Hardening APIs for XDR: Practical Best Practices and How ShieldWatch Helps
APIs power telemetry, identity signals, and sensitive data flows across endpoints, cloud services, and networks — and that makes them a primary attack surface inside XDR pipelines. When APIs aren’t discovered, validated, and monitored correctly, attackers gain avenues to exfiltrate data or pivot inside environments, increasing dwell time and incident complexity.
This article lays out the real operational challenges of securing APIs in XDR, practical integration and runtime protections, and the operational patterns that reduce risk without disrupting service. We also show how an enterprise XDR like ShieldWatch XDR augments these controls with automated discovery, AI anomaly detection, SOAR playbooks, and managed SOC coverage. You’ll find threat mappings, a prioritized integration checklist, capability-to-control tables, and concrete monitoring and automation patterns to harden APIs inside XDR.
What Are the Core Challenges in Securing APIs within XDR Integrations?
APIs touch multiple layers — application logic, identity, telemetry, and networking — which makes consistent visibility and enforcement difficult. Public endpoints, third-party integrations, and dynamic microservices expand the attack surface while forcing XDR to normalize diverse telemetry formats and contextual signals to reach reliable detections. Closing these gaps reduces false positives, accelerates triage, and enables confident automated containment. Recognizing where coverage is thin is the first step to designing XDR rules, telemetry schemas, and playbooks that expose real API risk without overwhelming analysts.
APIs also add operational friction that directly affects detection and response quality. The next section lists the API threats security teams encounter most often.
Which API Threats Impact XDR Platforms Most Frequently?
APIs are commonly attacked in ways that mirror the OWASP API Security Top 10. Frequent vectors include broken authentication and authorization, injection or parameter tampering, excessive data exposure, abuse of rate-limited endpoints, and API-focused DDoS or volumetric masking of data theft. Indicators show up across sources: anomalous tokens in auth logs, spikes in network traffic, malformed payloads in app logs, and unusual endpoint behavior like unexpected process activity. XDR delivers value where those cross-domain signals are normalized and correlated to produce high-fidelity detections.
Noisy, fragmented API telemetry also creates risks tied to version drift and integration complexity — the next section explains why.
How Do API Versioning and Integration Complexities Affect Security?
Versioning gaps, undocumented routes, and schema drift create blind spots: deprecated endpoints or forgotten routes can remain reachable and attract low-investigation attacker activity. Schema changes that aren’t enforced let malformed data bypass defenses, and third-party integrations often use inconsistent auth models that break centralized detection. Operational controls — continuous API discovery, schema validation tests, and runtime contract enforcement — make the live surface explicit to XDR. Systematic discovery and governance close the gap between what’s running and what XDR consumes, improving detection fidelity and reducing uncertainty during investigations.
Continuous discovery finds forgotten endpoints that need runtime protection and telemetry correlation, which leads into how a modern XDR enhances these capabilities.
How Does ShieldWatch XDR Enhance API Security and Threat Detection?
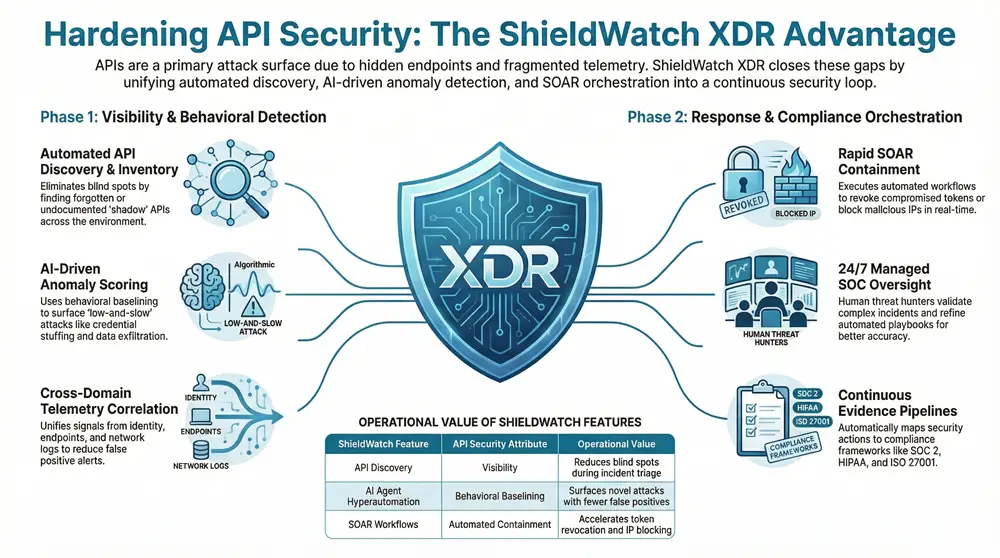
ShieldWatch XDR strengthens API defenses by combining automated discovery, cross-domain telemetry correlation, AI-driven anomaly scoring, and SOAR orchestration to detect and contain API threats across endpoints, network, cloud, and identity. The platform converts fragmentary signals into context-rich incidents using features like API inventorying, runtime baselining, and automated containment playbooks for confirmed threats. These capabilities help reduce alert fatigue, speed response, and provide an operational hub for API-specific telemetry and controls.
Below is an EAV-style comparison that ties ShieldWatch XDR features to API security attributes and the operational value they deliver.
The table summarizes how core ShieldWatch XDR capabilities map to API security attributes and the operational value they deliver.
Pairing discovery with automated response shortens mean time to containment and improves analyst efficiency, moving API defenses toward operational maturity.
What Are ShieldWatch XDR’s Key Features for API Discovery and Runtime Protection?
ShieldWatch XDR builds a living API inventory with passive telemetry and optional active discovery, then correlates those findings with identity and endpoint signals to prioritize risk. Runtime protections include traffic baselining, anomaly scoring, and orchestration hooks that enable dynamic rate limits or automatic isolation when behavior deviates. Recommended telemetry sources are structured API logs, application error logs, network flow records, and identity/authentication logs; correlating these lets XDR triangulate suspicious activity into actionable incidents. Configure normalized logging, consistent timestamps, and sufficient retention so investigations keep necessary context.
These discovery and runtime protections feed AI-driven analytics that improve detection and response outcomes, discussed next.
How Does AI-Driven Anomaly Detection Improve API Threat Response?
AI-driven anomaly detection in ShieldWatch XDR establishes baselines across identity, endpoint, and network signals, surfacing deviations like privilege misuse, credential stuffing, and abnormal data access. Correlating identity with API call patterns and endpoint behavior reduces false positives and speeds analyst triage with prioritized alerts. When the system raises a high-confidence anomaly, SOAR playbooks can revoke compromised tokens, apply temporary rate limits, or isolate affected services while preserving audit trails for post-incident review. These workflows lower MTTR and route complex decisions to 24/7 analysts when human judgment is needed.
Tightly coupling AI with orchestration produces repeatable containment playbooks that reduce manual errors and support continuous compliance evidence collection.
What Are the Best Practices for Secure API Integration in XDR Platforms?
Secure API integration starts with design-time controls — least privilege, input validation, and explicit schema contracts — and extends into runtime observability and automated response. Effective programs combine secure-by-design APIs, strong auth and authorization, structured telemetry forwarding, and layered runtime protections (WAF/gateway policies and rate limiting). These measures reduce the surface XDR must monitor, simplify correlation rules, and make automation safer and more targeted. The checklist below prioritizes immediate actions teams can take to improve API posture and XDR effectiveness.
Use this checklist to align engineering and security teams on concrete steps for API hardening within XDR environments.
- Design for least privilege: Enforce RBAC and scoped permissions so APIs only expose necessary operations.
- Enforce schema validation: Reject malformed payloads at the edge before they reach services.
- Forward structured telemetry: Stream parsed API logs, traces, and auth events to XDR in near real time.
This checklist tightens signal-to-noise for XDR and improves the speed and accuracy of automated playbooks, helping teams focus on true incidents instead of chasing alerts.
Below is an EAV-style table that maps common control areas to recommended implementations for XDR ingestion and enforcement.
Operationalizing these steps ensures XDR receives high-quality inputs, improving detection rules and enabling safer automation. The next paragraphs cover auth models and continuous monitoring practices teams should adopt.
Which Authentication and Authorization Methods Strengthen API Security?
Strong API auth uses modern identity protocols — OAuth 2.0 with scoped tokens, carefully validated JWTs, and mTLS for service-to-service where appropriate — combined with strict token lifecycle policies. Trade-offs exist: API keys are simple but risky, JWTs are efficient but need revocation strategies, and mTLS is strong but operationally heavier. Feeding identity telemetry into XDR surfaces token anomalies (reuse, abnormal lifetimes, suspicious claim changes), which are critical detection signals. Best practice couples robust auth models with centralized identity logging and sends token events into XDR for correlation with endpoint and network behavior.
These identity controls make automated responses (like token revocation) safer because actions are grounded in reliable identity signals, enabling better continuous monitoring and response orchestration.
How Can Continuous Monitoring and Automated Response Reduce API Risks?
Continuous monitoring means forwarding structured API logs, traces, and auth events into XDR to build baselines for anomaly scoring and early warnings. SOAR playbooks translate validated alerts into deterministic actions — dynamic rate limiting, token revocation, temporary isolation, and enriched tickets with investigation context. Safe automation includes gating: escalation thresholds, analyst approval for high-impact actions, and simulation modes for tuning. Track KPIs such as MTTR, detection coverage, false-positive rate, and automation frequency to validate and refine playbooks.
A disciplined monitoring-and-automation loop lowers dwell time, preserves availability, and delivers repeatable evidence for compliance and forensics.
How Do Managed SOC Services Support API Security in ShieldWatch XDR?
Managed SOC services extend XDR with 24/7 monitoring, API-focused threat hunting, and analyst-led escalations when automation reaches its limits. A managed SOC brings mature triage and validation processes, helping organizations without deep in-house resources maintain continuous coverage and reduce dwell time. The partnership amplifies XDR detections with contextual investigation, threat intelligence enrichment, and calibrated playbook responses. Managed SOC teams also coordinate remediation handoffs to engineering and tune detection to the customer’s normal API behavior.
Below is a bulleted list summarizing how a managed SOC augments API security for XDR customers.
- Continuous triage: Analysts validate suspicious API activity and reduce false positives before escalation.
- Threat hunting: Proactive hunts search for stealthy API abuse patterns that automated rules may miss.
- Playbook orchestration: Analysts refine and run SOAR playbooks for containment and forensic collection.
This human+automation model ensures responses are context-aware and speeds recovery when incidents occur.
What Role Does 24/7 SOC Monitoring Play in Detecting API Threats?
Continuous SOC monitoring catches subtle API anomalies that only reveal patterns across multiple sources and time windows — credential misuse across regions or slow exfiltration via pagination, for example. Human analysts distinguish business-justified spikes from suspicious lateral activity and escalate incidents with enriched evidence for fast remediation. SOC teams also operate watchlists and inject threat intelligence to flag malicious IPs or known exploitation indicators. Ongoing monitoring shortens feedback loops and improves detection models.
Analyst validation and vendor-managed orchestration feed safe automation that can terminate risky sessions or isolate services when needed.
How Does Incident Response Automation Enhance API Protection?
Automation converts validated detections into repeatable containment steps — token revocation, temporary ACL adjustments, dynamic rate limits, and IP blocking — reducing manual toil and limiting attacker dwell time. Automation must include safety checks: confidence scoring, escalation rules, and human approval for high-impact actions to avoid service disruptions. Example playbooks orchestrate investigation enrichment, containment, and recovery while preserving audit trails for post-incident review and compliance. Properly tuned automation, combined with SOC oversight, scales protection without adding operational burden.
Faster automated response narrows the gap between detection and containment and improves audit readiness and compliance mapping.
What Compliance and Regulatory Considerations Are Essential for XDR API Security?
API controls map directly to common compliance frameworks through access controls, logging and monitoring, data protections, and incident response procedures. XDR helps collect and preserve the telemetry auditors expect — structured logs, correlated identity events, and records of automated containment — turning continuous compliance into a practical, auditable process. Relevant frameworks include SOC 2, HIPAA, ISO/IEC 27001, and CMMC 2.0. Mapping technical controls to these frameworks helps prioritize work that satisfies both security and compliance objectives.
The table below maps common frameworks to API controls and shows example XDR mappings for evidence collection and automation.
These mappings show how XDR becomes a continuous evidence pipeline for auditors and simplifies compliance reporting.
Which Frameworks Does ShieldWatch XDR Support for API Security Compliance?
ShieldWatch XDR supports controls commonly required by SOC 2, HIPAA, ISO/IEC 27001, and CMMC 2.0: centralized logging/monitoring, access control tracking, and automated incident response. By capturing structured API telemetry, correlating identity signals, and preserving remediation actions (including SOAR runs), the platform produces auditable artifacts that map to control objectives. Built-in compliance features help teams configure retention, reporting, and evidence bundling so assessors see clear, context-rich artifacts during reviews.
The next section outlines practical steps organizations can adopt using XDR as the enforcement and evidence layer.
How Can Organizations Align API Security Practices with SOC 2, HIPAA, and ISO 27001?
Follow a practical checklist: assign API ownership and access policies, enforce structured logging and retention, run identity-linked access reviews, and codify incident playbooks that include token revocation and containment. Configure XDR to ingest and normalize API telemetry, enable automated evidence collection for key incidents, and schedule regular access and configuration audits that produce artifacts for assessors. Track metrics like access review completion, detection coverage, and time-to-containment to prove control effectiveness. These outputs — logs, alerts, and playbook executions — give auditors verifiable evidence and reduce compliance friction.
Aligning technical controls with documented processes and XDR-enabled evidence turns compliance from episodic work into an ongoing, auditable practice.
What Real-World Use Cases Demonstrate Effective API Security with ShieldWatch XDR?
Real-world examples show how discovery, AI detection, SOAR workflows, and 24/7 SOC oversight stop common API attacks and data loss. Use cases include catching credential stuffing on API endpoints, detecting injection or payload tampering by correlating malformed requests with anomalous downstream access, and halting exfiltration that uses paging to pull large datasets. In each scenario, identity, network, and endpoint signals were joined to produce a high-confidence incident; automated playbooks contained the threat; and analysts validated remediation. These outcomes reduce dwell, protect data, and create clear forensics for compliance.
Summaries below illustrate these patterns without disclosing customer details.
How Has ShieldWatch XDR Prevented OWASP API Top 10 Attacks?
In representative incidents, ShieldWatch XDR detected broken authentication by correlating a surge of failed token validations with unexpected geography and follow-on anomalous API calls. The platform elevated the incident, triggered an automated token revocation playbook, and applied a dynamic rate limit while analysts validated. For injection and parameter-tampering cases, baselined schemas and anomaly scoring flagged malformed payloads; containment included blocking vectors at the gateway and deploying immediate validation patches. These coordinated responses stopped the exploits and produced forensic records for remediation and lessons learned.
These examples show how detection plus orchestrated containment prevents common API vulnerabilities and raises operational maturity.
What Are Examples of Successful API Data Exfiltration Prevention?
Exfiltration via APIs often mimics legitimate pagination or aggregated queries, but behavioral baselines reveal suspicious patterns: many small requests that cumulatively extract large datasets, or odd parameter combinations tied to a single identity. ShieldWatch XDR correlated request cadence with downstream storage access and endpoint activity, then executed a SOAR playbook to throttle sessions and revoke compromised credentials. Analysts reviewed enriched context and applied targeted remediation — access policy changes and token rotation — stopping the exfiltration while keeping services available and preserving an audit trail.
Preventing exfiltration at scale requires high-fidelity signals, sensible automation guards, and analyst oversight to minimize business impact.
The practices and platform mappings in this article equip teams to harden API integrations in XDR. For organizations evaluating enterprise-grade options, ShieldWatch XDR demonstrates how discovery, AI analytics, SOAR orchestration, and managed SOC support combine to reduce alert fatigue, speed containment, and deliver measurable security outcomes. Technical buyers should compare these capabilities to their telemetry maturity, auth models, and compliance needs to prioritize integration work and tool choices.
Frequently Asked Questions
What is the importance of API security in modern applications?
APIs are the primary interfaces for data exchange between services and users, so they’re frequent attack targets. Strong API security protects sensitive data, prevents unauthorized access, and supports regulatory compliance. Securing APIs reduces breach risk, preserves customer trust, and prevents attackers from using APIs to move laterally inside environments.
How can organizations assess their API security posture?
Assess API posture with regular audits, vulnerability scans, and pen tests focused on API endpoints. Review authentication and authorization models, analyze traffic for anomalies, and apply OWASP guidance to identify common weaknesses. Continuous monitoring and structured logging also surface gaps that point to operational and detection improvements.
What role does user education play in API security?
User and developer education matters: training teams to follow secure coding practices, recognize phishing and weak authentication patterns, and adopt robust token management reduces human-driven risk. Informed teams are quicker to spot anomalies and follow incident playbooks, strengthening overall API security.
What are the consequences of poor API security?
Poor API security can lead to data breaches, unauthorized access, regulatory fines, reputational harm, and costly remediation. One exploited API can expose sensitive systems or allow attackers to pivot, creating long-term operational and financial damage.
How can automated tools enhance API security?
Automated tools provide continuous monitoring, real-time detection, and repeatable response actions. They analyze traffic, surface anomalies, and enforce policies at scale, reducing human error and improving response times. When combined with human validation, automation scales protection while preserving accuracy.
What are the best practices for API security management?
Best practices include strong auth and authorization, input validation, encryption in transit and at rest, timely patching, and structured telemetry. Maintain clear access controls, comprehensive logging for audits, and cross-functional processes that align engineering and security on secure API delivery.
Conclusion
APIs are central to modern systems and must be treated as first-class security assets inside XDR. By combining secure design, continuous discovery, structured telemetry, AI-driven detection, and safe SOAR automation — supported by 24/7 SOC coverage where needed — organizations can reduce risk while preserving service continuity. ShieldWatch XDR shows how these elements come together to shorten dwell time, reduce alert fatigue, and produce auditable evidence. If you’re refining API defenses, evaluate telemetry maturity, authentication models, and compliance needs to prioritize the right integrations and controls.




Hi https://is.gd/9PLRLO
Drive sales and watch your affiliate earnings soar!
Join our affiliate community and start earning instantly!
Start profiting from your traffic—sign up today!