XDR Automation: Faster Threat Response and Streamlined Security Workflows for Stronger Cyber Defense
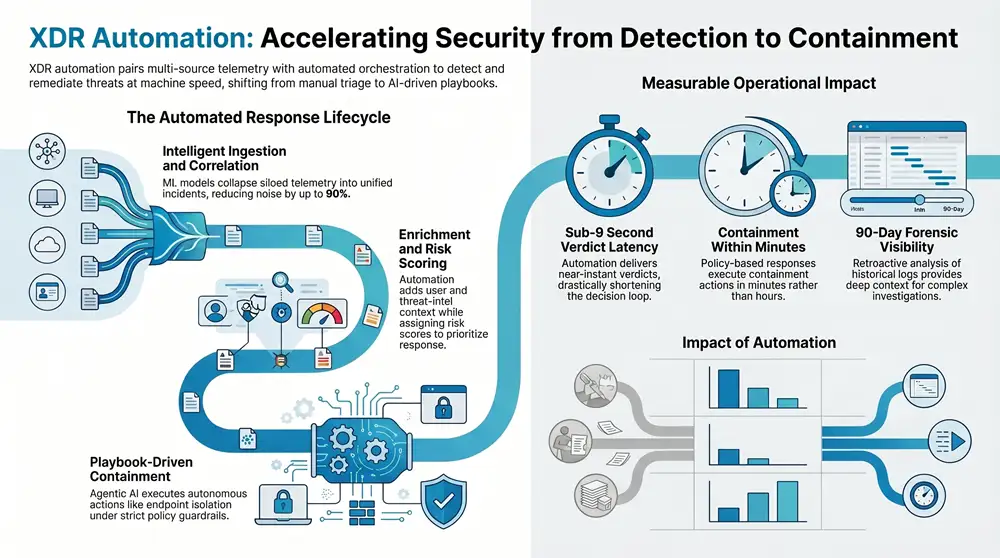
XDR automation pairs extended detection and response telemetry with automated orchestration so security teams detect, prioritize, and act on threats at machine speed. It tackles the day-to-day operational pain of noisy alerts and slow containment by automating triage, enrichment, and policy-driven remediation, letting teams close incidents faster and more consistently. This guide explains how automation shortens mean time to detect and respond, how AI and SOAR playbooks enable safe autonomous actions, where managed XDR delivers operational leverage, and how automation supports compliance.
We walk through core mechanics—telemetry correlation, risk scoring, agentic AI decisioning, and playbook-driven containment—and show measurable outcomes like fewer false positives and faster verdicts. Along the way you’ll get practical implementation guidance, EAV mappings that link features to outcomes, and selective platform examples showing how enterprise-grade XDR augments rather than replaces human oversight. By the end you’ll be able to weigh tradeoffs, understand the technical building blocks of XDR automation, and evaluate solutions for mid-market and enterprise environments.
What Are the Key Benefits of XDR Automation in Cybersecurity?
XDR automation centralizes telemetry from endpoints, network, and cloud, uses correlation and machine learning to surface the riskiest events, and executes policy-based responses to cut manual work and human error. Correlated signals and enriched context allow automated workflows to separate real incidents from noise, deliver actionable evidence quickly, and apply containment consistently. The main benefits are faster detection and response, a lower analyst burden, improved accuracy from ML correlation, and scalable operations that drive down the total cost of security delivery. These outcomes matter most when alert volume blocks proactive hunting and when consistent policy enforcement is needed across hybrid environments.
XDR automation delivers several measurable operational improvements:
- Reduced Mean Time to Respond: Automated triage and playbooks shorten decision loops and speed containment.
- Lower Alert Fatigue: Correlation and suppression collapse duplicates and low-value noise so analysts focus on real risk.
- Higher Detection Accuracy: ML models and threat intel reduce false positives and raise signal-to-noise.
- Operational Scalability: Automation and reusable runbooks let SOC teams handle more telemetry without a proportional headcount increase.
Those benefits show up in platform metrics: some enterprise XDR deployments report up to 90% fewer false positives, sub-9-second average verdicts, containment within minutes, and fast rollouts that enable retroactive analysis of up to 90 days of logs. The next section breaks down how automation compresses mean time to respond.
How Does XDR Automation Reduce Mean Time to Respond?
XDR automation lowers MTTR by creating a fast, repeatable path from detection to containment: ingest telemetry → correlate signals → enrich context → score risk → execute playbook. Automated triage filters and prioritizes alerts so analysts only see high-risk incidents, and enrichment pipelines deliver host, process, user, and threat-intel context without manual lookups. Playbook-driven containment enforces consistent actions—endpoint isolation, network segmentation, credential revocation—based on policy thresholds and preserves audit trails for review. Human time is reserved for exceptions and tuning, letting SOCs shift from backlog-driven firefighting to proactive improvement.
In What Ways Does XDR Automation Minimize Alert Fatigue?
XDR automation reduces alert fatigue by collapsing duplicate signals across EDR, network, and cloud telemetry and applying ML-based risk scoring to suppress low-value noise while surfacing prioritized incidents. Correlation produces unified incidents instead of siloed alerts, and behavioral models catch anomalous patterns that matter. Escalation rules and thresholding remove repetitive manual steps by auto-remediating routine issues and elevating events only when compounded risk factors appear. That frees analysts to focus on hunting and complex investigations, improving detection quality and lowering burnout from repetitive triage.
This EAV table connects common benefit metrics to typical reductions and concrete example values so you can see how automation translates into operational impact. Next, we’ll look at the AI capabilities that power many of these behaviors.
How Does AI Enhance Automated Threat Detection and Response in XDR Platforms?
AI strengthens XDR automation by spotting patterns across large, noisy telemetry sets, predicting likely attacker moves, and running agentic workflows inside clear governance boundaries. ML models classify events, surface anomalies, and produce risk scores that feed orchestration engines; predictive analytics forecast lateral movement or next-step compromise and help prioritize response. Agentic AI brings decisioning, executing multi-step actions under policy guardrails while logging everything for audit. Together, these layers enable faster, more accurate automated responses and let human analysts focus on the hardest investigations.
- Agentic AI Automation: Autonomous agents run sequenced actions when policy thresholds are met, cutting latency while keeping auditable records.
- Machine Learning Correlation: Classification and anomaly detection across EDR, network, and cloud telemetry improve signal clarity and reduce false positives.
- Predictive Analytics: Forecasting likely attack paths prioritizes incidents and helps select adaptive playbooks.
These AI capabilities work together: ML finds the signal, predictive analytics ranks impact, and agentic automation carries out the response. The section below defines agentic AI and describes its governance model.
What Is Agentic AI and Its Role in XDR Security?
Agentic AI describes autonomous agents that perform action sequences—enrichment, containment, remediation—based on policy rules and confidence thresholds. In XDR, agentic agents can isolate endpoints, revoke credentials, or block flows when multiple indicators point to compromise, while creating immutable audit logs. Controls include human-in-the-loop checkpoints for high-impact steps and configurable thresholds that escalate to analysts instead of auto-executing. That balance preserves automation speed while enforcing governance—essential in regulated environments that demand auditability and oversight.
How Do Machine Learning and Predictive Analytics Improve Threat Detection?
Machine learning in XDR handles anomaly detection, event classification, and clustering to expose threats hidden in noisy telemetry. Models ingest telemetry, UEBA signals, and threat intelligence to distinguish benign deviations from malicious behavior and assign confidence scores that guide playbook choice. Predictive analytics extend detection by estimating likely attack routes and recommending preemptive controls to reduce exposure. Continuous retraining from SOC feedback and incident outcomes keeps detection improving over time and lowers false positives, increasing automation effectiveness.
What Are the Capabilities of ShieldWatch XDR Platform in Streamlining Security Workflows?
ShieldWatch’s XDR platform unifies XDR, SIEM, SOAR, UEBA, and threat intelligence with hyper-automation and 24/7 SOC support to turn detection into rapid, auditable action. The architecture ingests multi-source telemetry, applies ML and agentic decisioning, and runs pre-built SOAR workflows to contain incidents consistently across endpoints, cloud, and network. The platform emphasizes fast deployment, retroactive analysis of up to 90 days of logs, and measurable reductions in analyst workload through automation and runbook reuse. Security teams evaluate capabilities by integration breadth, playbook coverage, and the strength of human-AI collaboration—areas where ShieldWatch provides a library of ready-to-run playbooks and continuous SOC-driven tuning.
- Hyper-automation with pre-built SOAR workflows: 150+ playbooks cover common incident types and enable quick response.
- Agentic AI decisioning: Autonomous actions operate under policy guardrails with full audit trails.
- 24/7 SOC integration: Human analysts monitor automation, validate complex incidents, and refine models.
Below is an EAV mapping that links ShieldWatch capabilities to how they operate and the operational benefits and metrics they deliver.
This EAV table shows how specific platform features map to measurable outcomes, helping teams prioritize what drives operational value. The following sections explain how SOAR playbooks automate response and how 24/7 SOC coverage complements automation.
How Do SOAR Workflows and Playbooks Automate Incident Response?
SOAR workflows follow a trigger → enrichment → decision → action pattern where triggers come from correlated telemetry and decisions use policy logic and ML risk scores. Playbooks are templated for common incident classes, customizable for environment-specific controls, and versioned so teams can track changes and measure impact. Conditional logic and integrations enable cross-domain actions—blocking a session, isolating an endpoint, or updating firewall rules—while keeping a single incident record. Metrics like playbook run rate, false-trigger rate, and containment latency drive continuous improvement and governance.
How Does 24/7 SOC Support Enhance Automated Threat Response?
A 24/7 SOC strengthens automation by providing human verification for complex or high-risk incidents, tuning detection models, and updating playbooks based on real adversary behavior. Analysts resolve ambiguity automation can’t safely handle, investigate escalations, and feed findings back into ML training and SOAR logic. That human-AI collaboration reduces drift, ensures responses match business risk appetite, and maintains a feedback loop that improves detection and automated response over time. Real-world cases often show faster remediation when automation handles routine tasks while SOC analysts focus on exceptions.
What Are Managed XDR Services and Their Advantages for Enterprises?
Managed XDR services—often offered as SOC-as-a-Service—bundle platform capabilities with outsourced operational expertise to provide continuous detection, response, and threat hunting. These services offload staffing and day-to-day operations, accelerate time-to-value, and scale security for mid-market and enterprise customers that lack full in-house SOC coverage. The managed model gives access to skilled analysts, standardized playbooks, and ongoing tuning of detection pipelines so organizations can reach mature security operations without matching headcount or tooling spend.
- Operational Expertise on Demand: Skilled analysts and hunters reduce the need to recruit specialized staff.
- Faster Time-to-Value: Pre-configured integrations and playbooks speed deployment and early wins.
- Scalability and Cost Efficiency: A subscription model scales with telemetry volume and organizational needs.
This model suits teams who want to focus internal resources on strategic work while relying on external experts to run continuous detection and response. The next sections cover human-AI collaboration for threat hunting and which industries gain the most value.
How Does Human-AI Collaboration Improve Proactive Threat Hunting?
Human-AI collaboration boosts proactive threat hunting by having automation surface prioritized, context-rich leads so hunters can focus on investigation strategy instead of enrichment chores. Automated triage narrows the scope, while enrichment pipelines deliver telemetry, UEBA signals, and threat intel to speed hypothesis testing. Hunter findings then feed retraining and playbook updates, closing the loop between detection and response. That loop raises the success rate for uncovering sophisticated threats while reserving human creativity for nuanced adversary behavior.
What Industries Benefit Most from Managed XDR and SOC-as-a-Service?
Managed XDR is particularly useful in regulated and distributed industries where compliance, fast incident response, and consistent enforcement matter. Healthcare and government contracting need documented controls and continuous monitoring—capabilities managed XDR provides. Distributed mid-market firms with remote endpoints gain from outsourced SOC expertise and centralized control, and MSPs can extend managed XDR as a differentiated service. Across verticals, the typical benefits are compliance support, faster breach detection, and offloaded operational staffing—making managed XDR both cost-effective and transformational.
How Does XDR Automation Support Compliance with Regulatory Frameworks?
XDR automation supports compliance by automating evidence collection, continuous monitoring, and reporting that map to common control objectives like access logging, detection, and incident response. Automated log retention and tamper-evident audit trails create the forensic artifacts auditors expect, while pre-built reporting templates can be aligned to SOC 2, HIPAA, and CMMC 2.0 controls. Continuous monitoring identifies control failures in near real time, enabling faster remediation and lowering the manual effort of audit evidence gathering. Automation supplements—but does not replace—manual policies, governance decisions, and attestation processes required by auditors.
Why mapping automation to controls matters: automated outputs—alerts, remediation logs, and scheduled reports—serve as evidence during assessments and shorten the time between a control deviation and its remediation, improving overall compliance posture.
What Are the Automated Compliance Features for SOC 2, HIPAA, and CMMC 2.0?
Automated compliance features include continuous monitoring of control-relevant events, role-based audit logging, scheduled evidence collection, and report templates mapped to control objectives. For SOC 2, automation captures and preserves logs, demonstrates consistent incident response, and produces periodic compliance reports. Under HIPAA, access logging and breach-detection playbooks speed notifications and forensic work. For CMMC 2.0, automated monitoring and policy enforcement create traceable records of cybersecurity practices. That said, automation complements—and does not replace—the governance, policy decisions, and attestation steps auditors require for some controls.
How Does Continuous Monitoring Streamline Regulatory Reporting?
Continuous monitoring streamlines reporting by offering scheduled and on-demand exports of control evidence, executive dashboards that summarize posture, and detailed logs for auditors and forensic teams. Automated alerts flag control deviations immediately so teams can remediate with a clear timeline—something auditors value. Typical cadence recommendations include daily health checks, weekly incident summaries, and monthly executive reports, with on-demand exports during audit windows. By delivering both executive summaries and forensic detail, continuous monitoring reduces ad hoc effort and business disruption around audits.
Automated compliance features also improve operational transparency and accelerate remediation cycles. For teams evaluating platforms, ShieldWatch’s unified stack and reporting templates are built to help with SOC 2, HIPAA, and CMMC 2.0 readiness by providing structured logs, playbook artifacts, and continuous monitoring outputs.
How Does Continuous Monitoring Streamline Regulatory Reporting?
Continuous monitoring shortens audit prep by keeping an accessible record of detection, response, and remediation activities and by automatically generating aggregated metrics and control evidence on demand. Dashboards surface executive KPIs while logs capture granular forensic trails, meeting different stakeholder needs without repeated manual pulls. Scheduled report generation enforces a steady cadence and removes the last-minute rush before assessments. Faster incident timelines also help organizations meet regulatory notification requirements and demonstrate effective control operation.
When evaluating XDR automation, the final operational step is choosing a platform and service model that balances automation capability with human oversight and compliance support. If you want to see how hyper-automation, agentic AI, and 24/7 SOC workflows can compress detection-to-containment cycles and deliver audit-ready evidence, contact ShieldWatch for a demo and a discussion about managed XDR options.
Frequently Asked Questions
What types of organizations can benefit from XDR automation?
XDR automation helps organizations that face high alert volumes—especially regulated sectors like healthcare, finance, and government—where compliance and rapid response matter. Mid-market firms with limited security staff also benefit by gaining enterprise-grade detection and response without large hiring investments. In short, teams that need faster, more consistent security operations see the biggest gains.
How does XDR automation integrate with existing security tools?
XDR automation is designed to integrate with SIEM, EDR, threat intel platforms, and other security tooling. It aggregates telemetry across sources to create a unified incident view, enriches context for workflows, and enables cross-domain responses. That lets you leverage existing investments while improving detection and response through automation.
What role does human oversight play in XDR automation?
Human oversight is critical to ensure automated actions align with organizational policy and risk appetite. Automation handles routine triage and remediation, while analysts validate high-risk incidents and make complex decisions. This human-AI partnership preserves governance and adaptability as threats evolve.
Can XDR automation help with incident investigation and forensics?
Yes. XDR automation captures detailed logs and audit trails of automated actions, which are essential for post-incident analysis. Features like retroactive log review let teams reconstruct events, identify patterns, and refine defenses—improving future response and forensic capabilities.
What are the cost implications of implementing XDR automation?
While initial investment is required for technology and onboarding, XDR automation often reduces overall costs by shortening detection and response times and lowering analyst workload—allowing teams to handle more alerts without proportional headcount increases. Over time, reduced incident impact and greater operational efficiency typically justify the expenditure.
How does XDR automation support compliance with industry regulations?
XDR automation supports compliance by automating evidence collection, continuous monitoring, and reporting aligned to frameworks such as SOC 2, HIPAA, and CMMC 2.0. It preserves logs, maintains tamper-evident audit trails, and generates control-specific reports—reducing the manual work needed to prepare for audits and respond to control deviations.
What are the future trends in XDR automation?
Future trends include deeper AI and ML integration for more accurate detection and predictive response, stronger human-AI collaboration models, and improved interoperability across security ecosystems. Expect more predictive analytics, safer agentic automation with refined governance, and tighter integrations that make automation easier to adopt and manage.
Conclusion
XDR automation sharpens security operations by tightening detection-to-response cycles, cutting alert fatigue, and enabling scalable, auditable remediation. With AI and machine learning, teams gain better accuracy and operational capacity, freeing analysts to focus on high-value investigations. When paired with 24/7 SOC support and thoughtful governance, automation both strengthens security posture and helps meet compliance obligations. To see how XDR automation could transform your security operations, reach out for a tailored consultation and demo.




https://shorturl.fm/xiI4u
https://shorturl.fm/QvXBL
https://shorturl.fm/OA0OS
https://shorturl.fm/2zhrG
https://shorturl.fm/PS5zy
https://shorturl.fm/igcwl
https://shorturl.fm/2bMlx
https://shorturl.fm/S3fv3