Compliance audits are getting harder: telemetry volumes grow, regulator expectations tighten, and enterprises must both centralize controls and prove them quickly. This guide shows how extended detection and response (XDR) combined with a managed security operations center (SOC) eases audit friction by unifying telemetry, automating evidence collection, and keeping continuous control validation.
You’ll learn what auditors look for, how XDR shortens preparation with centralized correlation and automated reporting, why a 24/7 managed SOC matters for regulatory assurance, and how a modern XDR platform maps to SOC 2, HIPAA, CMMC 2.0, and ISO 27001. We also provide practical deployment steps, sample SOAR playbooks for evidence packaging, and checklists teams can use to accelerate audit timelines. Throughout, we highlight actionable practices—audit readiness, audit automation, and managed SOC for compliance—that reduce audit risk.
What Are Cybersecurity Compliance Audits and Their Key Frameworks?
A cybersecurity compliance audit is a formal review that confirms an organization’s controls, processes, and evidence meet a defined standard. Auditors assess control design, operational effectiveness, and artifacts like logs and incident reports. Audits provide independent assurance that controls work as intended, establish evidence trails, and surface gaps that need remediation. When tools live in silos—separate EDR, identity logs, and cloud telemetry—auditors often find incomplete timelines and breaks in chain-of-custody, which drives up time and cost. Knowing core frameworks and their evidence expectations helps security teams prioritize telemetry, retention, and reporting so audits run smoother and return fewer exceptions.
H3: What Is a Cybersecurity Compliance Audit?
A compliance audit checks controls against a specific framework by reviewing policies, configurations, monitoring outputs, and incident evidence to confirm compliance and operational effectiveness. Auditors typically sample control mappings, events, retention rules, and incident handling artifacts to form an opinion. Common deliverables include evidence bundles (logs, timelines), exception reports, and remediation plans. Failures usually trace back to missing logs, inadequate retention, or undocumented tuning. Consistent log capture, preserved metadata, and recorded playbook runs address the most common findings and speed the audit process.
H3: Which Compliance Frameworks Are Essential: SOC 2, HIPAA, CMMC 2.0, ISO 27001?
These frameworks have different scopes but share an evidence-first mindset: SOC 2 focuses on trust service criteria and operational controls; HIPAA enforces safeguards around protected health information; CMMC 2.0 defines maturity-based practices for DoD contractors; ISO 27001 centers on an ISMS and continual improvement. Each requires documented controls, demonstrable monitoring, and verifiable incident response procedures that auditors can sample. Mapping framework requirements to telemetry and retention policies reduces uncertainty during assessments and creates repeatable evidence-generation processes auditors can rely on.
Different frameworks map to common evidence types:
- SOC 2: operational monitoring logs, access control evidence, and change-management artifacts.
- HIPAA: PHI access logs, audit trails, and breach detection documentation.
- CMMC 2.0: practice-level artifacts demonstrating repeatable processes and maturity evidence.
- ISO 27001: ISMS documentation, risk assessments, and proof of continual monitoring.
This shared evidence model lets security teams prioritize telemetry sources that serve multiple frameworks and anticipate likely auditor questions.
How Does XDR Enhance Compliance Audit Readiness and Automation?
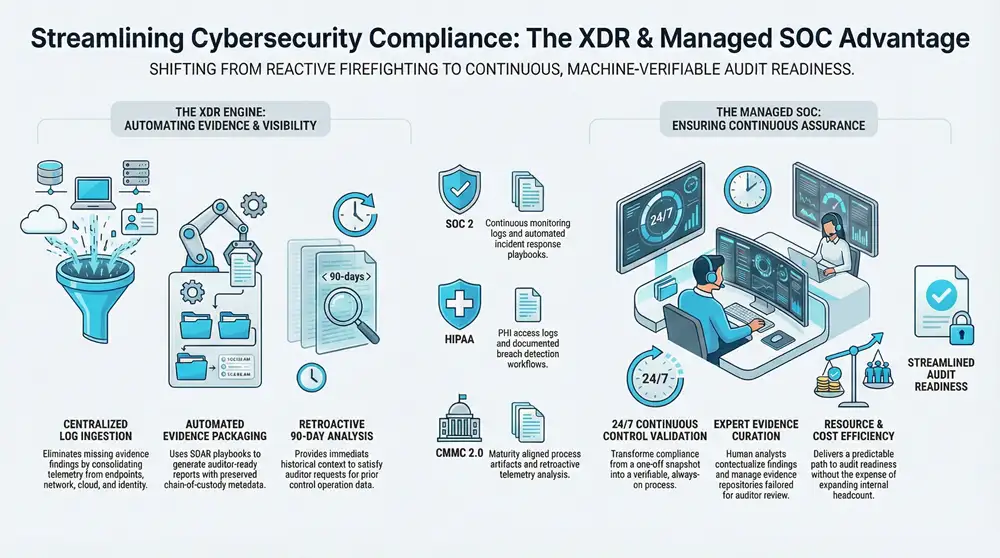
XDR improves audit readiness by centralizing telemetry from endpoints, network, cloud, and identity; correlating events into contextual timelines; and producing auditor-friendly artifacts automatically. Unified ingestion and correlation close evidence gaps, automated retention and tagging preserve chain-of-custody, and continuous monitoring gives auditors an always-on view. The result: shorter evidence-assembly times, fewer manual spreadsheets, and reproducible, machine-verifiable outputs that boost auditor confidence. The table below maps common XDR functions to the audit-ready outputs auditors expect.
- XDR centralizes telemetry to eliminate blind spots.
- XDR correlates disparate signals into auditor-ready timelines.
- XDR automates evidence packaging and retention policies.
Those capabilities shift teams from reactive collection to proactive evidence stewardship.
Next we show how unified platform capabilities translate into product features you can deploy to accelerate audit readiness.
ShieldWatch XDR is a practical example: the platform consolidates threat detection, response, and compliance monitoring across endpoints, networks, cloud, and identity while pairing autonomous AI with a human-led SOC. ShieldWatch’s agentic AI and hyper-automation reduce manual steps, and pre-built SOAR workflows simplify evidence collection and reporting—demonstrating how an XDR design pattern becomes operational audit automation.
H3: How Does XDR Improve Threat Detection and Data Visibility for Audits?
XDR enhances detection and audit visibility by linking endpoint, network, cloud, and identity telemetry into clear incident narratives auditors can trace. Correlation reduces false positives and surfaces the exact events and artifacts auditors request; retention and historical analysis enable retroactive investigation during pre-audit reviews. When disparate logs are united in a single timeline, auditors see cause, scope, and remediation without manual cross-referencing. Consolidated visibility addresses common audit pain points—missing context and fragmented evidence—by making control-relevant events discoverable and explainable.
H3: How Does XDR Automate Evidence Collection and Reporting?
XDR runs SOAR playbooks to export normalized logs, attach chain-of-custody metadata, and generate packaged reports aligned with auditor expectations. Automated tagging and retention policies ensure evidence meets timeframes, and playbook artifacts document who acted and when—information auditors use to validate operational effectiveness. A sample mini-playbook might trigger on an incident, gather endpoint memory and network flow logs, normalize fields, and produce a downloadable evidence bundle with a cover report. That automation removes manual work, cuts human error, and delivers reproducible artifacts auditors can sample easily.
What Are the Benefits of Managed SOC Services for Regulatory Compliance?
A managed SOC gives you continuous monitoring, expert triage, and audit support many internal teams can’t sustain 24/7. Analysts validate alerts, contextualize findings for compliance teams, and maintain evidence repositories and playbook runbooks auditors can review. For mid-market organizations without deep in-house SOC staffing, outsourcing routine monitoring is cost-effective and delivers a predictable path to audit readiness without expanding headcount. The core operational benefit is a reliable, auditable process that links detection to documented response and evidence retention.
Three high-level advantages of a managed SOC:
- Continuous control validation and monitoring that reduce drift and surprise findings.
- Expert evidence curation and incident summaries tailored for auditors.
- Resource and cost efficiency by extending SOC capabilities without expanding headcount.
Together, these benefits move audit readiness from ad-hoc firefighting to disciplined evidence stewardship and demonstrable control effectiveness.
Operational consistency in a managed SOC comes from routine runs and documented outputs auditors can sample during assessments.
H3: How Does a 24/7 Managed SOC Ensure Continuous Compliance?
A 24/7 managed SOC enforces continuous compliance through regular monitoring, scheduled control health checks, and evidence stewardship routines that validate control operation over time. Daily and weekly runbooks map monitoring tasks to control families, while dashboards show control health and exceptions auditors can query. Escalation paths preserve evidence integrity—every handoff is logged and summarized—so auditors receive consistent, timestamped narratives of incidents and remediation. This cadence turns controls from one-off snapshots into continuous, verifiable processes auditors trust.
H3: How Do AI and Automation in SOC Accelerate Audit Response?
AI and automation speed audit response by accelerating triage, synthesizing evidence, and producing auditor-ready documentation with less manual effort. Agentic AI filters noise to surface high-confidence incidents, while SOAR workflows execute evidence-collection steps and compile playbook logs that show chain-of-custody. These mechanisms shorten mean time to verdict and reduce time to produce audit artifacts; human analysts then verify and contextualize outputs so auditors can trust them. The outcome is faster, more accurate audit responses that combine machine efficiency with human oversight.
How Does ShieldWatch XDR Support Specific Compliance Frameworks?
ShieldWatch XDR ties platform capabilities to framework requirements by linking telemetry collection, automated reporting, and managed SOC outputs to the artifacts auditors expect. Continuous monitoring and auto-generated reports provide the retention and evidence summaries required by SOC 2 and ISO 27001; identity and activity monitoring plus breach detection playbooks help meet HIPAA safeguards. For DoD-focused organizations, ShieldWatch produces maturity-aligned artifacts and historical analyses that support CMMC 2.0 practices. The table below maps framework requirements to ShieldWatch capabilities to illustrate practical alignments for audit teams.
ShieldWatch’s product attributes—autonomous AI plus a human-led SOC, hyper-automation, 150+ pre-built SOAR workflows, sub-8.5-second average verdict time, rapid deployment with retroactive 90-day log analysis, and unified consolidation of SIEM, SOAR, and EDR—translate into tangible audit benefits. These capabilities shorten evidence-collection cycles, automate repetitive documentation, and provide the historical visibility auditors commonly request.
H3: How to Achieve SOC 2 Compliance with ShieldWatch XDR?
Reaching SOC 2 with ShieldWatch follows three practical phases: baseline scoping and control mapping, platform instrumentation and SOAR playbook deployment, and audit evidence packaging with continuous monitoring.
First, define scope and map trust services criteria to telemetry sources so controls are targeted correctly.
Next, instrument endpoints, cloud, identity, and network sources into ShieldWatch and deploy SOAR playbooks that automate evidence collection for each control.
Finally, generate auditor-facing evidence bundles and sustain continuous monitoring to demonstrate operational effectiveness across the audit period.
These steps convert control intent into machine-verifiable and human-reviewed artifacts auditors depend on.
H3: How ShieldWatch XDR Facilitates HIPAA, CMMC 2.0, and ISO 27001 Readiness?
ShieldWatch supports each standard with focused capabilities: for HIPAA, identity and access logging plus breach-detection workflows produce demonstrable PHI protection artifacts; for CMMC 2.0, maturity practices map to repeatable SOAR-driven processes and historical evidence; for ISO 27001, ISMS monitoring and incident documentation back continual improvement. A single practical feature—the retroactive 90-day analysis—gives auditors historical visibility into prior control operation. These aligned capabilities make it faster to assemble the specific artifacts auditors request across multiple frameworks.
What Are Best Practices for Implementing ShieldWatch XDR and Managed SOC?
Successful XDR and managed SOC implementations start with a focused pre-deployment assessment to identify scope, required telemetry, and control mappings, then proceed with prioritized integration and tuning to ensure auditor-relevant data flows are intact. Best practices: establish retention and tagging policies up front, deploy SOAR playbooks for evidence packaging, and validate evidence bundles against sample auditor queries. Integration typically sequences identity and endpoint telemetry first, then network and cloud feeds, and finally optional SIEM coexistence to limit disruption. These steps reduce friction and create a repeatable evidence lifecycle that accelerates audit timelines.
Below is a deployment checklist outlining integration points, prerequisites, and expected deliverables to guide teams through audit-readiness implementation.
This checklist clarifies responsibilities and produces tangible deliverables auditors can sample during assessments.
Operational guidance for deployment emphasizes rapid onboarding and retroactive analysis: initial telemetry ingestion and basic alerts can be stood up quickly, retroactive 90-day analysis provides immediate historical context, and ongoing tuning of rules and SOAR playbooks improves evidence quality. Plan a cadence of tuning cycles where playbooks are refined, retention is verified, and sample evidence bundles are validated against likely auditor questions.
H3: What Is the Deployment Timeline for ShieldWatch XDR Audit Readiness?
Deployment follows discovery, instrumentation, tuning, retroactive analysis, and audit-ready sign-off. Initial telemetry onboarding can be completed rapidly, but full tuning and evidence validation require iterative cycles. Discovery scopes controls and sources, instrumentation brings in logs and agents, tuning reduces false positives and aligns tagging, retroactive analysis provides historical context (90 days where available), and final sign-off confirms evidence bundles meet auditor expectations.
This phased approach balances speed with quality, letting teams show auditors consistent artifacts from the moment historical analysis is available through ongoing monitoring.
H3: How to Integrate ShieldWatch XDR into Existing Security Stacks?
Integration follows a priority pattern: connect identity providers and log sources first, deploy lightweight endpoint agents next, then ingest cloud and network telemetry, and finally integrate with existing SIEMs if you need to preserve historical workflows. Use API connectors and standardized log forwarding to minimize disruption, and validate each integration with sample auditor queries to confirm fields and timestamps are preserved. Coexistence options include dual-archiving and forwarding so existing tools retain visibility while ShieldWatch handles correlation and evidence packaging, enabling a gradual migration to a unified, audit-ready posture.
- Start with identity: Ensure access logs include user context before adding other sources.
- Add endpoints next: Deploy agents for process and file telemetry to capture forensic artifacts.
- Validate and tune: Run sample auditor queries to confirm evidence completeness.
These steps create repeatable integration patterns that reduce friction and produce auditor-ready outputs sooner.
ShieldWatch’s managed SOC and automation support these best practices with pre-built SOAR workflows, continuous monitoring, and historical analysis teams can leverage to meet auditors’ evidence requests more predictably and with less manual effort.
Frequently Asked Questions
What role does automation play in cybersecurity compliance audits?
Automation makes audits faster and more reliable. Automated evidence collection and reporting reduce manual work and human error, producing consistent, auditor-friendly documentation and ensuring required logs and artifacts are captured in real time. That streamlines the audit process and preserves a continuous compliance posture so teams can respond quickly to auditor requests.
How can organizations prepare for unexpected findings during an audit?
Run regular internal assessments and mock audits to spot gaps early. Maintain a clear incident response plan and comprehensive documentation of controls, processes, and evidence. Continuous monitoring and regular policy updates help you explain discrepancies and respond effectively when auditors surface unexpected findings.
What are the common challenges faced during cybersecurity compliance audits?
Common challenges include fragmented evidence, lack of centralized data, and incomplete control documentation. Siloed systems make it hard to present a cohesive compliance story. To address these issues, invest in integrated solutions like XDR that centralize telemetry and automate evidence collection to smooth the audit process.
How does ShieldWatch XDR differ from traditional security solutions?
ShieldWatch XDR is a unified platform that integrates threat detection, response, and compliance monitoring across endpoints, networks, and cloud. Unlike siloed tools, it centralizes telemetry and automates evidence collection to simplify generation of auditor-ready documentation. That holistic approach improves security posture and streamlines compliance workflows.
What best practices should organizations follow when implementing XDR solutions?
Start with a pre-deployment assessment to define scope and required telemetry. Set retention and tagging policies up front, deploy SOAR playbooks for automated evidence packaging, and prioritize identity and endpoint telemetry before adding network and cloud sources. Regular tuning cycles will ensure evidence quality and alignment with auditor expectations.
How can a managed SOC enhance an organization's compliance efforts?
A managed SOC brings continuous monitoring, expert triage, and audit support. Analysts contextualize findings, curate evidence, and keep detailed records auditors can review. Outsourcing these functions delivers cost efficiencies and helps organizations remain audit-ready without expanding internal teams.
What is the significance of continuous monitoring in compliance audits?
Continuous monitoring proves controls operate over time rather than at a single point. It helps detect and close gaps early, provides up-to-date evidence for auditors, and supports quicker incident response—demonstrating effective control operation throughout the audit period.
Conclusion
XDR plus a managed SOC makes compliance audits more predictable and less resource-intensive. By centralizing telemetry and automating evidence collection, organizations can meet regulatory requirements faster and with greater confidence. Beyond simplifying audits, these solutions strengthen overall security posture. Learn how ShieldWatch XDR can streamline your compliance program today.




Promote our products and earn real money—apply today!
Maximize your income with our high-converting offers—join as an affiliate!