SentinelOne + XDR: Practical Guide to Strengthening Endpoint Security and Implementation
Enterprises today struggle with fragmented endpoint telemetry, increasingly sophisticated attackers, and overwhelmed security teams—conditions that weaken detection and response. Integrating SentinelOne telemetry into an Extended Detection and Response (XDR) layer addresses these gaps by unifying signals, speeding containment, and producing audit-ready evidence. In this guide we describe how SentinelOne XDR integration raises detection fidelity, the architectural patterns for ingesting and correlating endpoint events across cloud and network, the role of managed SOC services alongside automated workflows, and the compliance controls that benefit most from continuous monitoring.
You’ll find clear data-flow diagrams, deployment considerations, and practical best practices for enterprise rollouts, plus real-world use cases that show coordinated automated and human response to advanced threats. The goal: leave you with specific steps to plan integrations, measure ROI, and reduce analyst fatigue through targeted automation and repeatable playbooks.
What Are the Key Benefits of SentinelOne XDR Integration with ShieldWatch?
Connecting SentinelOne to an XDR platform gives you unified visibility by bringing detailed endpoint telemetry into a correlated detection fabric that spans cloud, network, and identity. SentinelOne provides granular process, file, and network events; the XDR correlation engine normalizes and scores event sequences against rules and behavioral analytics. The outcome is higher-fidelity alerts, richer forensics, and faster containment. Practically, teams see faster verdicting, fewer false positives, better investigator context, and simpler audit evidence collection—so analysts can focus on high-risk incidents while routine responses are automated. Below we highlight AI-driven automation and noise reduction, then show a compact mapping of telemetry attributes to detection outcomes and operational gains.
The main benefits of integration include:
- Unified Visibility: Endpoint, cloud, and network signals form a single incident timeline that speeds investigations.
- Faster Containment: Automated detection and response actions reduce time to isolate threats and limit lateral movement.
- Fewer False Positives: Machine-learning correlation and contextual enrichment cut noisy alerts and free up analyst time.
- Stronger Forensics: Detailed execution chains and artifacts support root-cause analysis and remediation.
- Simplified Compliance: Continuous monitoring and retained telemetry make audit reporting more efficient.
These capabilities create the foundation for deeper automation and analyst augmentation, which we expand on next.
Compare telemetry and correlation improvements to see where integration delivers the biggest value.
This table shows how endpoint telemetry supplies concrete attributes an XDR engine uses to raise detection accuracy and speed response. Next, we explain how agentic AI and automation turn those attributes into tactical actions.
How Does AI-Driven Automation Enhance Threat Detection and Response?
AI-driven automation converts correlated telemetry into prioritized hypotheses, automated playbook actions, and clear analyst next steps—cutting manual triage and shortening investigations. Models ingest multi-source signals—process lineage, network connections, identity anomalies—to score incidents and trigger agentic playbooks that can isolate hosts, collect artifacts, and enrich alerts automatically. For example: a high-confidence behavioral match from SentinelOne escalates to an XDR playbook that isolates the endpoint, captures forensic data, and notifies an analyst for validation. That loop reduces verdict-to-action time and lowers false positives by applying contextual scoring before alerts reach analysts. Below we show how consolidation and prioritization cut analyst workload and boost SOC throughput.
In What Ways Does Integration Reduce Alert Fatigue and Improve Efficiency?
Integration reduces alert fatigue by consolidating duplicate signals, using ML correlation to group related events, and enriching alerts with contextual evidence so analysts see one actionable incident instead of many low-value alerts. Prioritization engines rank incidents by risk using features like process ancestry, lateral-movement indicators, and threat-intel matches, directing attention to the highest-impact investigations. Operationally this delivers measurable savings: fewer analyst hours on false positives and faster containment thanks to richer decision data in alerts. For teams that need continuous coverage, the next section outlines how 24/7 SOC models augment automated XDR workflows and enable uninterrupted threat hunting.
How Does ShieldWatch XDR Architecture Support Seamless SentinelOne Integration?
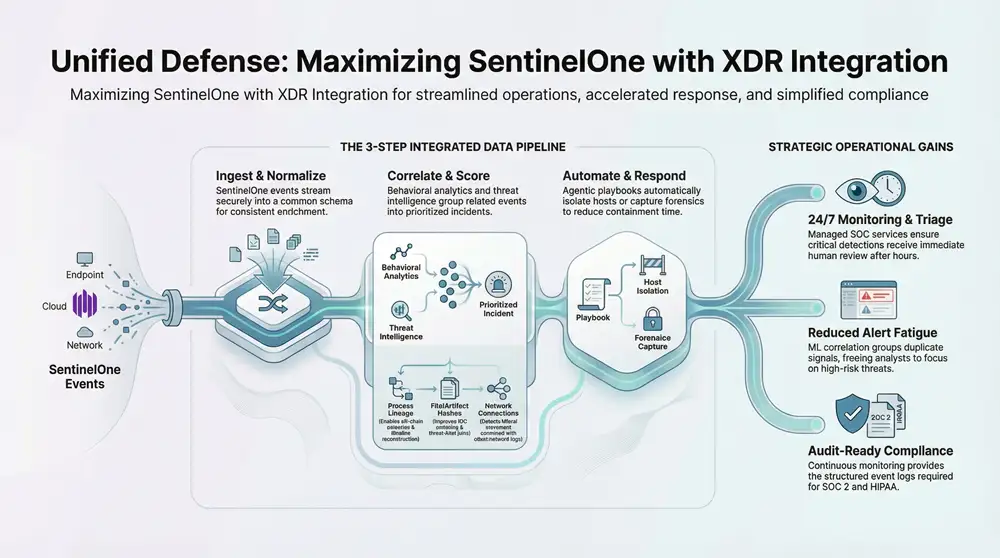
A resilient XDR architecture ingests SentinelOne telemetry via API connectors or streaming collectors, normalizes events into a common schema, correlates sequences with behavioral rules, and triggers playbooks for automated response. This layered approach minimizes integration friction while preserving data fidelity. The ingestion layer maps SentinelOne process, file, network, and rollback actions into normalized event types; the correlation engine applies scoring and enrichment from threat intelligence and network telemetry to produce prioritized incidents. Historical indices and retention enable retroactive detection and forensic reconstruction. Below are the core data-flow steps, followed by a mapping of integration touchpoints.
High-level data flow from endpoint to automated response:
- Ingest: SentinelOne events stream securely to the XDR ingestion layer.
- Normalize: Events are converted into a shared schema for consistent correlation and enrichment.
- Correlate & Score: Behavior analytics and threat intelligence surface prioritized incidents.
- Automate/Assign: Playbooks run containment or remediation and route validated alerts to analysts.
These steps describe the core pipeline teams implement when connecting SentinelOne telemetry to an XDR fabric and prepare you for the specific mapping below.
This mapping clarifies how each SentinelOne signal feeds downstream detection and response, helping teams prioritize integration touchpoints during rollout. Next, we examine managed SOC services that complement these architectural capabilities.
What Role Does SentinelOne Telemetry Play in Enhancing Detection and Context?
SentinelOne delivers high-resolution endpoint signals—process trees, file interactions, registry and persistence artifacts, and rollback actions—that give an XDR engine the context it needs to distinguish benign anomalies from malicious behavior. Process ancestry helps reconstruct lateral movement and multi-stage campaigns; file and hash data boost IOC confidence by tying activity to threat intel. Rollback and containment actions serve as remediation evidence the XDR can verify and annotate in incident timelines. Together, these telemetry types increase detection fidelity and speed root-cause analysis, supporting both automated playbooks and analyst-driven investigations.
How Are Data Flows and Correlation Managed Across Endpoints, Cloud, and Network?
Data flows follow an ingest→normalize→correlate→enrich pipeline so endpoint, cloud API, and network telemetry are scored uniformly and assembled into unified incident timelines. Normalization maps diverse schemas to canonical fields—actor, action, resource, timestamp—so correlation rules work across sources without brittle mappings. Correlation logic applies behavioral heuristics and scored rules to group related events, produce composite incidents, and compute risk scores that govern automation thresholds. Retention and indexed historical hunting enable retroactive searches that reveal lateral movement patterns long after initial compromise, supporting incident response and compliance evidence needs.
What Managed SOC Services Complement SentinelOne XDR Environments?
Managed SOC services extend an integrated SentinelOne+XDR deployment with continuous monitoring, expert triage, and playbook execution—accelerating response and filling coverage gaps for organizations with limited internal staff. Core SOC capabilities include 24/7 alert monitoring, incident validation, escalation coordination, and post-incident reporting; these services ensure high-confidence incidents get timely human review and appropriate action. Managed teams also run proactive threat hunts and tune detections to reduce false positives over time, improving the signal delivered to in-house teams. The following list summarizes the most valuable service layers.
- 24/7 Monitoring and Triage: Continuous oversight to validate alerts and speed containment.
- Proactive Threat Hunting: Analyst-led hunts guided by AI hypotheses and historical telemetry.
- Playbook Execution and Orchestration: Coordinated automated and manual remediation with business stakeholders.
- Reporting and Compliance Support: Tailored incident reports and audit artifacts for regulators.
These layers let automation run efficiently while ensuring human judgment covers complex incidents and business-impact decisions. Next we detail the analyst–AI collaboration model.
How Do Human Analysts and AI Collaborate for Proactive Threat Hunting?
Analysts and AI work together by using machine-generated hypotheses and prioritized leads as starting points for investigator-led hunts. Analysts add intuition to refine search pivots, uncover novel indicators, and validate model outputs. AI surfaces correlated anomalies and likely attack paths; analysts confirm context, follow investigative threads, and update playbooks with new findings. That feedback loop improves model precision and detection tuning, reducing false positives and producing more actionable hunts. Typical hunts begin with prioritized XDR alerts, run hypothesis-driven queries over a 90-day index, and end with enrichment, containment, and playbook updates the AI can reuse.
What Are the Operational Advantages of 24/7 SOC Monitoring?
Round-the-clock SOC monitoring shortens dwell time by ensuring critical detections receive immediate attention even outside business hours, preventing attackers from exploiting overnight windows to escalate privileges or exfiltrate data. Continuous coverage supports time-sensitive actions like isolating compromised endpoints, capturing forensics, and coordinating with IT to block network threats. For mid-market organizations and MSPs, outsourcing 24/7 operations reduces hiring burdens and grants access to senior analyst expertise without building an internal night shift. These advantages translate into measurable improvements in MTTD and MTTR and better audit readiness through prompt incident documentation.
How Does SentinelOne XDR Integration Support Compliance and Regulatory Requirements?
Combining SentinelOne with an XDR platform helps meet compliance requirements by delivering continuous monitoring, consolidated log retention, and structured audit artifacts that map to control objectives in frameworks like SOC 2, HIPAA, and CMMC 2.0. The approach is evidence-driven: normalized telemetry and incident timelines provide the records auditors need to verify monitoring controls, access/change logs, and response procedures. Automated reports and dashboards make it easier for assessors to review control evidence tied to detection, response, and remediation activities. Below we list supported standards and explain how continuous monitoring produces auditor-friendly artifacts.
Supported compliance standards and how integrated XDR helps:
- SOC 2: Continuous logging, incident detection, and documented monitoring actions map to trust service criteria.
- HIPAA: Access monitoring, breach detection, and retained event data support patient-data protection requirements.
- CMMC 2.0: Continuous telemetry and documented response procedures help demonstrate cybersecurity maturity.
- ISO 27001: Incident management and continual improvement processes are supported through integrated detection and reporting.
These mappings cut down manual work for auditors and create a consistent, searchable source of truth for security control evidence. The next subsection explains how continuous monitoring supports audit readiness.
Which Compliance Standards Are Supported by ShieldWatch XDR?
ShieldWatch XDR supports multiple compliance frameworks by offering continuous monitoring, configurable retention policies, and reporting features that align with auditor expectations for controls and evidence collection. The platform provides searchable event histories, incident timelines, and exportable reports aligned to monitoring and incident-response control categories in SOC 2, HIPAA, CMMC 2.0, and ISO 27001. ShieldWatch’s architecture also emphasizes cloud coverage and historical hunting windows that speed forensic analysis and audit readiness. These capabilities reduce the time teams spend gathering evidence and enable faster responses to auditor requests.
How Does Continuous Monitoring Facilitate SOC 2, HIPAA, and CMMC 2.0 Readiness?
Continuous monitoring generates the audit artifacts assessors expect: complete logs, incident timelines with remediation steps, and records of timely response and change controls. Indexed retention lets assessors validate monitoring windows and sample incidents over required timeframes, while automated reports map incidents to control objectives for faster review. Dashboards and role-based report access demonstrate separation of duties and governance, shortening audit cycles and reducing manual evidence collection work for compliance teams.
What Are the Strategic Considerations for Enterprises Implementing SentinelOne XDR?
When implementing SentinelOne XDR, organizations should weigh deployment models, integration planning, data retention and privacy constraints, and change-management priorities to ensure measurable security and business outcomes. Key choices include co-managed versus fully managed operation, telemetry retention windows for historical hunting, and how playbooks map to organizational escalation paths. Operational trade-offs—investing in analyst training versus outsourcing—should be evaluated with ROI metrics such as analyst-hours saved, MTTD/MTTR improvement, and avoided breach costs. The next sections quantify ROI impacts and provide a practical deployment checklist.
Strategic trade-offs to consider:
- Co-managed vs Fully Managed: Choose based on internal expertise and desired control over incident handling.
- Data Retention Policies: Balance storage costs against the value of historical hunting windows for retroactive detection.
- Automation Scope: Define which playbooks can run unattended and which require human approval to avoid business disruption.
These decisions feed the ROI model and the implementation checklist below.
Use this table to quantify trade-offs and prioritize integration steps that deliver the largest business impact. Next we cover how those metrics translate into ROI and risk reduction.
How Does Integration Deliver Measurable ROI and Risk Reduction?
Integration delivers measurable ROI through fewer analyst hours spent on false positives, quicker containment that limits breach impact, and lower compliance preparation costs. You can express these gains as saved analyst hours per month, percentage reductions in false positives, and shorter MTTR. For example, automating low-risk responses and cutting false positives translates directly into hourly savings and improved SLA performance. Cost avoidance from prevented breaches—when compared to average remediation costs—adds further justification. Reusable playbooks and historical hunting capabilities compound savings as detection maturity improves.
What Best Practices Ensure Successful SentinelOne XDR Deployment?
Start with a scoped pilot to validate ingestion, mappings, and playbook behavior, then roll out iteratively while tuning detections. Define telemetry schemas, retention policies, and escalation paths before broad deployment and involve stakeholders from IT, security, and legal to align automation thresholds with business risk. Run tabletop exercises to validate playbooks and confirm logging and incident reporting meet auditor expectations. Track KPIs—MTTD, MTTR, false-positive rate, and analyst hours saved—and use those metrics to drive continuous improvement and ensure the integration meets its security and operational goals.
What Real-World Use Cases Demonstrate the Effectiveness of SentinelOne XDR Integration?
Integrated SentinelOne XDR use cases show coordinated detection and response across the kill chain: early behavioral detections on endpoints trigger cross-source correlation, automated containment isolates affected hosts, and analysts run hunts to remove persistent footholds. Common examples include ransomware where process anomalies precede encryption and lateral movement indicators link hosts and cloud workloads for coordinated isolation and rollback. Another frequent scenario is credential theft, where identity anomalies combined with endpoint execution chains reveal compromised accounts and enable rapid revocation and containment. The following subsections outline an APT interdiction and explain how hybrid cloud environments gain from integrated telemetry and policy enforcement.
Typical business use cases include:
- APT Detection and Interdiction: Early discovery of multi-stage campaigns through execution-chain correlation.
- Ransomware Response: Automated isolation and rollback to limit encryption spread and speed recovery.
- Hybrid Cloud Protection: Cross-tenant workload visibility and identity correlation to prevent lateral escalation.
These scenarios demonstrate how integrated telemetry changes incident outcomes—now we dive into a concrete example.
How Does Integrated XDR Prevent Advanced Persistent Threats?
Integrated XDR thwarts APTs by linking small anomalous activities—suspicious process launches, unusual parent-child execution chains, or outbound C2 attempts—into a coherent incident that reveals a multi-stage attack. SentinelOne’s process lineage feeds the XDR correlation engine, which recognizes patterns like privilege escalation followed by lateral credential use. Automated playbooks isolate compromised hosts and capture artifacts for forensic analysis. Analysts use aggregated timelines and historical hunting to find persistence mechanisms and remove backdoors, shortening the campaign lifecycle and preventing prolonged data exfiltration. That chain—detection, automated mitigation, and focused hunting—turns early signals into decisive defensive actions.
In What Ways Does ShieldWatch XDR Secure Hybrid Cloud Environments?
ShieldWatch XDR extends endpoint context into cloud workloads by correlating SentinelOne telemetry with cloud-native logs and identity signals to detect threats that cross on-prem and cloud boundaries. By mapping process activity and workload identity into the XDR fabric, the platform exposes suspicious cross-tenant behavior and enforces automated containment across hybrid stacks. ShieldWatch supports extended historical hunting across cloud workloads, and its managed SOC services provide around-the-clock orchestration for rapid remediation. Together, these capabilities detect lateral movement into cloud workloads and apply policy-driven containment across the full estate.
This guide covered the benefits, architecture, managed services, compliance mapping, strategic trade-offs, and real-world use cases for integrating SentinelOne with an XDR platform to strengthen endpoint security. Each section provides practical guidance and actionable next steps for planning a phased integration that prioritizes high-fidelity detection, automated response, and measurable operational improvements.
Frequently Asked Questions
Which organizations benefit most from integrating SentinelOne with XDR?
Organizations that handle sensitive data—healthcare, finance, government—gain the most from SentinelOne + XDR. These sectors face strict compliance requirements and are frequent attack targets. Unified visibility and automated response help them improve security posture, reduce response times, and meet regulations like HIPAA and SOC 2. Smaller teams or businesses with limited security staff also benefit from managed SOC services that extend coverage and expertise.
How does the integration affect incident response times?
Integrating SentinelOne with XDR shortens incident response times by automating detection and response steps. Playbooks can isolate threats and kick off containment actions automatically, reducing human intervention for routine events. That frees security teams to concentrate on complex threats and yields faster MTTD and MTTR—key measures of an effective security program.
What should organizations consider about data retention when implementing SentinelOne XDR?
Retention planning is essential. Keeping telemetry long enough supports historical threat hunting and meets regulatory needs, but storage costs must be balanced against forensic value. Define retention windows for different data types aligned with operational and compliance requirements, and include lifecycle policies for archiving and deletion.
How does SentinelOne XDR enable proactive threat hunting?
SentinelOne XDR supplies rich telemetry and AI-driven insights that let analysts prioritize and pursue high-value leads. Machine-generated hypotheses narrow investigative scope; analysts validate context, pivot to new indicators, and update playbooks. This human–AI collaboration speeds discovery of novel indicators and prevents escalation into major incidents.
What role does continuous monitoring play in compliance readiness?
Continuous monitoring provides the evidence auditors need: complete logs, incident timelines, and remediation records. With SentinelOne + XDR, organizations can produce automated reports and dashboards that map incidents to control objectives, making audits faster and less labor-intensive.
How can organizations quantify the ROI of integrating SentinelOne with XDR?
Measure ROI using KPIs such as reduction in analyst hours on false positives, improvements in MTTD and MTTR, and cost avoidance from prevented breaches. Also consider efficiency gains from automated playbooks and lower compliance preparation costs. Quantifying these metrics builds a strong business case for integration.
What common challenges occur during integration and how can they be mitigated?
Typical challenges include data silos, schema mismatches, and stakeholder coordination. Mitigate them with careful planning, canonical schemas, phased rollouts, and cross-functional involvement from IT, security, and legal. Pilots and iterative tuning keep disruption low and detection accuracy high.
Conclusion
Integrating SentinelOne with an XDR platform materially strengthens endpoint security by delivering unified visibility, faster containment, and fewer false positives. This integrated approach simplifies compliance and lets security teams focus on the highest-risk incidents. If you’re ready to see these benefits in your environment, ShieldWatch can help you plan and implement a phased, measurable integration that delivers rapid security and operational improvements.




Unlock top-tier commissions—become our affiliate partner now!
Get paid for every referral—sign up for our affiliate program now!
Be rewarded for every click—join our affiliate program today!
Join forces with us and profit from every click!
Apply now and receive dedicated support for affiliates!
Earn passive income on autopilot—become our affiliate!
Share your link and rake in rewards—join our affiliate team!