meet those aims. Required artifacts include a defined scope, an information security policy, a risk assessment and treatment methodology, a Statement of Applicability (SoA), documented procedures, internal audit records, and management review outputs. Annex A groups controls into families—access control, cryptography, operations security, communications security, supplier relationships—and each family maps to evidence types auditors expect. Knowing clause intent and Annex A categories helps teams design auditable controls and select monitoring tools that produce the required evidence.
Key translations from the standard to operational controls include:
- Normative clauses mandate governance, planning, resource support, performance evaluation, and continual improvement.
- Annex A lists practical controls grouped by objective; organizations select and justify applicable controls in the SoA.
- Common evidence sources are logs, configuration baselines, access review records, training records, and risk treatment documentation.
The table below maps representative Annex A control families to their intent and example evidence or monitoring capabilities that help demonstrate compliance.
This mapping shows how Annex A translates into concrete artifacts and monitoring outputs, helping teams prioritize the tools and processes that produce the audit evidence assessors expect.
What are the main clauses and Annex A controls of ISO 27001?
The main clauses—context, leadership, planning, support, operation, performance evaluation, and improvement—require organizations to set scope, assign leadership responsibility, plan by risk, allocate resources, operate controls, and evaluate effectiveness via monitoring and audits. Annex A complements these clauses with control objectives grouped into families such as asset management, physical security, human resources security, access control, cryptography, operations security, communications security, system acquisition, and supplier relationships. Each Annex A control family contains measures that must be chosen or justified in the SoA. Mapping clauses to Annex A turns governance requirements into technical and procedural controls that create demonstrable security posture.
What documentation and policies are required for ISO 27001 compliance?
Required and recommended documentation typically includes an ISMS scope statement, the information security policy, a current Statement of Applicability (SoA), a documented risk assessment and risk treatment plan, procedures for key processes, internal audit reports, and management review minutes. Auditors accept evidence such as system logs, access review reports, training attendance records, incident reports, and configuration-management records that link back to controls in the SoA. A clear document-control system with versioning and approval metadata is essential to show governance and traceability. Consistent documentation proves controls are not only implemented but are repeatable, auditable, and improving over time.
How Does the ISO 27001 Certification Process Work?
The certification journey follows a structured six-stage path from initial assessment to ongoing surveillance, verifying that an ISMS meets the standard and operates effectively. Each stage builds evidence and operational maturity: scoping and gap analysis define what needs attention; ISMS design and control implementation deliver policies and technical controls; internal audits and management review confirm readiness; Stage 1 and Stage 2 external audits validate conformity and effectiveness; and surveillance audits plus continual improvement preserve certification. Tying risk assessments, control implementation, and documented evidence into an auditable chain makes audits smoother and shortens time to certification.
What are the six stages of the ISO 27001 certification process?
The certification pathway typically follows six stages with specific deliverables and timelines.
- Gap analysis and scoping: Assess current state vs. ISO 27001, define ISMS scope, boundaries, and stakeholders.
- ISMS design and control implementation: Draft policies, select Annex A controls, produce the SoA, and deploy technical and procedural controls.
- Risk assessment and treatment: Identify and evaluate risks, then document the risk treatment plan linking controls to prioritized risks.
- Internal audits and management review: Run internal audits, address nonconformities, and hold management reviews to prove governance.
- Stage 1 and Stage 2 external audits: Complete a Stage 1 readiness check followed by a Stage 2 certification audit that examines implementation and effectiveness.
- Surveillance and continual improvement: Sustain the ISMS through surveillance audits, monitoring, and corrective actions to keep certification valid.
Each stage creates documentation and evidence auditors will review. Timelines vary by organization size and maturity; many teams plan several months to a year depending on initial gaps.
How are risk assessments and internal audits conducted during certification?
Risk assessments identify assets, threats, and vulnerabilities, assess impact and likelihood, and prioritize risks for treatment. Teams use qualitative matrices or quantitative scoring tied to business impact, then select controls proportional to residual risk. Internal audits sample processes and evidence to verify controls are operating as intended; auditors typically expect logs, access reviews, change records, and corrective-action histories. Continuous monitoring tools that provide time-stamped logs and trend reports simplify evidence collection and make it easier for auditors to validate ongoing control effectiveness.
Many organizations use continuous monitoring platforms and managed SOC services to automate evidence capture and reduce manual audit prep—streamlining the path to certification while keeping controls operational.
For teams that want to lower the operational load of monitoring and evidence collection, ShieldWatch XDR is an example of an autonomous detection and response platform that combines AI with a 24/7 Managed SOC. ShieldWatch XDR protects endpoints, network, cloud, and identity and includes compliance-ready features that generate logs and retrospective analyses useful for ISO 27001 evidence. Using such tooling alongside documented processes reduces mean time to detect and helps preserve consistent audit artifacts, letting internal teams focus on risk treatment and governance.
How Can ShieldWatch XDR Support ISO 27001 Implementation and Compliance?
ShieldWatch XDR aligns with ISO 27001 operational needs by automating monitoring, correlating events across domains, and producing audit-ready evidence that connects detections to control objectives. Its AI-driven detection correlates endpoint, network, cloud, and identity signals to cut noise and surface validated incidents that map to Annex A intents like access control, operations security, and incident management. The Managed SOC adds expert validation and 24/7 coverage, helping teams respond quickly and retain continuous evidence trails. Deployed properly, ShieldWatch XDR can shorten time-to-evidence for internal audits and keep surveillance readiness—by preserving logs, alerts, and incident timelines auditors expect to review.
Below is a concise feature-to-control mapping that shows how ShieldWatch capabilities align with ISO 27001 control families and the operational benefits they deliver.
This mapping illustrates how platform features fit into an ISMS, creating evidence and operational improvements auditors can trace back to control objectives.
How does ShieldWatch XDR automate monitoring of ISO 27001 Annex A controls?
ShieldWatch XDR ingests telemetry from endpoints, networks, cloud services, and identity systems, then applies correlation and AI rules to detect control-relevant events and anomalies. For access control (A.9), it captures authentication anomalies and privilege escalations; for operations security (A.12), it records suspicious processes, lateral movement indicators, and configuration drift. Automated reporting bundles these events into time-stamped evidence packages that link to the SoA and risk-treatment outcomes. Continuous evidence collection reduces manual log pulls and speeds internal audit sampling, while retrospective analysis lets teams rebuild timelines—typically covering the prior 90 days—when auditors ask for historical context.
What are the benefits of integrating ShieldWatch’s Managed SOC with ISO 27001 compliance?
Pairing technology with a Managed SOC brings expertise and continuous validation that improve audit readiness and reduce residual risk. Managed analysts review and contextualize detections, run root-cause analysis, and coordinate response activities—shortening mean time to detect and respond and producing documented incident-handling records required for A.16. Outsourcing 24/7 monitoring eases staffing burdens, ensures off-hours coverage, and centralizes evidence collection for audits. The Managed SOC also delivers consistent reporting templates and trend analyses that feed management reviews and support the ISMS continual-improvement cycle.
What Strategic Value Does ISO 27001 Certification Offer to Executives?
ISO 27001 gives executives a governance framework that reduces cyber risk while aligning security investments to business continuity and risk objectives. An ISMS translates technical controls into measurable outcomes—lower breach likelihood, faster recovery, and stronger supplier confidence—that leadership can quantify. Executives should monitor a concise set of metrics such as mean time to detect (MTTD), mean time to respond (MTTR), percentage of controls with automated evidence, and audit-prep time to assess program maturity. These metrics guide procurement and vendor decisions, helping leaders choose solutions that lower operational cost and accelerate certification.
When evaluating cybersecurity vendors for ISO 27001, prioritize providers that demonstrate evidence generation, integrate with existing workflows, and offer an operational model that matches organizational capacity. ShieldWatch positions its XDR and Managed SOC to provide continuous monitoring, AI-driven detection, and built-in compliance reporting to reduce audit prep overhead. Use a procurement framework that weighs risk reduction, evidence automation, SLA commitments, and total cost of ownership to align vendor capabilities with strategic goals and timelines.
How does ISO 27001 certification mitigate cyber risk and enhance business continuity?
An ISMS formalizes how risks are identified, treated, and monitored, reducing the chance and impact of incidents by ensuring controls match business risk. Certification requires documented business continuity and incident-management procedures that improve recovery capabilities and service availability. Better detection and response mean quicker containment, fewer disruptions, and clearer communications during incidents—outcomes that increase customer and partner trust. Those benefits translate into lower financial and reputational exposure and stronger operational resilience.
What factors should CIOs and CISOs consider when selecting cybersecurity solutions for ISO 27001?
Executives should evaluate a vendor’s ability to map features to Annex A controls, the degree of evidence automation, scalability across environments, integration with SIEM and ITSM systems, and the delivery model (self-managed versus managed SOC). Review SLAs for detection coverage and response times and the availability of audit-aligned reporting templates. If you work through MSPs, assess channel and partner support. A weighted decision checklist that prioritizes evidence automation and operational fit helps ensure selected tools speed certification rather than add complexity.
Vendor Selection Checklist:
- Control Mapping: Vendor provides clear feature-to-Annex A mappings and example evidence.
- Evidence Automation: Platform automates log collection, correlation, and audit reporting.
- Operational Model: Managed SOC options and SLAs align with business needs.
Applying these criteria reduces procurement ambiguity and helps pick solutions that support ISO 27001 objectives and executive risk tolerance.
What Are Common Questions About ISO 27001 Certification?
Below are concise answers to frequent, practical questions about required artifacts, audit evidence, and how automation fits into compliance. Use these as quick references during readiness assessments and procurement discussions—each item highlights how automation and Managed SOCs can help collect and maintain audit-focused evidence.
What documents are required for ISO 27001 certification?
Core documentation includes the information security policy, the Statement of Applicability (SoA), a documented risk assessment and risk treatment plan, the ISMS scope statement, internal audit reports, corrective-action records, and management review minutes. Additional evidence often includes procedures for access control, incident management, change management, training records, and system logs that demonstrate control operation. Auditors expect technical artifacts like logs and access-review reports to be traceable back to controls listed in the SoA. Keeping these documents under version control with approvals shows governance and smooths the audit process.
The essential documents auditors typically look for are:
- Information Security Policy: High-level direction and leadership commitment.
- Statement of Applicability (SoA): Inventory of controls with inclusion/exclusion justifications.
- Risk Assessment & Treatment Plan: Methodology, identified risks, and selected treatments.
These records form the backbone of audit evidence—keeping them current, approved, and linked to technical artifacts reduces audit friction and improves readiness.
How does AI and automation enhance ISO 27001 compliance efforts?
AI and automation accelerate detection, lower false positives, and generate structured evidence that maps directly to control objectives—cutting manual audit prep. Automated correlation links events across endpoints, cloud, and identity to build incident timelines and impact analyses, while reporting engines produce time-series evidence and control-specific summaries for auditors. Automation works best combined with human validation to ensure context and accuracy. Together, they reduce routine work, shorten MTTD and MTTR, and create repeatable evidence streams ready for surveillance audits.
Practical automation examples include scheduled log ingestion and correlation, anomaly detection for access violations, and automated evidence exports that feed management reviews and internal audit sampling. These capabilities turn raw telemetry into auditable artifacts and let security teams focus on remediation and control improvements instead of manual evidence assembly.
This guide closes with practical checklists and mappings teams can use to align ISMS artifacts, monitoring tools, and vendor capabilities to ISO 27001 requirements.
Approaching ISO 27001 as a governance framework supported by automated evidence collection and targeted managed services lets teams reach certification readiness while lowering operational overhead and strengthening security posture.
Frequently Asked Questions
What is the role of the Statement of Applicability (SoA) in ISO 27001?
The SoA is a central ISMS document that lists which Annex A controls apply to your organization and explains why each control is included or excluded. It links your risk assessment to the controls you implement and should be updated as risks and controls change. Treat the SoA as a living record that supports ongoing compliance and audit readiness.
How often should organizations conduct internal audits for ISO 27001 compliance?
Internal audits should occur at least annually, but frequency should match the organization’s size, complexity, and risk profile. More frequent audits—especially after major process, technology, or personnel changes—help catch issues early and enable timely corrective action.
What are the key challenges organizations face when pursuing ISO 27001 certification?
Common challenges include allocating enough resources, interpreting the standard correctly, and keeping stakeholders engaged. Limited internal expertise can slow implementation, and aligning existing processes to ISO 27001 may require cultural and procedural change. Incomplete or poorly managed documentation is another frequent pitfall. Addressing these challenges requires leadership buy-in, clear planning, and a pragmatic approach to controls and evidence collection.
How can organizations ensure continuous improvement in their ISMS?
Continuous improvement relies on regular monitoring, evaluation, and updates driven by performance metrics and audit findings. Implement a Plan-Do-Check-Act (PDCA) cycle, invest in training and awareness, and use feedback channels to surface weaknesses. Real-time monitoring and automated reporting provide the insights needed to make proactive improvements to your security posture.
What is the significance of management reviews in the ISO 27001 process?
Management reviews let leadership assess ISMS effectiveness and alignment with business objectives. Reviews should examine audit results, risk assessments, corrective actions, and changes to internal or external contexts. Regular management reviews enable informed decisions on resource allocation, policy updates, and strategic direction that strengthen the ISMS.
How does ISO 27001 certification impact an organization's reputation?
ISO 27001 certification signals a proven commitment to information security and risk management. It reassures customers, partners, and regulators that your organization follows internationally recognized practices for protecting sensitive information. Certification can enhance trust, open procurement opportunities, and differentiate your organization in security-sensitive markets.
Conclusion
ISO 27001 certification gives organizations a practical framework for managing information risk, improving resilience, and building stakeholder trust. Implementing a structured ISMS demonstrates a commitment to protecting sensitive data while aligning security practices with industry standards. To start your certification journey, consider tools and services—like ShieldWatch XDR and a Managed SOC—that automate evidence collection and simplify ongoing monitoring. Explore our resources to plan a focused, audit-ready path to ISO 27001 certification.




Maximize your earnings with top-tier offers—apply now!
Join our affiliate family and watch your profits soar—sign up today!
Start earning every time someone clicks—join now!
Apply now and receive dedicated support for affiliates!
Unlock top-tier commissions—become our affiliate partner now!