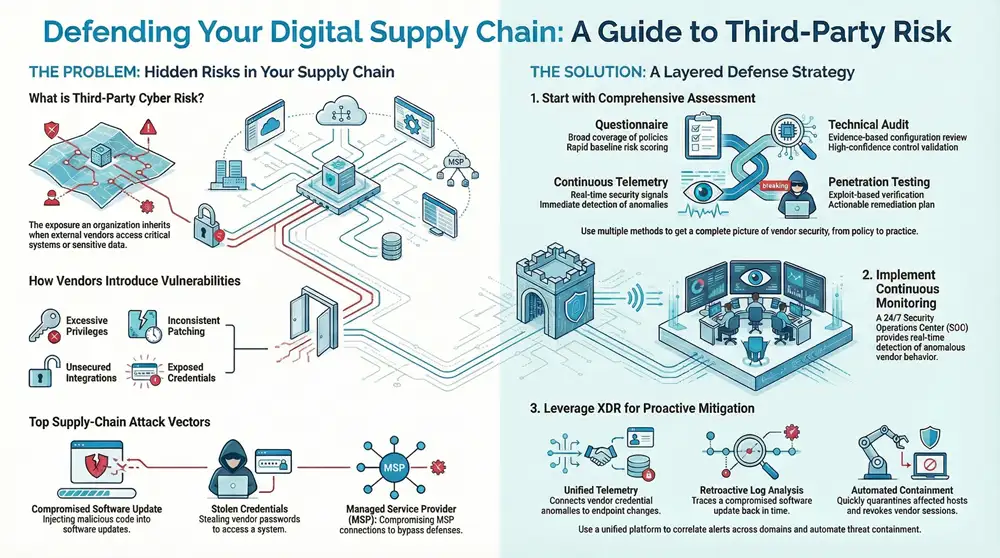
Third‑party cyber risk is the exposure an organization inherits when external suppliers, software vendors, cloud providers or managed service partners touch critical systems or handle sensitive data. Those relationships extend trust and privileges beyond your perimeter — and when a supplier is breached, the financial, operational and regulatory fallout can be significant.
This guide shows how vendor risk programs, continuous telemetry, managed SOC operations and purpose‑built XDR work together to shrink exposure, speed detection and reduce blast radius from third‑party incidents. You’ll get practical assessment techniques, the key signals to prioritize remediation, how 24/7 detection bolsters supply‑chain resilience, and which compliance controls to require from suppliers. We map assessment best practices to operational controls, explain how hybrid AI+human SOC models accelerate containment, and underline why XDR features such as retrospective log analysis and unified telemetry matter for defending against software supply‑chain attacks and credential compromise.
What are third‑party cyber risks and why do they threaten supply‑chain security?
Third‑party cyber risks are gaps and attack paths created when outside entities interact with your systems, data or processes.
They endanger supply‑chain security because vendors often hold privileged access, share integrations or push updates that can carry malicious changes — giving attackers direct routes to pivot into customer environments.
Recognizing these risks is essential to prioritizing controls: every trusted connection and delegated function increases your attack surface. The next section breaks down the common operational mechanisms vendors use to introduce risk and why those mechanisms matter for detection and containment.
How do third‑party vendors introduce cybersecurity vulnerabilities?
Vendors create vulnerabilities through several recurring operational mechanics: excessive privileges, inconsistent patching, unsecured integrations and exposed credentials. Stolen vendor credentials or misconfigured APIs enable lateral movement into downstream systems, and insecure update channels can deliver tampered binaries or dependency‑level backdoors. For example, a supplier with console access to your identity provider or CI/CD pipeline becomes a high‑impact vector if their account is phished or an insider turns malicious. Spotting these mechanics early informs contractual guardrails and technical controls that reduce implicit trust and limit blast radius.
What are common supply‑chain attack vectors targeting third parties?
Attackers often exploit software update processes, stolen vendor credentials, compromised managed‑service connections and dependency/package poisoning in build pipelines. Update tampering is especially damaging because signed releases propagate broadly; credential theft succeeds because many vendors use long‑lived keys or service accounts; and compromised MSPs can alter monitoring or backups to conceal intrusions. Focusing on the highest‑priority vectors — software updates, credential compromise and MSP/network abuse — lets defenders tailor detection rules and vendor requirements to close the most commonly exploited gaps.
How does vendor security assessment strengthen supply‑chain cybersecurity?
A strong vendor assessment program finds control gaps, measures exposure and drives contractual and technical remediation. The most effective programs combine questionnaires, on‑site or virtual audits, penetration testing and telemetry‑led continuous assessment — moving from point‑in‑time assertions to persistent validation. Assessments translate findings into required controls, SLA clauses and remediation timelines so procurement and security teams can prioritize vendors by risk and enforce mitigations before granting access.
- Questionnaires deliver a fast, standardized snapshot of vendor controls and policies.
- Technical audits validate configurations, patching and architecture through collected evidence.
- Telemetry‑based continuous assessment monitors logs and signals to detect drift or compromise.
- Penetration testing surfaces exploitable weaknesses and produces a technical remediation roadmap.
Those modalities form a layered verification strategy that balances coverage, cost and cadence. Knowing how each mode contributes helps you choose the right assessment mix based on vendor criticality and enterprise risk appetite.
Below is a concise comparison of common assessment approaches and their operational characteristics.
The table illustrates that telemetry‑led assessment provides ongoing detection while questionnaires are snapshots, and that audits deliver higher assurance for critical suppliers. Together they cover complementary assurance dimensions.
Integration opportunity: ShieldWatch XDR aligns with many telemetry and automation needs described here. ShieldWatch XDR unifies endpoint, network, cloud and identity telemetry for continuous vendor scoring, supports retroactive 90‑day log analysis for investigation, and automates evidence collection to feed risk scoring and contractual controls. Paired with procurement gating and remediation SLAs, a telemetry‑first platform like ShieldWatch XDR narrows the gap between assertions and observable behavior.
What are best practices for conducting comprehensive vendor risk assessments?
Start with classification and scoping: identify which suppliers touch sensitive resources or critical functions and tier them by potential impact. Follow with evidence‑driven verification — request logs, configuration snapshots and attestations, and perform technical scans or audits where risk warrants deeper review. Embed scoring and remediation tracking into procurement workflows so vulnerabilities trigger remediation milestones and contractual consequences when needed. Prioritize effort: give high‑blast‑radius suppliers continuous telemetry and frequent audits, while lower‑risk vendors can be managed with periodic questionnaires and sampled validation.
How can continuous monitoring enhance vendor security posture?
Continuous monitoring streams telemetry — endpoint signals, network flows, cloud IAM events and application logs — into detection systems, enabling near‑real‑time alerts on anomalous vendor behavior. Behavioral baselining reduces false positives by establishing normal vendor patterns; alert thresholds tied to vendor criticality enforce appropriate SLAs for investigation. Practically, continuous feeds must integrate with SOC workflows to escalate events, trigger automated containment or produce compliance evidence. When monitoring is mapped to remediation playbooks, organizations detect vendor‑originating incidents earlier and limit propagation.
What role does a managed SOC play in detecting and responding to third‑party threats?
A managed Security Operations Center (SOC) augments internal teams with continuous monitoring, threat hunting and incident response expertise focused on third‑party threats. Managed SOCs fill staffing and shift gaps, maintain detection content for common supply‑chain vectors, and coordinate cross‑team response when a vendor compromise impacts downstream systems.
This capability is especially valuable for supply chains because vendor incidents often unfold across time zones and require correlated telemetry to connect vendor activity to enterprise impact. The sections that follow cover the benefits of 24/7 detection and hybrid AI+human operations.
How does 24/7 security operations improve supply‑chain threat detection?
Round‑the‑clock SOC coverage ensures vendor‑originating anomalies are seen and acted upon regardless of when they occur, reducing time‑to‑detect and time‑to‑contain for off‑hours events. Dedicated hunting teams look for subtle indicators across telemetry that may signal vendor credential misuse or lateral movement, and analyst rotations preserve investigation continuity.
Typical scenario: an off‑hours vendor update triggers unusual process behavior that a 24/7 SOC detects and isolates before batch systems process corrupted files. That continuous posture shortens dwell time and prevents small vendor faults from turning into enterprise outages.
What are the benefits of combining AI with a human‑led SOC for incident response?
A hybrid AI+human SOC uses AI for triage, enrichment and prioritization while skilled analysts validate, simulate adversary behavior and make complex decisions. AI reduces false positives and elevates high‑confidence incidents so analysts can focus on containment and root‑cause work. For example, AI can correlate a vendor’s anomalous API calls across identity and network telemetry, score the event and suggest containment steps while analysts handle escalation and vendor coordination. The result: lower MTTR, higher signal‑to‑noise and defensible automated containment governed by human thresholds.
How can XDR platforms be leveraged for proactive supply‑chain threat mitigation?
Extended Detection and Response (XDR) platforms ingest telemetry from endpoints, network, cloud and identity to correlate events and automate containment — enabling proactive mitigation of third‑party threats before they escalate. XDR spots cross‑domain patterns — for example, a vendor account copying files to cloud storage after a patch — and runs playbooks to isolate affected assets. Capabilities like retrospective log analysis, cross‑domain correlation and automated policy enforcement are particularly effective against software supply‑chain and MSP‑originated compromises. The comparisons below show how common XDR features map to supply‑chain use cases.
- Unified telemetry links vendor identity activity to endpoint and cloud anomalies.
- Retroactive log analysis reconstructs timelines after a suspicious vendor event.
- Automated containment enforces least privilege and isolates compromised sessions quickly.
These use cases demonstrate why XDR is central to reducing blast radius and delivering validated response across integrated telemetry sources.
This practical comparison highlights that retrospective analysis and unified telemetry are the features most directly tied to supply‑chain detection and containment.
Integration note: ShieldWatch XDR demonstrates these capabilities by pairing AI‑driven correlation with 90‑day retroactive log analysis and automated containment. Its unified view across endpoints, network, cloud and identity supplies continuous vendor telemetry that accelerates investigations and supports compliance evidence, while AI reduces alert fatigue so analysts can act on verified threats.
What are the key XDR features for unified third‑party risk management?
Essential XDR features for third‑party risk include cross‑domain correlation (identity, endpoint, network, cloud), retrospective analysis to rebuild vendor timelines, behavioral analytics that flag deviations from vendor baselines, and automated policy‑driven containment. These capabilities let security teams join a vendor’s anomalous API calls to suspicious process executions and IAM changes, producing a coherent incident narrative for faster remediation. XDR outputs can feed vendor scoring, SLA enforcement and targeted audits.
How does AI‑powered automation reduce alert fatigue and speed response?
AI‑powered automation triages noisy signals into prioritized, context‑rich incidents and enriches alerts with correlated telemetry and suggested playbooks. Scoring models rank incidents by likely impact and recommended containment steps; automated playbooks can execute safe, reversible actions — like isolating a host or revoking tokens — under analyst gates. Offloading repetitive adjudication to AI lets analysts focus on high‑complexity decisions, improving throughput and lowering mean time to remediation without sacrificing oversight. Governance and guardrails ensure automation runs only within predefined boundaries and escalates ambiguous cases to humans.
Which compliance frameworks matter for vendor security and supply‑chain protection?
Compliance frameworks set baseline expectations for vendor controls, reporting and breach notification, and they matter for contractual security across regulated industries. SOC 2 focuses on control environments and monitoring for service providers; HIPAA governs safeguards for protected health information; and CMMC 2.0 defines maturity requirements for defense suppliers. Mapping vendor obligations to the right frameworks clarifies required controls such as encryption, access management, logging and notification timelines. The sections below outline vendor requirements and practical continuous‑monitoring strategies to stay audit‑ready.
How do SOC 2, HIPAA and CMMC 2.0 affect third‑party risk management?
SOC 2 asks service providers to demonstrate effective controls, ongoing monitoring and evidence of operation — which enterprises should validate via reports and telemetry. HIPAA requires vendors protecting PHI to implement encryption, strict access controls and timely breach notifications; covered entities must ensure Business Associate Agreements include technical and reporting obligations. CMMC 2.0 pushes defense suppliers to prove security maturity across levels, prompting primes to enforce baseline hygiene and incident response capabilities in their supply chain. Requiring attestations, audit reports and telemetry access ensures vendors meet these expectations.
What are effective strategies for continuous compliance monitoring?
Continuous compliance monitoring combines automated evidence collection, control baselines mapped to framework requirements and audit‑ready reporting. Automation captures encryption status, access reviews, patch state and anomalous access events and converts them into control metrics for SOC 2 or CMMC evidence. Scheduled validation, drift detection alerts and sampled audits reduce surprises during formal assessments. Mapping telemetry directly to control objectives ensures monitoring produces actionable audit artifacts rather than isolated alerts.
What are best practices for building a resilient vendor cybersecurity program?
Resilient vendor programs rely on governance, clear lifecycle policies, continuous monitoring, prioritized remediation and practiced incident collaboration with suppliers. Governance should define classification, SLAs and escalation paths; lifecycle processes must cover onboarding, periodic reassessment and offboarding; operational resilience calls for playbooks, tabletop exercises with vendors and contingency plans for supplier outages. Prioritize resources on vendors with large blast radius or access to critical data so limited budgets deliver maximum risk reduction. The following sections outline zero‑trust steps and a practical method to rank vendors by likely impact.
How to implement zero‑trust principles in supply‑chain security?
Applying zero trust to third parties means enforcing least privilege, microsegmentation, short‑lived credentials and continuous verification for vendor access. Practical steps include replacing standing service accounts with ephemeral tokens, applying conditional access and device posture checks, and segmenting vendor traffic into constrained zones with strict ingress/egress policies. Continuous identity verification — re‑authentication and risk‑based prompts — narrows the window for credential abuse. These controls reduce implicit trust and make vendor activity observable and revocable.
How to prioritize risks based on vendor “blast radius” and business impact?
Prioritize vendors by combining business impact (data criticality, process dependency) with technical exposure (privileges, network reach, shared credentials) to calculate a composite risk score. A simple model — Risk = Likelihood × Impact — works well, where Impact includes regulatory exposure, revenue implications and recovery complexity. Operationalize scores into SLAs and remediation tiers so high‑blast‑radius suppliers receive continuous monitoring, frequent audits and stronger contractual controls while low‑risk vendors get lighter oversight. Require telemetry access and the ability to revoke or constrain vendor sessions when scores cross thresholds.
For organizations ready to operationalize these approaches, adopting unified telemetry, continuous assessment and hybrid AI+human SOC workflows shortens detection windows and reduces alert fatigue. ShieldWatch delivers an enterprise‑grade XDR with 24/7 managed SOC capabilities that align with these practices — unifying endpoint, network, cloud and identity telemetry, providing retroactive 90‑day log analysis, AI‑assisted triage that lowers false positives and fast containment workflows. Requesting a demo or talking with an expert will clarify how these capabilities map to your vendor prioritization and compliance goals while keeping blast radius and regulatory risk under control.
Frequently asked questions
What steps can organizations take to mitigate third‑party cyber risks?
Build a formal vendor risk management program: assess suppliers, bake security requirements into contracts, and continuously monitor vendor activity. Prioritize vendors by business impact, enforce least‑privilege access, and require compliance evidence. Regular training for internal teams and vendors helps everyone spot and respond to threats faster.
How often should vendor risk assessments be conducted?
Assessment frequency should match vendor criticality. High‑risk suppliers may need assessments semiannually; lower‑risk vendors can be reviewed annually. Continuous monitoring should complement periodic assessments and any material change — such as a merger, new service or infrastructure change — should trigger a reassessment.
What role does employee training play in supply‑chain security?
Training is essential. Regular, role‑based training helps staff recognize phishing, enforce secure vendor relationships and follow data‑protection practices. A security‑aware workforce reduces human error — a common factor in successful attacks — and supports more resilient vendor collaboration.
How can organizations ensure compliance with security frameworks?
Embed compliance into vendor management: require attestations and reports, automate evidence collection, and maintain audit‑ready dashboards. Communicate expectations clearly to vendors, provide guidance on controls, and update compliance plans as frameworks evolve to stay audit‑ready.
What are the benefits of using AI in vendor risk management?
AI helps by automatically analyzing large data sets, surfacing patterns and flagging anomalies that indicate risk. It prioritizes alerts to reduce fatigue, enables continuous monitoring and provides real‑time insights into vendor behavior — allowing faster, better‑informed decisions about vendor relationships and remediation.
What should organizations do if a vendor is compromised?
Execute your incident response plan: isolate affected systems, assess impact, and coordinate with the vendor to understand scope. Notify stakeholders and regulators as required, then conduct a post‑incident review to strengthen controls and adjust the vendor relationship where needed.
Conclusion
Stopping third‑party risk requires disciplined vendor risk management, continuous telemetry and an XDR‑backed response model supported by a 24/7 SOC. Prioritize assessments, enforce contractual controls and use AI‑assisted workflows to reduce noise and accelerate containment. Taken together, these steps strengthen supply‑chain resilience, protect sensitive data and keep you audit‑ready. Learn how ShieldWatch’s platform and managed SOC can help you operationalize these practices and lower your vendor blast radius.




https://shorturl.fm/3XIDT
https://shorturl.fm/wu2RD
https://shorturl.fm/zxHEl
https://shorturl.fm/S0235
Start profiting from your traffic—sign up today!
Monetize your traffic with our affiliate program—sign up now!
Partner with us for high-paying affiliate deals—join now!
Share your link and rake in rewards—join our affiliate team!
Share your unique link and earn up to 40% commission!