XDR vs EDR: Key Differences and Practical Benefits for Modern Cybersecurity
If your organization is weighing XDR against EDR, you need clear definitions and decision criteria that connect security investments to real operational outcomes. This article defines Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR), contrasts their scope and capabilities, and explains when XDR is the right next step versus when strong EDR remains an essential control. You’ll see how multi‑domain telemetry, AI‑driven correlation, and automation improve detection fidelity and speed up response, plus a practical checklist for choosing between point tools, integrated XDR, and Managed XDR.
We also map a modern XDR deployment to enterprise needs using the ShieldWatch XDR Platform (Agentic AI + 24/7 SOC) as a concrete example. By the end, you’ll have a comparison table, feature‑to‑impact mappings, and a buyer checklist to support procurement and architecture conversations about endpoint detection, XDR, and managed security services.
What is Endpoint Detection and Response?
Endpoint Detection and Response (EDR) is a security capability centered on continuous, agent‑based monitoring of endpoints to detect, investigate, and remediate threats. EDR collects endpoint telemetry—process activity, file and registry changes, network connections—and applies signatures, heuristics, and behavioral analytics to surface suspicious activity. Its main value is deep endpoint visibility and forensic detail that enable rapid containment and cleanup of malware, credential theft, and lateral movement. Those strengths explain why EDR is a foundational control in most security stacks and why teams often ask whether EDR alone is enough in hybrid, cloud‑forward environments.
EDR delivers several core functions that support endpoint security posture and incident response:
- Continuous Telemetry Collection: Resident agents capture process, file, and network activity for forensic and historical analysis.
- Behavioral Detection: Analytics flag anomalous behaviors and patterns that indicate compromise.
- Response Actions: Automated or manual containment—process kill, host isolation, rollback—reduces immediate risk.
EDR supplies rich endpoint context that investigators rely on, but its endpoint‑centric focus creates blind spots that broader correlation and cross‑domain detection are designed to close. That leads into how EDR protects endpoints day to day.
How does EDR protect endpoints and detect threats?
EDR protects endpoints by installing lightweight agents that collect detailed telemetry—process trees, loaded modules, file hashes, and local registry changes—and forward that data to a central analysis engine. Agents apply local heuristics and behavioral rules to block or quarantine known malicious activity, while centralized analytics enable correlation and forensic reconstruction. Typical detection scenarios include spotting ransomware through anomalous file I/O, catching credential dumping by unusual access to system secrets, and detecting living‑off‑the‑land techniques via odd process parent/child relationships. The agent model excels at host‑level containment and provides the artifacts SOC analysts need to build incident timelines and find root causes.
That local focus works well for many endpoint‑contained incidents, but because EDR usually lacks native visibility into network flows, cloud telemetry, or identity events, some multi‑stage attack paths remain obscured. Extending detection beyond endpoints addresses those gaps — which is where XDR comes in.
What are the limitations of traditional EDR solutions?
Traditional EDR is limited by an endpoint‑only telemetry model that can miss multi‑stage attacks spanning cloud services, identity systems, and network segments. High alert volumes and weak cross‑domain correlation often create analyst fatigue and lengthen mean time to respond (MTTR). Scalability becomes an issue in hybrid environments with distributed cloud workloads and mixed OS fleets, producing coverage gaps. These shortcomings point to the need for cross‑domain visibility and automated correlation to improve detection fidelity and reduce manual triage.
Because EDR centers on agents and host forensics, teams commonly augment it with additional telemetry—network sensors, cloud logs, and identity signals—to close blind spots and speed detection across the attack surface. That broader approach is the core promise of XDR, defined next.
What is Extended Detection and Response?
Extended Detection and Response (XDR) is a platform‑level approach that aggregates telemetry from endpoints, network, cloud, identity, and email to enable cross‑domain correlation and coordinated response. XDR normalizes diverse data sources, applies AI/ML to link related events, and orchestrates containment actions across domains so an alert in one area can trigger automated remediation elsewhere. The enterprise benefit is higher‑confidence detection and faster containment through unified visibility and playbook‑driven automation, reducing dwell time and alert noise.
XDR expands coverage across five primary telemetry domains:
- Endpoints
- Network traffic and telemetry
- Cloud logs and workloads
- Identity and authentication systems
- Email and collaboration signals
Combining these sources reveals attack chains—like a compromised cloud credential that later leads to endpoint lateral movement—that EDR alone may not connect. Real‑world XDR deployments show how these capabilities map to operational needs and vendor differentiation. The ShieldWatch XDR Platform, for example, pairs Agentic AI with a 24/7 SOC to unify endpoints, network, cloud, and identity while offering rapid deployment and retroactive log analysis. That example helps make XDR capabilities tangible for enterprise environments.
How does XDR expand security beyond endpoints?
XDR widens the lens by ingesting telemetry from network appliances, cloud services, identity providers, and email gateways alongside endpoint agents, then linking related indicators into a single incident view. Cross‑source correlation can turn a suspicious cloud login, an anomalous network transfer, and an endpoint process spawn into one high‑confidence incident instead of three isolated alerts. That multi‑perspective approach reduces blind spots and uncovers attack patterns—supply‑chain compromise or stealthy lateral movement—that endpoint‑only data may miss. The broader scope improves detection fidelity and helps teams prioritize incidents with real contextual relevance.
Correlating events across domains also enables more surgical responses: for example, revoking a compromised credential at the authentication layer while isolating affected hosts, which shortens containment time and minimizes business impact.
What role do AI and automation play in XDR?
AI and automation are central to XDR’s ability to cut noise and speed response. Machine learning models run at scale to correlate signals across telemetry domains, surface high‑fidelity alerts, and assign confidence scores. SOAR‑driven workflows then execute containment steps—network segmentation, cloud access revocation, endpoint isolation—based on predefined playbooks. This human‑AI collaboration removes routine triage work and lets analysts focus on investigation and threat hunting. By automating repeatable actions and prioritizing alerts, AI and SOAR lower mean time to detect and mean time to contain.
Automated correlation and playbook‑driven remediation produce consistent incident handling, which can be tuned to meet compliance and operational SLAs and further strengthen enterprise resilience.
What are the Key Differences Between XDR and EDR?
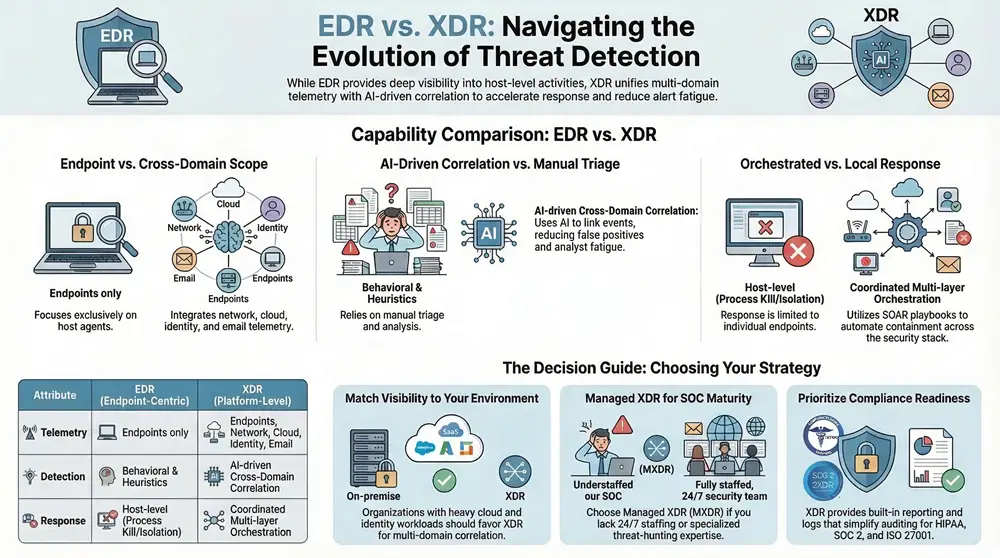
Comparing XDR and EDR comes down to scope, data sources, detection approach, response orchestration, and deployment tradeoffs—factors that shape SOC workflows and risk reduction. In short: EDR focuses on endpoint telemetry and host‑level response, while XDR aggregates multi‑domain telemetry and orchestrates cross‑layer remediation. The table below summarizes those distinctions to help practitioners evaluate architectural choices and expected operational outcomes.
That comparison highlights that broader telemetry and automated orchestration are the main differentiators—and they explain why XDR typically reduces false positives and MTTR versus endpoint‑only solutions.
How do scope and data sources differ between XDR and EDR?
EDR depends on endpoint agents and host telemetry for deep visibility into process execution, file changes, and host artifacts. XDR augments those agents with network telemetry, cloud audit logs, identity events, and email signals to build a holistic view of attacker behavior across layers. The expanded dataset lets XDR detect correlated activity—such as a compromised cloud credential used to deliver payloads to endpoints—that EDR may not link effectively. In practice, those extra sources shrink blind spots and improve detection fidelity by exposing lateral movement and privilege escalation across systems.
Moving from endpoint‑only to multi‑domain telemetry shifts detection from isolated host alerts to contextual incidents that reflect attacker campaigns rather than discrete events.
What distinguishes detection and response capabilities in XDR vs EDR?
EDR generally provides strong host‑level detections and manual or semi‑automated remediation—process kills, host isolation, or rollback—that work well for endpoint‑contained incidents but often require manual cross‑system coordination. XDR, paired with SOAR, enables automated, coordinated responses across identity, cloud, network, and endpoints—actions like credential revocation, network flow blocking, and instance isolation within a single orchestrated playbook. This coordinated model reduces SOC workload and shortens MTTR by executing containment steps concurrently. Higher detection fidelity from cross‑domain correlation also raises confidence that automated actions target real incidents rather than false positives.
Together, these capabilities move incident handling from isolated endpoint fixes to an orchestrated containment strategy that lowers operational overhead and business disruption.
What are the Benefits of XDR Over EDR for Enterprises?
XDR delivers measurable enterprise benefits: better detection quality, less alert fatigue, and streamlined operations through automation and unified investigations. By correlating multi‑domain telemetry and applying AI‑driven prioritization, XDR speeds detection and enables coordinated response, cutting dwell time and investigation costs. The table below links common XDR features to business outcomes so decision‑makers can see how technical capabilities translate into value.
How does XDR enhance threat detection and response speed?
XDR speeds detection by correlating signals across telemetry domains and using AI to surface high‑confidence incidents, reducing time analysts spend chasing low‑value alerts. Automated playbooks can run containment actions immediately or with minimal approval, lowering mean time to contain and shrinking attacker dwell time. For example, linking an anomalous identity event to endpoint execution can trigger credential revocation and host isolation in a single coordinated workflow—actions that would take much longer if done manually. The combined effect is faster detection, more accurate triage, and quicker remediation.
Better prioritization ensures SOC resources focus on real threats, increasing security throughput and reducing operational cost per incident.
In what ways does XDR simplify security operations and scalability?
XDR simplifies operations by consolidating alerts into unified incident views and reducing reliance on multiple consoles and manual cross‑tool correlation. Pre‑built SOAR workflows and standardized playbooks accelerate time to value and create repeatable remediation patterns, while automated onboarding and retroactive analysis lower deployment friction. For teams without mature 24/7 SOC capabilities, Managed XDR (MXDR) provides outsourced detection, threat hunting, and response with agreed SLAs, easing hiring and retention pressures. Overall, XDR and managed models scale more gracefully than point solutions, letting security teams maintain coverage across hybrid and cloud environments without linear headcount growth.
Those operational efficiencies reduce total cost of ownership and make enterprise‑grade detection attainable for mid‑market and larger organizations alike.
How Does ShieldWatch XDR Platform Deliver Comprehensive Protection?
The ShieldWatch XDR Platform operationalizes XDR with Agentic AI, a 24/7 SOC, and a library of pre‑built SOAR workflows to automate detection and response. The platform unifies endpoints, network telemetry, cloud logs, and identity signals into correlated incidents with automated containment, and offers rapid deployment plus retroactive analysis of up to 90 days of logs. ShieldWatch frames these capabilities to cut false positives, help meet compliance requirements (SOC 2, HIPAA, CMMC 2.0, ISO 27001), accelerate time‑to‑value, and lower operational risk.
Below is a technical feature‑to‑value mapping that shows how ShieldWatch components address common enterprise use cases.
What unique features does ShieldWatch XDR offer?
ShieldWatch combines Agentic AI for automated correlation and prioritization with a 24/7 SOC to ensure continuous monitoring and expert investigation support. The platform’s 150+ pre‑built SOAR playbooks enable fast, repeatable containment across endpoints, network, and cloud, while retroactive analysis of up to 90 days of logs accelerates investigations and shortens time to remediate newly discovered threats. ShieldWatch also focuses on cutting false positives—an important operational metric—and provides built‑in compliance tooling for standards such as SOC 2, HIPAA, CMMC 2.0, and ISO 27001. Together, these features create a turnkey XDR experience that addresses detection needs and enterprise governance requirements.
How does ShieldWatch integrate AI, SOC, and SOAR for autonomous security?
ShieldWatch runs an ingest → correlate → triage → automate → human‑review pipeline: ingest diverse telemetry, apply Agentic AI to correlate and score incidents, execute SOAR playbooks for automated containment, and escalate complex cases to the 24/7 SOC for analyst review. This workflow combines machine‑scale analysis with human judgment—automating actions where confidence is high and routing nuanced decisions to people. Continuous monitoring and retroactive analytics close investigation loops and enable iterative tuning of detection models and playbooks. The result is an autonomous posture that reduces manual triage, speeds containment, and preserves an auditable trail for compliance.
This integrated model supports internal SOC teams and managed service partners, giving operational flexibility for organizations at different maturity levels.
How to Choose Between EDR, XDR, and Managed XDR Services?
Choosing among EDR, XDR, and Managed XDR (MXDR) comes down to visibility needs, SOC maturity, cloud footprint, compliance obligations, and budget. Use the checklist below to match options to your risk profile and operational capabilities, and consider Managed XDR when you need 24/7 coverage or specialized threat hunting.
- Visibility Needs: If you run cloud workloads, identity services, and complex networks, favor XDR for multi‑domain telemetry and correlation.
- SOC Maturity: If you lack 24/7 coverage or seasoned threat hunters, consider Managed XDR to outsource detection and response.
- Compliance Requirements: When regulatory reporting and audit readiness are mandatory, choose solutions with built‑in compliance controls and reporting.
- Budget and TCO: Evaluate total cost of ownership, including staffing and integration; XDR often reduces operational overhead despite broader tooling scope.
- Time to Value: If you need quick onboarding and historical context, prefer platforms that offer rapid deployment and retroactive log analysis.
What factors determine the right solution for your organization?
Key factors include asset mix (endpoints versus cloud workloads), attack surface complexity, existing telemetry coverage, SOC staffing, and regulatory obligations. Organizations with distributed workforces and hybrid clouds typically benefit from XDR’s multi‑domain correlation to detect complex attacks, while teams with mature EDR practices and mostly on‑premise endpoints may keep EDR as a strong baseline. SOC staffing and 24/7 triage capability are critical—without continuous coverage, incidents can dwell longer and cause greater impact. Budget planning should factor analyst time and operational costs, since automation and managed services can materially change cost profiles.
Use these considerations to build a roadmap: mature EDR first, add XDR for broader visibility, and adopt Managed XDR where continuous SLAs and proactive hunting are required.
What advantages do Managed XDR services provide?
Managed XDR delivers 24/7 SOC expertise, continuous threat hunting, and operational SLAs without the full cost of building an in‑house team—especially valuable for mid‑market organizations and MSPs. Managed services reduce hiring and retention burdens, speed time to value with pre‑built playbooks and deployment processes, and provide predictable operating models with defined response expectations. For organizations facing skill shortages or needing immediate detection improvements, Managed XDR offers a practical path to enterprise‑grade defenses and consistent incident handling.
When evaluating Managed XDR providers, prioritize integration breadth, playbook completeness, retroactive analysis capability, and demonstrated metrics for alert reduction and MTTR improvement to ensure the service meets operational goals.
Frequently Asked Questions
What are the key considerations when transitioning from EDR to XDR?
Transitioning to XDR requires a clear assessment of your current posture and visibility gaps across endpoints, network, and cloud. Verify that the XDR solution integrates with existing tools and workflows, and plan training so your team can use new capabilities effectively. Factor in deployment sequencing, data normalization, and compliance alignment to smooth the transition and capture XDR’s benefits more quickly.
How can organizations measure the effectiveness of their XDR implementation?
Measure XDR effectiveness with KPIs such as mean time to detect (MTTD), mean time to respond (MTTR), and false positive rates. Also track incidents detected across multiple domains, speed and success rate of automated responses, and the time saved in analyst triage. Regular post‑incident reviews and threat‑hunting results provide qualitative insight into overall impact and tuning opportunities.
What types of organizations benefit most from Managed XDR services?
Managed XDR is ideal for mid‑sized organizations and teams that lack a full in‑house SOC or deep threat‑hunting expertise. Companies with hybrid cloud environments or constrained security talent gain immediate coverage, access to expert analysts, and operational SLAs through Managed XDR—delivering enterprise‑grade detection and response without large upfront hiring costs.
What role does compliance play in choosing between EDR and XDR?
Compliance influences the choice because regulatory requirements often dictate visibility and reporting needs. XDR’s broader telemetry and built‑in reporting typically make audits easier for frameworks like HIPAA or PCI‑DSS. If compliance and detailed evidence are mandatory, favor solutions that provide comprehensive logs, standardized controls, and audit‑ready reporting.
How does the cost of XDR compare to traditional EDR solutions?
XDR can carry a higher license cost than standalone EDR because it covers more telemetry and automation. However, XDR often lowers total cost of ownership by consolidating tools, reducing manual triage, and improving analyst efficiency. Evaluate both initial investment and long‑term operational savings—automation and managed services frequently offset higher tooling costs.
What are the common challenges organizations face when implementing XDR?
Common challenges include integrating diverse telemetry sources, normalizing data, and tuning detection rules to minimize false positives. Change management and training are important as staff adapt from EDR workflows to cross‑domain incident handling. Finally, organizations must commit resources to optimize and maintain the XDR environment to realize its full value.
Conclusion
Choosing between XDR and EDR comes down to the visibility you need and the operational model you can sustain. XDR’s multi‑domain telemetry and automated response improve detection fidelity and reduce operational overhead compared with endpoint‑only approaches, while EDR remains a critical foundation for host‑level visibility and forensics. Use a staged approach—mature EDR, add XDR for broader coverage, and consider Managed XDR where continuous SLAs and advanced hunting are required—to align security controls with your risk and budget. Explore our resources to find the right path for your organization’s security needs.




Refer friends and colleagues—get paid for every signup!
Expliciet materiaal is beschikbaar op verschillende adult websites voor
vermaak. Kies altijd voor betrouwbare adult sites.
Review my website ONLINE VIAGRA PHARMACY