XDR (Extended Detection and Response) consolidates telemetry from endpoints, network, cloud, and identity systems so teams can detect, investigate, and contain threats across the entire attack surface. This piece breaks down how XDR works, contrasts it with EDR and SIEM, and maps concrete scenarios where XDR cuts dwell time and lowers operational overhead. You’ll find actionable use cases—ransomware containment, insider-threat detection, cloud misconfiguration remediation—plus how AI, hyper-automation, and managed delivery models scale security operations.
Practical examples include detection signals, SOAR playbooks, and measurable outcomes like faster containment and fewer false positives. Short vendor-context sections show how ShieldWatch’s platform supports these capabilities. The sections that follow cover XDR fundamentals, hands-on use cases, cloud and hybrid security, AI-driven automation, managed XDR/SOC delivery, and compliance mappings to help security leaders and SOC teams plan deployments and measure impact.
What Is Extended Detection and Response and How Does It Enhance Security Operations?
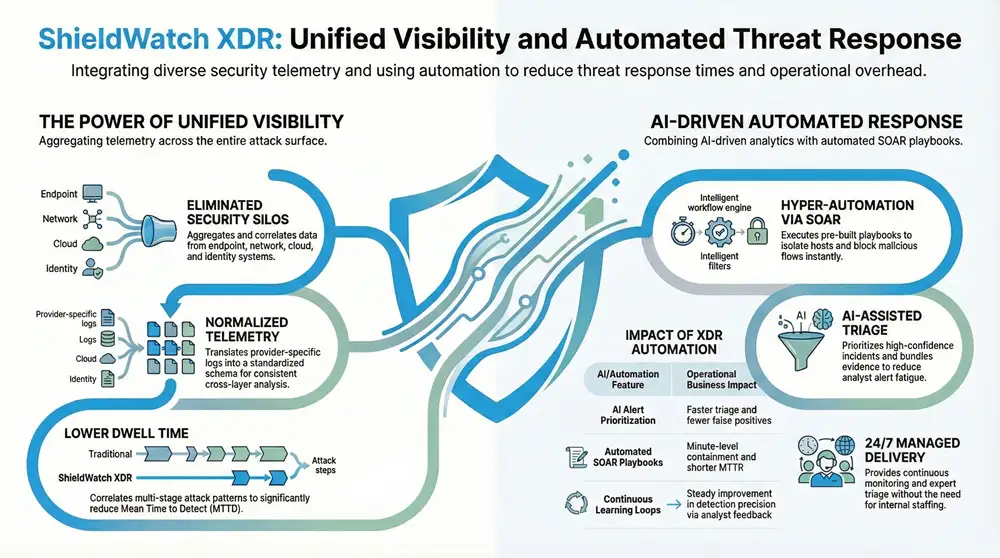
XDR is a platform approach that aggregates and correlates data from EDR, NDR, UEBA, cloud logs, and identity systems to deliver unified detection and coordinated response. By removing siloed telemetry, XDR gives analysts cross-layer visibility into attack patterns and lets teams orchestrate repeatable containment consistently. The core components are normalized telemetry, correlation rules, and SOAR orchestration — together they cut mean time to detect (MTTD) and mean time to respond (MTTR), improve threat hunting, and reduce alert fatigue. Unlike an EDR- or SIEM-first model, XDR emphasizes integrated telemetry and automated execution across the stack; next we’ll look at how enterprise platforms operationalize these capabilities.
XDR delivers three practical operational benefits:
- Unified visibility: Correlates endpoint, network, cloud, and identity signals to surface multi-stage attacks.
- Faster response: Automates containment steps and enables minute-level interventions to shrink dwell time.
- Simplified operations: Reduces analyst load through triage automation and context-rich alerts.
Those advantages frame a closer look at vendor implementation patterns and platform features that make deployments effective in production.
How Does ShieldWatch Define and Implement XDR for Enterprises?
At ShieldWatch, XDR is an enterprise-grade platform that fuses endpoint, network, cloud, and identity telemetry with AI-assisted analytics and orchestration for rapid detection and response. Our deployment approach focuses on fast onboarding and retroactive analysis so historical telemetry becomes usable immediately, enabling early threat discovery. ShieldWatch combines 24/7 SOC expertise with AI-driven workflows and a library of SOAR playbooks to deliver actionable alerts and automated containment across hybrid environments. For teams evaluating fit, we emphasize broad coverage, fast verdicts, and flexible delivery—direct enterprise deployment or channel/MSP delivery—to match operational needs. That implementation overview leads into the concrete operational benefits security teams can expect.
What Are the Key Benefits of Using an XDR Platform in Modern Cybersecurity?
An XDR platform produces measurable results for executives and SOC operators: broader detection coverage, faster response times, and lower operating costs. By correlating diverse telemetry sources, XDR surfaces high-confidence incidents for analyst review and reduces noise through prioritized triage. Automation—pre-built playbooks and decision logic—lets teams isolate hosts, block malicious flows, and rotate credentials to contain threats quickly. Operationally, XDR lowers alert volume, supports compliance through continuous evidence collection, and reduces manual effort. These outcomes explain why organizations are moving from toolchains to integrated XDR for modern security operations.
Which Real-World Use Cases Demonstrate XDR’s Impact on Enterprise Security?
XDR performs best when attacks cross telemetry boundaries and need correlated context for rapid containment. Below are representative enterprise scenarios showing how XDR improves detection, response, and post-incident analysis. Each example outlines the problem, the XDR response pattern, and an outcome metric SOC teams can use to measure success.
- Ransomware outbreak: A phishing click yields a foothold, lateral movement, and file encryption. XDR correlates anomalous endpoint processes with suspicious network flows to block propagation and isolate affected hosts within minutes.
- Insider data exfiltration: Unusual access patterns and large outbound transfers trigger UEBA and identity alerts. XDR correlates those signals, suspends risky sessions, and preserves forensic evidence for investigation.
- Cloud compromise via misconfiguration: Excessive public storage access and abnormal API calls are detected by correlating cloud logs with identity and endpoint telemetry. XDR triggers policy remediation and records an audit trail.
These examples follow a clear problem → solution → outcome pattern and lead into a concise comparison of threats and XDR responses.
The following table summarizes common enterprise threats, the operational challenges they create, and how XDR addresses them.
How ShieldWatch helps: In each scenario ShieldWatch pairs AI-assisted triage with a 24/7 SOC model and hyper-automation to shrink containment windows. Our platform prioritizes rapid verdicts and minute-level containment through automated playbooks, and retroactive analysis surfaces historical indicators from ingested logs—supporting SOC outcomes without replacing internal analyst expertise.
How Does ShieldWatch XDR Secure Cloud and Hybrid Environments?
Securing cloud and hybrid environments requires consistent telemetry ingestion, normalization, and cross-account correlation so teams can detect lateral movement and privilege misuse across providers. XDR addresses multi-cloud complexity by normalizing diverse cloud logs (IAM, storage, API calls) and correlating them with endpoint and network signals to reveal suspicious sequences. That unified view supports continuous compliance checks and misconfiguration detection, and it drives automated remediation workflows. The next subsections describe multi-cloud integration strategies and common misconfigurations XDR can detect and remediate.
What Are the Challenges of Multi-Cloud Security and How Does XDR Address Them?
Multi-cloud deployments bring inconsistent telemetry formats, visibility gaps across accounts, and differing default security postures that complicate correlation and lateral-movement detection. XDR mitigates these issues with telemetry normalization, cross-account correlation rules, and a centralized detection engine that links identity events, API anomalies, and endpoint behaviors. Practical integration patterns include agented and agentless collectors, standardized event schemas, and mapping rules that translate provider-specific logs into common SOC alert types. Solving these integration challenges makes cross-cloud lateral activity and compounded misconfigurations visible to detection pipelines, which then enables automated remediation workflows.
How Does XDR Detect Cloud Misconfigurations and Support Compliance?
XDR detects common misconfigurations—public storage exposure, overly permissive IAM policies, and risky network defaults—by continuously analyzing cloud configuration snapshots and activity logs. When issues are found, XDR can trigger enforcement workflows: notify owners, revert risky changes, or apply guardrails—and it records evidence for auditors. Those detection and remediation steps feed compliance reporting by exporting findings and remediation timelines that map to control requirements. Automating both detection and documentation reduces manual audit work and improves continuous compliance posture.
What Role Does AI and Hyper-Automation Play in Enhancing XDR Capabilities?
Agentic AI and hyper-automation extend SOC capacity by prioritizing alerts, orchestrating validated playbooks, and learning from analyst feedback. AI ingests multi-source telemetry, scores incidents by confidence, and recommends containment steps. Hyper-automation then executes vetted playbooks through SOAR integrations to perform tasks like host isolation or credential rotation. Together these capabilities reduce analyst workload, lower false positives, and speed time-to-containment. The subsections below explain agentic AI mechanics and the common operational benefits of automation in more detail.
How Does Agentic AI Improve Threat Detection and Alert Triaging in XDR?
Agentic AI operationalizes models that consume telemetry—endpoint indicators, network context, identity events—and produce prioritized incident recommendations for analysts. Models learn from human-in-the-loop feedback: analysts confirm or override suggestions, and the system refines scoring to reduce false positives. In practice, agentic AI promotes high-confidence incidents and bundles correlated evidence so analysts spend less time assembling context and more time resolving critical cases. This active learning loop increases precision while keeping human oversight central to trusted incident response workflows.
Before we review specific automation playbooks, here’s how automation features map to quantifiable SOC improvements.
What Are the Benefits of Hyper-Automation and SOAR Workflows in Security Operations?
Hyper-automation with SOAR playbooks removes manual steps and enforces consistent response patterns so smaller teams can handle more alerts without sacrificing quality. Typical automated actions include isolating compromised hosts, blocking malicious IPs at the network edge, disabling affected accounts, and orchestrating credential rotations. A library of pre-built workflows accelerates operationalization—teams adapt templates to their environment and integrate with ticketing and ChatOps for collaborative response. Automating repeatable tasks speeds resolution and preserves a replayable audit trail for post-incident review and compliance.
How Do Managed XDR and SOC as a Service Enhance Enterprise Security Operations?
Managed XDR and SOC-as-a-Service deliver continuous monitoring and operational expertise that augment internal teams, offering 24/7 detection, triage, and response without the need to staff a full SOC. These service models clarify shared responsibilities: the provider handles monitoring, initial triage, and automated containment while the enterprise controls escalation, policy decisions, and forensic ownership. The following subsections describe how managed XDR complements in-house teams and how 24/7 coverage shortens detection windows.
What Is Managed XDR and How Does It Complement In-House Security Teams?
Managed XDR is a delivery model where a provider runs the XDR platform and SOC processes to detect and respond on customers’ behalf while coordinating closely with internal security owners. It boosts limited SOC capacity by supplying experienced analysts, threat intelligence, and pre-built playbooks that speed onboarding and surface early wins—fewer false positives and discovery of latent threats. Onboarding usually includes rapid telemetry ingestion, initial retroactive hunts, and an agreed escalation matrix for significant incidents. For teams that want predictable costs and continuous coverage, managed XDR becomes a practical extension of in-house capabilities.
How ShieldWatch helps: ShieldWatch offers managed XDR with channel-friendly delivery that pairs our XDR platform with 24/7 SOC expertise and hyper-automation workflows, enabling MSPs and mid-market customers to access advanced detection without building a full SOC. This model supports fast deployment and immediate operational gains.
How Does 24/7 SOC as a Service Provide Continuous Threat Monitoring and Response?
A 24/7 SOC-as-a-Service maintains constant monitoring cadence, staffed escalation paths, and documented incident lifecycle management to shorten detection and response windows. Continuous coverage means alerts are evaluated in real time, containment actions can run anytime, and escalations to internal teams follow SOPs that preserve chain-of-custody and compliance posture. Example outcomes include reduced average time-to-detect and documented containment actions for auditors—improving security posture and regulatory readiness. Continuous SOC coverage also enables proactive hunts that uncover dormant threats before they escalate.
How Does ShieldWatch XDR Support Compliance and Risk Management in Enterprises?
ShieldWatch maps XDR telemetry and automated workflows to common regulatory frameworks so enterprises can maintain audit-ready evidence, monitor control effectiveness, and close compliance gaps. By collecting endpoint, network, cloud, and identity evidence and automating report exports, an XDR platform substantiates controls for frameworks like SOC 2, HIPAA, CMMC 2.0, and ISO 27001. The subsection below lists frameworks and maps ShieldWatch capabilities to control requirements with a concise table that shows how features align with audit needs.
Which Regulatory Frameworks Does ShieldWatch XDR Help Enterprises Comply With?
ShieldWatch supports readiness for widely used frameworks—SOC 2, HIPAA, CMMC 2.0, and ISO 27001—by providing continuous telemetry, alerting on control deviations, and automating evidence collection. Audit controls requiring access logging, configuration management, and incident response documentation are supported through recorded alerts, change detection, and exportable incident reports. ShieldWatch’s capabilities—broad telemetry coverage, automated reporting, and retention policies—reduce manual audit preparation and provide traceable evidence during assessments. These features feed audit workflows that teams use to demonstrate control effectiveness.
How Does XDR Facilitate Audit Readiness and Reporting for SOC 2, HIPAA, CMMC, and ISO 27001?
XDR simplifies audit readiness by automating evidence collection, generating customizable reports, and preserving incident artifacts auditors require. Practical steps include mapping controls, enabling continuous telemetry collection, scheduling report exports for audit windows, and retaining immutable logs for forensic validation. Pre-built templates and report filters reduce manual effort and help SOC teams produce the documentation auditors expect. Implementing these workflows streamlines audits and supports ongoing risk management by highlighting control gaps and tracking remediation progress.
For organizations focused on compliance, ShieldWatch emphasizes automated reporting and evidence retention that align with common frameworks, letting teams concentrate on remediation and risk reduction instead of manual report assembly.
Frequently Asked Questions
What types of organizations can benefit from implementing an XDR platform?
XDR benefits organizations of all sizes and industries. Enterprises with complex IT environments—especially hybrid and multi-cloud infrastructures—gain the most from unified telemetry. Teams facing rising threats like ransomware or insider risk will see immediate value, and small-to-medium businesses can access enterprise-grade detection and response without a large in-house SOC.
How does XDR improve incident response times compared to traditional methods?
XDR improves response times by consolidating telemetry and automating repeatable actions. Traditional, siloed toolchains slow detection and correlation; XDR integrates endpoint, network, and cloud data so teams can quickly identify and link threats. Pre-built SOAR playbooks enable immediate containment actions, reducing mean time to respond (MTTR) and limiting damage.
What role does threat intelligence play in enhancing XDR capabilities?
Threat intelligence enriches XDR by providing context on emerging threats and attacker TTPs. Integrated feeds improve detection accuracy and prioritization, and they inform automated playbooks so responses reflect current adversary behavior. In short, threat intel raises detection fidelity and speeds effective response.
Can XDR solutions be integrated with existing security tools?
Yes. XDR is designed to integrate with existing security stacks—firewalls, EDR, SIEM, identity systems, and more. That interoperability preserves prior investments while enabling normalized telemetry and a unified view that improves incident detection and response effectiveness.
What are the cost implications of adopting an XDR platform?
Costs vary by organization size, environment complexity, and required features. While initial investment can be significant, XDR often delivers long-term savings by reducing tool sprawl, lowering operational overhead, and shortening incident handling times. Flexible pricing and managed delivery options help organizations align cost to value.
How does XDR support compliance with regulatory frameworks?
XDR supports compliance by automating evidence collection, monitoring control effectiveness, and producing detailed reports. Continuous telemetry and exportable incident artifacts help demonstrate adherence to frameworks like SOC 2, HIPAA, and ISO 27001—streamlining audits and strengthening risk management.
Conclusion
ShieldWatch XDR strengthens security operations by delivering unified visibility, faster containment, and simpler day-to-day workflows. With AI-driven automation, comprehensive telemetry, and flexible delivery models, organizations can reduce risk and streamline compliance. If you want to see how these benefits apply to your environment, explore ShieldWatch XDR solutions tailored to enterprise needs and take the next step toward a stronger security posture.




Become our affiliate—tap into unlimited earning potential!
Drive sales, earn big—enroll in our affiliate program!
Unlock exclusive affiliate perks—register now!
Become our partner and turn referrals into revenue—join now!
Refer friends, earn cash—sign up now!
Promote our products—get paid for every sale you generate!