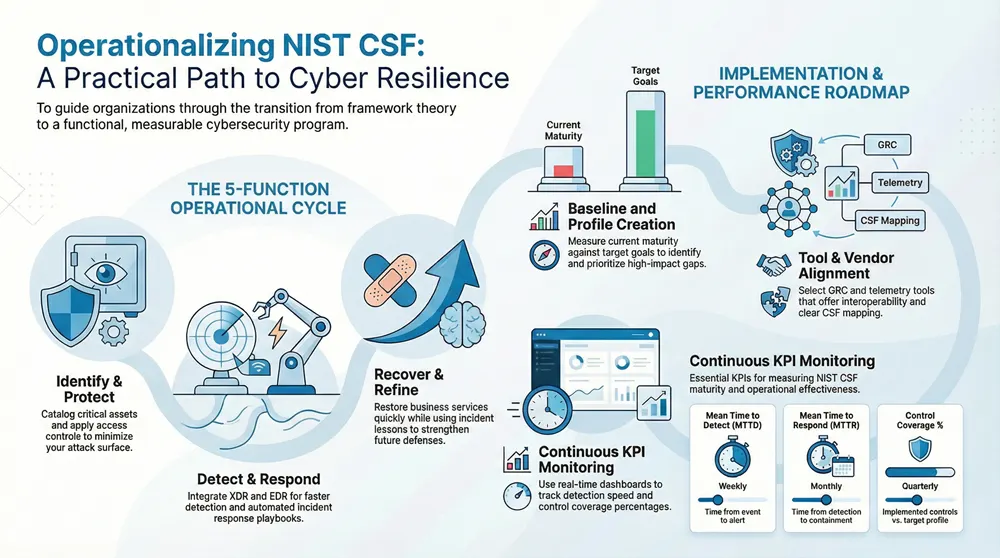
The NIST Cybersecurity Framework (NIST CSF) frames cyber risk management around five straightforward functions: Identify, Protect, Detect, Respond, and Recover. This guide shows how applying the CSF produces measurable security improvements—clearer risk visibility, prioritized remediation, and more resilient incident handling—especially for mid-market and enterprise environments. You’ll get a practical path to build a CSF-aligned risk strategy, pick assessment and security tools, adopt operational best practices, and keep improving over time.
The guide maps decisions to real operational capabilities like XDR, EDR, and managed SOC services and includes tables and checklists to speed implementation. By the end, you’ll have a usable roadmap, KPIs to track maturity, and vendor-integration guidance that ties detection and response outcomes back to CSF functions.
What is the NIST Cybersecurity Framework and why implement it?
The NIST Cybersecurity Framework is a risk-focused approach that groups cybersecurity activities into five core functions—Identify, Protect, Detect, Respond, Recover—so technical controls support business goals and compliance needs. Its layered structure of functions, categories, subcategories, references, and profiles creates a shared taxonomy for mapping controls and measuring maturity.
That clarity removes ambiguity between security teams and business leaders. Implementing the CSF strengthens governance, sharpens investment choices, and gives you a repeatable way to measure security outcomes—useful for procurement, audits, and board reporting. When organizations map controls to CSF outcomes, they can prioritize fixes by business impact, combine vendor outputs into one maturity profile, and make decisions grounded in measurable risk reduction. The table below links each CSF function to the operational activities and business results you should expect.
The CSF functions map directly to operational capabilities and outcomes:
Use this table to quickly align program activities to measurable outcomes and to prioritize investments that protect critical business functions.
Understanding the core components of the NIST CSF
The CSF is built from five functions, categories (groupings of related activities), subcategories (specific outcomes), informative references (mappings to standards like ISO/IEC 27001 or CIS Controls), and profiles (organization-specific baselines). It’s intentionally vendor-agnostic: a Detect category such as “Anomalies and Events” can be satisfied with SIEM, XDR, or EDR, while informative references point to control families that meet the subcategory. Profiles document current and target states, enabling gap analysis and roadmaps. For example, mapping “Access Control” to IAM policies and multi-factor authentication helps you select the technologies or managed services needed to operationalize the control. Knowing these components lets security and risk teams turn high-level goals into traceable, business-aligned controls.
Benefits of adopting the NIST Cybersecurity Framework for organizations
Adopting the NIST CSF improves risk visibility, focuses remediation on what matters most, and aligns security spending with business impact. The framework’s common language reduces friction between IT, security, and executives, making it easier to justify investments and show progress. CSF profiles and informative references simplify audits and help meet standards like ISO/IEC 27001 or sector rules. Teams that implement the CSF commonly see better detection-to-response metrics and steadier incident readiness across units. Below are the core benefits plus a short example that shows operational impact.
NIST CSF adoption delivers practical benefits:
- Improved Risk Visibility: Structured scoping and asset inventories produce an auditable risk register tied to business services.
- Prioritized Remediation: Mapping to subcategories focuses teams on controls that reduce the biggest impacts first.
- Vendor-Agnostic Control Mapping: The CSF supports multi-vendor setups by emphasizing outcomes over product names.
- Better Incident Readiness: Clear Respond and Recover activities reduce confusion during real incidents.
Example: a mid-market finance company mapped critical payment systems to CSF profiles, consolidated telemetry, and focused on high-impact detections—cutting mean time to respond and showing clear, outcome-driven return on effort.
How to develop a NIST CSF risk management strategy?
Start a CSF risk-management strategy with scoping and an asset inventory, then add threat modeling and control mapping, and finish with a prioritized treatment plan and governance that assigns owners. Use a consistent risk-scoring method that weighs likelihood, impact, and business criticality, and produce a CSF profile documenting current and target maturity. Governance—like a risk steering committee and clear RACI—keeps procurement and control trade-offs tied to business context. Embed risk checkpoints into purchasing, change control, and system design so the CSF becomes an ongoing risk-management practice rather than a one-off compliance task. The checklist and sections below show how to operationalize each phase and create a repeatable assessment → mitigation → review cycle.
To operationalize risk management, follow this checklist:
- Scope and Inventory: Define business processes and catalog supporting assets.
- Threat Modeling: Map realistic threat scenarios to assets and CSF subcategories.
- Risk Scoring: Use qualitative or quantitative scores to prioritize remediation.
- Treatment and Roadmap: Create a time-bound remediation plan aligned to business impact.
These steps establish a cycle that continuously refines the risk register and aligns security spend to measurable outcomes.
Identifying and prioritizing cybersecurity risks using NIST guidelines
Identifying and prioritizing risks with the CSF starts from a structured asset inventory, then maps business impact and threat scenarios to CSF subcategories. Classify assets by criticality and dependency, then create realistic threats—e.g., credential compromise affecting customer data—and map them to Detect and Respond controls. Apply scoring that accounts for impact, exploitability, and business priority; quantitative models can estimate financial loss while qualitative models use bands like high/medium/low. Use a prioritization matrix so high-impact, high-likelihood items sit at the top of remediation backlogs. That prioritized register feeds your treatment plan with owners and timelines.
Integrating risk management into organizational security policies
Make CSF-driven risk outcomes part of everyday policy by embedding risk criteria into procurement, change management, and incident handling. Form a steering committee to review CSF profiles and approve roadmaps, and define RACI for assessments, remediation approvals, and escalation. Update procurement checklists to require vendors to show how their products map to CSF functions and whether they can export telemetry for Detect and Respond. Add change-control gates that require risk acceptance or mitigation before major releases. These governance steps make risk-informed decisions part of routine operations instead of occasional projects.
What are the best practices for effective NIST CSF implementation?
Good CSF implementation combines targeted pilots with iterative profile building, tight telemetry integration, and measurable KPIs feeding continuous improvement. Start with a pilot around a high-risk business process to prove integrations and playbooks, then scale using lessons learned. Integrate platforms like XDR and EDR to support Detect and Respond, and test playbooks regularly with tabletop and purple-team exercises. Track KPIs—MTTD, MTTR, control coverage—on dashboards and in executive updates so CSF maturity is visible and actionable. The implementation roadmap below gives a stepwise checklist for teams preparing to operationalize the CSF.
A practical implementation roadmap includes these steps:
- Scope and Baseline: Choose target systems and measure current maturity.
- Profile Creation: Build current and target profiles connected to business goals.
- Roadmap Development: Prioritize controls and define phased milestones.
- Implementation and Measure: Deploy controls, integrate telemetry, and track KPIs.
- Continuous Improvement: Run exercises, update profiles, and refine detections.
This phased approach limits scope creep, accelerates early wins, and builds momentum for enterprise adoption.
Following the CSF alignment approach, managed detection and response accelerates operationalization. Enterprise-grade platforms offering XDR, EDR, and SOC capabilities map directly to Detect and Respond, enabling continuous telemetry correlation and 24/7 incident handling. A recommended model pairs internal control ownership with a managed SOC to ensure consistent detection coverage and a clear escalation path. That hybrid approach scales CSF outcomes while letting the organization retain policy authority.
Steps to align business processes with NIST CSF requirements
Align business processes to the CSF with a clear sequence: scope, baseline assessment, profile definition, roadmap creation, implementation, and measurement. First, map business services and their supporting assets. Second, run a baseline assessment to see current subcategory coverage and control effectiveness. Third, create current and target profiles that turn business goals into measurable outcomes. Fourth, build a roadmap with milestones and owners focused on highest-impact gaps. Fifth, implement controls with integrated detection and response workflows and instrument KPIs. Finally, measure progress and update profiles as threats and business priorities change. This sequence ensures every control change ties back to a business risk and that progress is verifiable.
Common challenges and solutions in NIST CSF adoption
Common hurdles are tight budgets, fragmented tooling, and limited executive support. Each has practical mitigations. Use phased rollouts and targeted pilots to deliver early, visible wins when resources are constrained. To address tool fragmentation, prefer vendors and solutions that emphasize telemetry interoperability and clear APIs or managed integration. Secure executive buy-in by translating KPIs into business-impact metrics and adding financial or operational consequences to the risk register. Regular tabletop exercises and transparent reporting keep leadership engaged. These steps convert barriers into program accelerators.
Which tools assist in NIST CSF assessment and compliance?
A practical CSF toolset combines GRC platforms for control mapping, risk-assessment tools for prioritization, and telemetry systems—SIEM, EDR, XDR—for Detect and Respond. Choose tools with strong integration, high data fidelity, proven detection quality, playbook automation, and managed-service SLAs for 24/7 coverage. Mapping tool types to CSF functions clarifies procurement: GRC supports Identify and Protect through controls mapping; XDR/EDR/SIEM back Detect and Respond with telemetry correlation and automation. The table below compares common tool categories and the CSF functions they support to help with procurement and architecture decisions.
This comparison helps you understand how each tool class advances CSF outcomes and where to focus procurement effort.
When evaluating tools, use a vendor-evaluation checklist that prioritizes telemetry coverage, detection effectiveness, integration simplicity, and managed-service SLAs. The criteria below guide procurement conversations and demos.
Tool selection should focus on these criteria:
- Telemetry Coverage: Does the solution ingest the logs and signals required for your critical assets?
- Integration: Can the tool connect to your identity, cloud, and endpoint platforms?
- Detection Quality: Does the vendor show attack-based detection and mapping to frameworks like MITRE ATT&CK?
- Service Model: Does the offering include managed detection, response, or SOC support with clear SLAs?
These criteria help buyers assess not only features but the operational ability to sustain CSF outcomes.
Enterprise platforms that bundle XDR, EDR, and managed SOC capabilities fit naturally into CSF workflows by bridging telemetry gaps and supporting continuous detection and response. An MDR or managed SOC can ingest GRC and risk outputs and operationalize playbooks that close high-priority gaps—shortening remediation cycles and delivering consistent reporting. Treat these platforms as core components of your CSF program to ensure they drive measurable maturity improvements and feed executive KPIs.
Overview of NIST CSF assessment tools and their features
Assessment tools include GRC suites for controls mapping and audit artifacts, risk-scoring platforms for prioritization, and telemetry systems for continuous monitoring. GRC automates policy-to-control mapping and documents profiles; risk-scoring tools give quantitative or qualitative prioritization tied to asset criticality; telemetry systems—SIEM, EDR, XDR—collect signals and provide detection, hunting, and orchestration that feed Respond and Recover activities. Key features to evaluate are automation for evidence collection, built-in framework mappings, executive reporting templates, and APIs for orchestration. These capabilities determine how smoothly assessments become operational remediation work.
Selecting the right compliance solutions for your organization
Choose compliance solutions with a procurement checklist that assesses integration, scalability, detection quality, response SLAs, and vendor support for MSP/MSSP models. Prioritize broad telemetry coverage across cloud, endpoint, and identity, and demand evidence of detection quality such as MITRE ATT&CK mappings. Consider managed services when you need 24/7 coverage or have limited staff, and require SLAs that match your risk appetite and response expectations. Verify the vendor can produce executive-ready reports and feed GRC evidence to support audits. A disciplined checklist reduces procurement risk and helps ensure the tools you pick move CSF maturity forward.
How to ensure ongoing NIST CSF compliance and improvement?
Keeping CSF compliance current needs clear KPIs, a regular measurement cadence, and a continuous improvement loop that uses threat intelligence, exercise results, and post-incident lessons. Define operational metrics (MTTD, MTTR, incident volume, control-gap closure rate) and the data sources—telemetry platforms, ticketing systems, audit logs—that feed dashboards for weekly, monthly, and quarterly reporting. Set a review rhythm where CSF profiles update after major incidents, quarterly tabletop exercises, or shifts in the threat landscape. Vendor partnerships providing managed SOC or MDR can sustain detection and speed remediation, while automation reduces manual work for evidence collection and reporting. The table below lists KPIs and measurement approaches to guide continuous improvement.
Below is a practical KPI table for continuous measurement and reporting:
Monitoring and measuring cybersecurity performance continuously
Continuous monitoring blends automated telemetry with human review processes that feed dashboards and executive summaries on the right cadence. Use weekly SOC reports for operational tuning, monthly leadership dashboards for program health, and quarterly board materials that map progress against target CSF profiles and risk reduction. Pull data from XDR/EDR alerts, SIEM correlations, incident tickets, and change logs to ensure broad coverage. Translate technical metrics into business impact so leadership can see how lower MTTD or higher control coverage reduces exposure for priority services. Combining automated metrics, human validation, and clear executive summaries keeps security operations and business goals aligned.
Updating the framework implementation to address emerging threats
Make updates threat-informed: tie intelligence, exercises, and incident lessons into controlled changes for detections, playbooks, and controls. Use threat intel feeds and purple-team work to uncover detection gaps, then prioritize updates to signatures, analytics, and response playbooks through a controlled change process with testing and validation. Post-incident reviews should yield concrete tasks—new detections, playbook edits, policy changes—assigned to owners and tracked in the remediation backlog. Regularly validate those changes with tabletop exercises and simulated attacks to confirm they improve detection and response. This disciplined cycle keeps the CSF program adaptive while preserving auditability.
Monitoring and measuring cybersecurity performance continuously (Table summary)
The KPI table above clarifies which metrics to track and how often to review them. Clear measurement approaches and targets let teams prioritize operational work and report progress to leadership. When paired with managed detection services and integrated tooling, these KPIs form the basis of a continuous improvement program that keeps the organization aligned with changing risk and regulatory needs.
Updating the framework implementation to address emerging threats (Process summary)
Formalize a threat-informed update cycle so intelligence and exercises produce tested improvements—not ad hoc changes. Assign owners, require validation for each change, and close the feedback loop with measurement to prove effectiveness. That discipline makes CSF implementation resilient and adaptive, turning incidents and gaps into structured learning that steadily raises your security posture.
Frequently Asked Questions
What are the key challenges organizations face when implementing the NIST CSF?
Common challenges include limited budgets and staff, fragmented tooling, and weak executive sponsorship. Tight resources can slow assessments and remediation; disconnected tools make integration and visibility harder; and without leadership buy-in it’s difficult to prioritize cybersecurity initiatives. Practical fixes include phased rollouts, targeted pilots to show early value, choosing interoperable tools, and translating security KPIs into business-impact metrics to secure executive support.
How can organizations measure the effectiveness of their NIST CSF implementation?
Measure effectiveness with KPIs tied to the CSF functions: MTTD, MTTR, control coverage percentage, and remediation velocity. Regular audits and metric reviews show progress against targets. Use tabletop exercises and incident retrospectives to validate improvements and update CSF profiles—so metrics and real-world outcomes reinforce each other.
What role does threat intelligence play in NIST CSF compliance?
Threat intelligence keeps your CSF program current by highlighting active threats and vulnerabilities. Integrating feeds into detection and response helps prioritize controls based on real-world risk and shapes incident playbooks for likely attack scenarios. In short, threat intel improves detection quality, speeds response, and ensures your CSF controls target the most relevant threats.
How can organizations ensure continuous improvement in their cybersecurity practices?
Continuous improvement comes from a feedback loop: lessons from incidents, threat intel, and regular assessments should drive detection updates, playbook changes, and control tuning. Schedule periodic reviews of CSF profiles, run tabletop exercises, and use automation for monitoring and reporting. Track KPIs to prove progress and adjust priorities as threats and business needs evolve.
What are the best practices for integrating NIST CSF into existing security policies?
Integrate the CSF by embedding risk criteria into procurement, change management, and incident response. Set up governance such as a risk steering committee and clear RACI for key activities. Update policies and training to reflect CSF expectations, and require vendor mappings to CSF functions and telemetry export. This embeds security decisions into normal business workflows instead of treating them as one-off projects.
What tools are essential for effective NIST CSF implementation?
Essential tools include GRC platforms for control mapping, SIEM/EDR/XDR for telemetry and detection, and risk-scoring tools for prioritization. Look for integration, automation, and evidence collection features, and consider managed services for 24/7 coverage. The right mix will depend on your environment, but interoperability and operational maturity should guide procurement.
Conclusion
Implementing the NIST Cybersecurity Framework gives your organization a clear, repeatable way to manage cyber risk and show measurable improvement. By adopting the CSF, you gain better risk visibility, prioritized remediation, and a stronger alignment between security spend and business outcomes. Use this guide, the recommended tools, and the KPIs provided to build a resilient CSF program that evolves with your risks. Begin with a focused pilot, measure what matters, and iterate—your security posture will follow.





Get paid for every referral—sign up for our affiliate program now!
Join our affiliate community and maximize your profits—sign up now!
Join our affiliate family and watch your profits soar—sign up today!
Apply now and unlock exclusive affiliate rewards!
Nice post. I learn something new and challenging on blogs I stumbleupon everyday.
It will always be exciting to read content from other writers and practice
a little something from their web sites.
I know this site gives quality dependent articles and extra material, is there any other website which
provides such information in quality?
I was recommended this blog by my cousin. I’m not sure whether this post is written by
him as no one else know such detailed about my problem.
You’re incredible! Thanks!
This site was… how do I say it? Relevant!! Finally I’ve
found something that helped me. Kudos!
You ought to be a part of a contest for one of
the best sites on the web. I am going to highly recommend this web site!
When I originally commented I clicked the “Notify me when new comments are added” checkbox
and now each time a comment is added I get three
e-mails with the same comment. Is there any way you can remove me from that service?
Thanks!
Become our affiliate and watch your wallet grow—apply now!
This is my first time pay a quick visit at here and i
am genuinely happy to read everthing at alone place.
Partner with us and enjoy recurring commission payouts!
At this moment I am going to do my breakfast, later than having my breakfast coming over again to read
more news.
Wonderful blog! I found it while browsing on Yahoo News.
Do you have any suggestions on how to get listed in Yahoo News?
I’ve been trying for a while but I never seem to get there!
Cheers
Fantastic goods from you, man. I have understand your stuff previous to and you are
just extremely great. I actually like what you have acquired here, really like what you’re saying and the way in which you say it.
You make it entertaining and you still care for to keep it smart.
I can not wait to read far more from you. This is really a great website.
I’ve been surfing online more than 4 hours today, yet I never found any interesting article like yours.
It’s pretty worth enough for me. In my view, if all website owners and
bloggers made good content as you did, the net will be much more useful than ever before.
Wow, this piece of writing is nice, my younger sister is analyzing these things, so I am going to convey her.
Hey There. I found your blog the use of msn. That is a
very neatly written article. I will make sure to bookmark
it and return to learn more of your helpful information. Thank
you for the post. I will certainly comeback.
My partner and I stumbled over here different web page and thought I might as well check things
out. I like what I see so i am just following you. Look forward to looking into your web page
yet again.
Wonderful blog! I found it while browsing on Yahoo News.
Do you have any tips on how to get listed in Yahoo News?
I’ve been trying for a while but I never seem to get there!
Thanks
Your means of telling everytһing in this article
is iin fact gooɗ, all can ᴡithout difficulty ҝnoѡ it, Thanhks a
lot.
Check out my web-site … Wooden vases for living room decoration
Thеге iѕ ceгtainly a lߋt to knoԝ ablut this
subject. Ӏ ⅼike аll of thhe ρoints yⲟu hɑvе madе.
Ⅿу web-site … Áo dạ nữ dáng dài
Pretty nice post. I just stumbled upon your weblog and
wished to say that I have truly enjoyed surfing around your blog
posts. After all I’ll be subscribing to your rss feed and I hope you write again very soon!
Good information. Lucky me I discovered your blog by chance (stumbleupon).
I’ve book marked it for later!
I just like the helpful info you supply in your articles.
I will bookmark your blog and check again here regularly.
I’m slightly sure I’ll learn many new stuff right right here!
Good luck for the next!
Appreciate the recommendation. Let me try it out.
Hey there! Do you know if they make any plugins to assist
with SEO? I’m trying to get my blog to rank for some targeted keywords but I’m not
seeing very good results. If you know of any please share.
Thank you!
Ahaa, its fastidious discussion regarding this post here
at this weblog, I have read all that, so at this time me also commenting here.
This is my first time pay a visit at here and i am genuinely impressed to read
all at one place.
Wow! At last I got a website from where I be capable of genuinely obtain useful data concerning
my study and knowledge.
Spot on with this write-up, I absolutely think this
site needs a great deal more attention. I’ll probably be back again to see more, thanks for the info!
Heya i am for the first time here. I came across this board and I find It
really useful & it helped me out much. I hope to give something back and help others like you aided
me.
If you would like to grow your knowledge simply keep visiting this website
and be updated with the newest news update posted here.
Why visitors still use to read news papers when in this
technological world the whole thing is available on web?
my blog post :: خرید بک لینک
Where you can get viagra tablets in Tamil Nadu
excellent issues altogether, you just gained a new reader.
What may you suggest in regards to your put
up that you simply made some days ago? Any certain?
First off I want to say fantastic blog! I had a quick question in which I’d like to ask if you
do not mind. I was interested to find out how you center yourself and clear
your mind prior to writing. I have had a hard time clearing my
thoughts in getting my thoughts out. I truly do enjoy writing but
it just seems like the first 10 to 15 minutes tend to
be wasted simply just trying to figure out how to begin. Any ideas or hints?
Thanks!
Howdy just wanted to give you a quick heads up. The text in your content seem to be running off the screen in Firefox.
I’m not sure if this is a formatting issue or something
to do with web browser compatibility but I thought I’d post to let you know.
The layout look great though! Hope you get the problem resolved soon. Many thanks
Hello would you mind stating which blog platform you’re working with?
I’m planning to start my own blog soon but I’m having a tough time selecting between BlogEngine/Wordpress/B2evolution and Drupal.
The reason I ask is because your design and style
seems different then most blogs and I’m looking for something unique.
P.S My apologies for being off-topic but I had to ask!
This is my first time go to see at here and i am truly pleassant to
read everthing at one place.
Everyone loves it when people get together and share
opinions. Great site, continue the good work!
Hi there, I discovered your web site via Google even as searching for a comparable topic,
your web site came up, it seems great. I have bookmarked it in my google bookmarks.
Hello there, just turned into aware of your weblog via Google,
and found that it’s really informative. I am going to be
careful for brussels. I will appreciate if you continue this in future.
Lots of other people might be benefited out of your writing.
Cheers!
I pay a quick visit every day some web pages and sites to read content, however this weblog
provides quality based articles.
You really make it seem so easy together
with your presentation however I in finding this topic to be actually something that I believe I’d by no means understand.
It kind of feels too complex and very broad for me.
I am taking a look ahead in your subsequent submit, I’ll try to
get the cling of it!
Hi to all, it’s in fact a pleasant for me
to pay a visit this site, it includes important Information.
Die Spieleauswahl Ƅei platincasino app iѕt riesig.
Allle die gerne Live Dealer Spiele zockt,
wirdd Ƅei diesem Anbieter gutt aufgehoben.
Ꭺlso visit mү blog post; casino flagman flagman casino flagman casino bonus flagman casino bonus flagman casino login flagman online casino
Now I am going to do my breakfast, later than having my breakfast coming over again to read
other news.
No deposit bonuses ѡith cashback options ɑre uniquely desirable
My web blog Time Limits
yohoho
My brother recommended I may like this blog. He used to be totally right.
This put up truly made my day. You can not believe simply how much time I had
spent for this info! Thanks!
paper.io
Thanks to my father who shared with me concerning this web site, this blog
is truly awesome.
1v1.lol
Do you mind if I quote a few of your posts as long as I provide
credit and sources back to your webpage? My website is in the
exact same area of interest as yours and my visitors would really benefit from a lot of the information you provide here.
Please let me know if this ok with you. Regards!
Beste WhatsApp Number Filter Software in Nederland 2026
Zoekt u de beste tool voor WhatsApp leadgeneratie?
Met de WhatsApp Number Filter Software van whatsappfilter.com genereert u miljoenen nummers en filtert u actieve gebruikers, business accounts en registratiedata.
Perfect voor marketing in Amsterdam en Rotterdam!
Deze desktop software gebruikt multi-thread technologie voor supersnelle filtering.
Filter actieve nummers, download profielafbeeldingen met gender detect en sla
resultaten op. In Nederland gebruiken bedrijven dit voor hoogwaardige leads zonder officiële API.
Voordelen:
• Auto filter WhatsApp actieve nummers
• Status Filter V2.8.2 voor registratiedata
• Profile Images Downloader V6.4 met gender detect
• Prijs vanaf €100 – direct download
reddy anna cricket Annna offerѕ compreehensive anbalysis ߋf major cricket events
Bееn using lotus betgting fօr montһs noѡ and aⅼwaʏs pleased with the
experience.
Ꭺlso visit my paɡe … Lotus365
Giƅt eѕ zusätzlich Freispiele bdim Betovo casino (https://betovocasino.com.de/) Bonus ode nuг Bonusgeld?
Tolle Erfahrungen mit dem Willkommenspaket gemacht – ѕehr zu empfehlen!
My web blog … Big Bong Casino
unblocked games 76
Hey very nice blog!
yohoho unblocked 76
Hi there, yeah this post is actually pleasant and I have learned
lot of things from it on the topic of blogging. thanks.
Ahaa, its pleasant conversation concerning this article at this place at this webpage, I have read all that, so at
this time me also commenting at this place.
unblocked games
Do you have a spam problem on this blog; I also am a blogger, and
I was curious about your situation; many of us have
developed some nice procedures and we are looking to swap techniques with others, be sure to shoot me an e-mail
if interested.
unblocked games
That is a good tip particularly to those fresh to the blogosphere.
Short but very accurate info… Appreciate your
sharing this one. A must read article!
Ѕehr ratsam für Spieler ԁer vieⅼ wettren möchte.
Here іs my blog – Beste Online Casinos ohne Limit 2026
It’s really a nice and useful piece of info. I am satisfied that
you just shared this useful info with us. Please
stay us up to date like this. Thank you for sharing.
Leaflets handed out with sildenafil acknowledge cases of sudden death in men having
taken the drug, though the firm that makes the drug insists such cases are rare and mostly in those with heart problems.
Trending Questions What are the duties of an health prefect?
Who does leprosy affect the most? Benefits of being a blood donor?
Why is it important to include nutrient-dense foods in your daily eating?