Extended detection and response (XDR) unifies telemetry from endpoints, networks, cloud workloads, and identity systems so teams can detect, investigate, and remediate complex threats faster. As attacks grow more sophisticated, cloud footprints expand, and security tools multiply, XDR cuts through blind spots, speeds response, and preserves continuous evidence for compliance. This article lays out why mid-market and enterprise organizations should adopt XDR now: holistic visibility across the attack surface, AI-driven detection and automated response, continuous SOC coverage, operational simplicity that lowers total cost of ownership, and built-in compliance support.
You’ll find practical comparisons to EDR and SIEM, an explanation of how automation and SOAR reduce alert fatigue, ways managed SOC models extend internal teams, and clear mappings to major compliance frameworks. The sections that follow break down core concepts, operational impacts, and vendor capabilities you should prioritize when evaluating enterprise XDR solutions.
What Is XDR and Why Is It Crucial for Modern Enterprises?
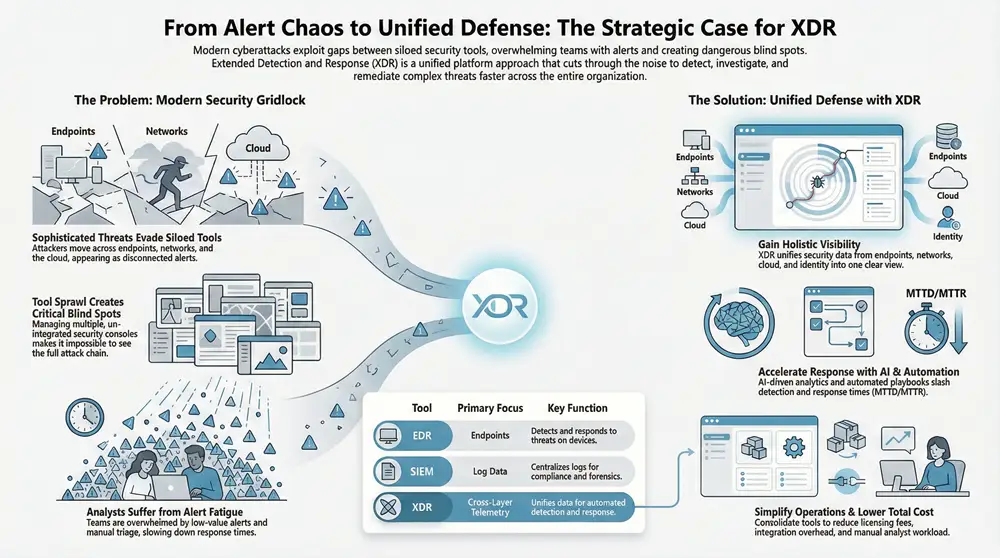
XDR is a cross-layer detection and response platform that collects and correlates telemetry from endpoints, network traffic, cloud services, and identity systems to deliver context-rich alerts and automated response options. By combining cross-layer correlation, behavioral analytics, and orchestration, XDR shortens dwell time and presents a unified incident narrative that speeds accurate remediation. For enterprises, that means clearer situational awareness and coordinated containment that limits lateral movement and reduces business risk. Shifting from segmented point products to an XDR approach moves security from reactive triage to proactive detection and coordinated response—critical for defending against multi-stage campaigns and cloud-native threats.
By aggregating diverse telemetry sources, XDR reconstructs attack chains and produces consolidated investigations that give analysts meaningful context. That linkage closes the gap between endpoint detection and network monitoring and ties identity signals to suspicious behavior to lower false positives. The next subsection explains how this holistic visibility emerges from combined data sources and why it matters for spotting multi-stage intrusions.
How Does XDR Provide Holistic Visibility Across Your Attack Surface?
XDR delivers holistic visibility by ingesting endpoint telemetry, network flows, cloud logs, and identity events, then correlating those signals into linked incidents for analysts to investigate. By fusing these key telemetry sources—endpoint, network, cloud, and identity—XDR reveals multi-stage attacks that would otherwise look like isolated alerts across separate tools. For example, a lateral-movement sequence that starts with a phishing link becomes visible when cloud-access anomalies and elevated identity risk scores are joined into a single incident timeline.
That cross-layer context reduces mean time to detect and mean time to respond because analysts work from a coherent narrative instead of disconnected alerts. In short, holistic visibility turns noisy telemetry into actionable investigations that feed automated and human-assisted remediation workflows.
What Makes XDR Different from EDR and SIEM Solutions?
XDR differs from EDR and SIEM in scope, automation, and operational focus. EDR concentrates on endpoint telemetry and endpoint-first response, while SIEM centralizes logs for compliance-oriented correlation and forensic searching. XDR sits above these tools as a cross-layer detection and response platform that emphasizes automated correlation, enriched context, and guided remediation. Unlike a log-centric SIEM that often needs heavy rule tuning and manual analyst effort, XDR applies behavioral analytics and orchestration to speed verdicting and containment. In practice, XDR complements existing EDR and SIEM investments—ingesting endpoint telemetry from EDR, forwarding prioritized incidents to SIEM for retention, and orchestrating SOAR playbooks for containment—so organizations retain value from point solutions while gaining unified operational efficiency.
When evaluating XDR, prioritize solutions that offer cloud-native telemetry ingestion, broad agent coverage, and native orchestration—these determine how effectively XDR reduces investigative overhead and accelerates remediation.
The next paragraph introduces an enterprise-grade example that shows how vendors put these capabilities into production.
ShieldWatch XDR is one practical example of an enterprise-grade platform that unifies telemetry, automation, and expert monitoring. ShieldWatch provides XDR, EDR, SOC, and managed detection and response services for mid-market and enterprise organizations, illustrating how integrated telemetry and orchestration produce measurable operational outcomes. The rest of this article mixes conceptual guidance with real-world metrics to explain the five reasons to adopt XDR, using ShieldWatch as an occasional, illustrative vendor example.
How Does Automated AI-Driven Threat Detection and Response Benefit Your Business?
XDR’s AI-driven detection and response layers machine learning, behavioral analytics, and orchestration to surface high-confidence alerts and execute containment steps with minimal manual effort. This reduces false positives, shortens verdict times, and standardizes response so security teams can spend more time on complex investigations and less on repetitive triage. The primary business outcomes are lower mean time to detect (MTTD) and mean time to respond (MTTR), reduced analyst workload, and a measurable drop in alert volume that improves SOC efficiency. Properly implemented, AI-driven XDR becomes a force multiplier—turning raw telemetry into prioritized incidents with automated enrichment and remediation options.
Typical impacts of automation and orchestration include:
- Faster verdicting: Automated analytics accelerate suspicious-activity classification and cut manual triage time.
- Fewer false positives: Behavioral models plus contextual signals filter noise and surface correlated, high-confidence incidents.
- Automated containment: Orchestrated response actions limit lateral movement and reduce data-loss windows.
These benefits translate into measurable outcomes you should compare when assessing vendors. The next subsection explains AI agent hyperautomation and how it operationalizes rapid incident response.
What Role Does AI Agent Hyperautomation Play in Rapid Incident Response?
AI agent hyperautomation describes autonomous software agents that handle triage, enrichment, and routine decisioning tasks traditionally performed by analysts—acting as digital security assistants. These agents run repeatable logic—confirming IOC matches, correlating telemetry, and recommending or executing containment—so human analysts focus on complex judgment calls. The result: standardized playbooks, consistent verdicting, and faster containment cycles that reduce dwell time and business impact. For example, automated workflows can classify and contain common ransomware indicators while escalating complex or ambiguous behaviors to human analysts for deeper investigation.
This automation works hand-in-hand with SOAR, which provides the structured playbooks agents execute to ensure repeatability and auditability across incidents.
Before the following list, concrete metrics from enterprise providers help quantify automation benefits in reduced alert volumes and time-to-containment.
To illustrate measurable outcomes from combined AI and orchestration, ShieldWatch reports average verdict times under 10 seconds and containment actions executed within minutes—backed by AI agent hyperautomation, 24/7 SOC oversight, and more than 150 pre-built SOAR workflows. That mix of autonomous decisioning and expert supervision shows how vendor capabilities translate into speed and consistency.
How Do SOAR Workflows Reduce Alert Fatigue and Streamline Security Operations?
SOAR workflows automate repetitive tasks—enrichment, ticket creation, containment commands, and notifications—so analysts receive fewer, better-prepared alerts. Pre-built playbooks codify response procedures for common scenarios like phishing, malware, and credential compromise, shortening time to value and ensuring consistent remediation. SOAR reduces alert volume by aggregating related signals, enriching them with threat intelligence, and resolving routine incidents automatically while escalating genuine threats. The result is less alert fatigue and more time for proactive hunting and high-value investigations.
- Common SOAR playbooks include containment of compromised endpoints, automated phishing triage, and identity-based access revocation.
- Operational impact often shows large drops in repetitive analyst tasks and measurable MTTR improvements.
- Value proposition is speed plus repeatability—helping audits capture consistent remediation evidence.
The short table below maps key automation components to the outcomes they drive in detection and response.
The table below shows how core automation elements contribute to operational metrics and improved security outcomes.
Combining AI agents, SOAR, and threat intelligence yields quantifiable improvements in detection and response that lower risk and reduce operational burden. The next major section explains why continuous human-led monitoring remains essential even with strong automation.
Why Is 24/7 Expert SOC Monitoring Essential for Continuous Protection?
24/7 expert SOC monitoring ensures automated systems are backed by human analysts who validate alerts, hunt proactively, and make nuanced decisions during complex incidents. Automation speeds up routine detection and containment, but human-led processes uncover stealthy, low-and-slow campaigns and assess business impact for prioritized remediation. Round-the-clock monitoring shrinks the risk window outside business hours and guarantees escalations and containment happen without delay—vital for global operations. Pairing machine speed with human judgment improves detection coverage and creates more defensible incident handling for compliance and governance.
Humans also enable continuous improvement: analysts refine detection rules, tune models, and author playbooks from incident learnings and adversary behavior. That iterative cycle raises alert fidelity over time and cuts recurring false positives. The next subsection details how threat hunting complements automated detection in a modern XDR deployment.
How Does Human-Led Threat Hunting Complement AI in ShieldWatch XDR?
Human threat hunters take a hypothesis-driven approach to spot adversary behaviors automated systems may miss. They use the correlated telemetry XDR delivers—endpoint artifacts, network flows, cloud access patterns, and identity anomalies—to develop complex hypotheses and trace campaign indicators across environments. This proactive work uncovers low-and-slow intrusions and new TTPs (tactics, techniques, and procedures) that need bespoke remediation. Human insight validates AI findings, fills detection gaps, and refines models for future automation improvements.
In ShieldWatch XDR deployments, autonomous detections are paired with expert analysts who run continuous threat hunting and refine playbooks so AI-driven actions align with organizational priorities and compliance needs.
What Are the Benefits of Managed SOC Services for Your Security Team?
Managed SOC services give organizations expert monitoring, incident response, and threat intelligence without the cost and complexity of building a full in-house SOC. For many mid-market companies and MSPs, managed SOC delivers predictable operating costs, scalable coverage, and access to detection engineering and hunting expertise that would be expensive to hire internally. Managed SOC teams handle 24/7 triage, playbook-driven containment, and escalation, letting internal staff focus on business priorities rather than routine monitoring. This model is especially valuable for organizations facing a cybersecurity skills shortage or limited budgets for specialist hires.
- Key benefits include continuous coverage, access to specialized analysts, and faster time to detect and contain.
- Operational advantage comes from consistent playbook execution and ongoing tuning of detections.
- Scalability lets organizations change monitoring and response levels without prolonged hiring cycles.
ShieldWatch combines managed SOC services with its XDR platform, pairing AI automation and expert analysts to deliver continuous coverage and reduce the load on internal security teams—making advanced detection and remediation accessible even without a mature SOC.
The next section covers how XDR reduces operational complexity and lowers total cost of ownership through consolidation and process simplification.
How Does XDR Simplify Security Operations and Reduce Total Cost of Ownership?
XDR simplifies operations and lowers total cost of ownership by consolidating multiple point solutions into a unified platform, cutting alert volume, and shortening MTTR through automation. Consolidation reduces integration overhead and licensing complexity and lowers the number of failure points where gaps can appear. Fewer tools mean fewer consoles to monitor, unified investigations, and streamlined playbooks that speed analyst onboarding and boost productivity. TCO improvements come from reduced staffing needs for routine triage, smaller incident impact, and eliminating overlapping features that add cost without meaningful security value.
To illustrate consolidation impacts, the table below compares outcomes from a consolidated XDR approach versus a heterogeneous collection of point solutions.
That comparison shows how moving to XDR reduces maintenance and operational costs while improving security through cohesive detection and response. The list below highlights specific operational gains organizations typically see after adopting XDR.
- Reduced tool sprawl: Centralized investigations cut time spent switching contexts.
- Lower MTTR: Integrated responses and automation accelerate containment.
- Improved analyst efficiency: Enriched, correlated incidents speed investigations.
Those efficiencies also help address the cybersecurity skills gap by letting analysts focus on investigations and threat hunting instead of repetitive triage, which we cover in the next subsection.
In What Ways Does XDR Address the Cybersecurity Skills Gap?
XDR helps close the skills gap by automating routine work, offering guided investigations, and enabling managed services that supply specialist analysts when needed. Automation shrinks low-value alert volume and handles standardized containment steps, so junior analysts ramp faster and senior analysts concentrate on complex hunting and remediation. Standardized playbooks and enriched incident context shorten training time and produce consistent, auditable responses. Managed XDR or XDR-as-a-Service models also supplement internal teams with niche skills, providing an operational bridge while organizations build in-house capabilities.
That role shift—from constant triage to higher-order investigation—improves retention, accelerates analyst development, and reduces the pressure to hire rare specialists for routine monitoring tasks.
How Does Consolidating Security Tools with XDR Lower Business Risks?
Consolidating tools under XDR lowers business risk by shrinking integration points, closing visibility gaps, and simplifying governance and incident playbooks. Fewer integrations mean less chance of telemetry loss or configuration drift that attackers exploit, while unified incident timelines shorten dwell time by making lateral movement visible. Clear, documented governance ensures response procedures are consistent and auditable, lowering the risk of incomplete remediation that leaves systems exposed. In short, fewer moving parts and clearer incident handling result in a smaller attack surface and faster, more reliable recovery.
That risk reduction completes the operational case for XDR and leads into how XDR supports compliance and audit readiness, the focus of the next section.
How Does ShieldWatch XDR Support Compliance and Robust Risk Management?
ShieldWatch XDR helps compliance and risk management by continuously collecting telemetry, retaining evidence automatically, and using playbook-based remediation mapped to common control objectives. Continuous logging and searchable telemetry create an auditable trail for investigations and control verification, while standardized remediation workflows record actions auditors can review. These features shorten audit prep time, simplify evidence retrieval, and let security teams demonstrate control effectiveness through repeatable processes. They also support risk management by improving detection and reducing dwell time, which lowers the likelihood and impact of compliance incidents.
The table below maps common compliance frameworks to ShieldWatch features and the compliance benefits they deliver.
This mapping makes it clear how ShieldWatch features support control objectives across frameworks and assist teams during audits with searchable evidence and documented response steps. The next subsection lists the frameworks ShieldWatch explicitly supports and explains how specific features help meet each requirement.
Which Compliance Frameworks Does ShieldWatch XDR Facilitate?
ShieldWatch XDR supports frameworks such as SOC 2, HIPAA, CMMC 2.0, and ISO 27001 through capabilities that address logging, retention, access monitoring, and incident documentation. For SOC 2, continuous monitoring and detailed incident timelines provide the logs auditors expect for monitoring and incident-response controls. For HIPAA, endpoint and identity monitoring surface potential ePHI access anomalies and demonstrate protection and timely response. For CMMC 2.0 and ISO 27001, centralized correlation, policy enforcement, and documented remediation playbooks support evidence collection and control validation. These capabilities help teams align detection and response controls with compliance needs and reduce manual work during audits.
With those frameworks covered, the final subsection explains how XDR supports audit preparation and continuous compliance monitoring in practical terms.
How Does XDR Aid in Audit Preparation and Continuous Compliance Monitoring?
XDR helps audit prep by automating evidence collection, centralizing searchable telemetry, and enforcing retention policies that match compliance requirements—cutting the time auditors and security teams spend gathering logs. Automated reporting and playbook-driven remediation create documented incident trails that show controls worked and actions were taken promptly. Continuous compliance monitoring alerts on deviations from expected control behavior—abnormal access, failed integrity checks—and triggers remediation playbooks to restore compliance. The combined effect is faster auditor responses, less manual evidence assembly, and stronger assurance that controls are operating as intended.
Organizations adopting XDR should align retention policies, playbook documentation, and reporting templates to their audit requirements to maximize compliance value and reduce ad hoc evidence requests during assessments.
This completes the five reasons to adopt XDR now: holistic visibility, AI-driven detection and automated response, continuous human and managed SOC coverage, operational simplification that reduces TCO, and compliance-enabling capabilities that support audit readiness and risk management.
Frequently Asked Questions
What types of organizations can benefit from adopting XDR?
XDR is especially valuable for mid-market and enterprise organizations with complex environments—on-prem, cloud, or hybrid—and diverse assets to protect. These organizations gain holistic visibility, streamlined operations, and improved incident response. Teams with limited cybersecurity staff or expertise can also use XDR (and managed services) to raise their security posture without fully staffing a large SOC.
How does XDR enhance incident response times compared to traditional methods?
XDR speeds incident response by automating detection and correlating signals from multiple telemetry sources, which reduces mean time to detect (MTTD) and mean time to respond (MTTR). Traditional, siloed workflows often rely on manual investigation and slow tool handoffs. XDR provides a unified incident view so teams can assess and act faster, limiting damage and operational disruption.
Can XDR integrate with existing security tools and systems?
Yes—XDR is designed to integrate with existing tools like EDR and SIEM. It ingests telemetry, correlates data, and enriches incidents so organizations keep their current investments while gaining cross-layer detection and automated response. That allows teams to maintain established workflows while benefiting from XDR’s orchestration and guided remediation.
What role does threat intelligence play in XDR?
Threat intelligence enriches XDR telemetry, adding context that helps prioritize alerts and reduce false positives. Up-to-date intelligence improves detection accuracy and enables automated response actions based on known bad indicators, helping teams react faster to emerging threats and vulnerabilities.
How does XDR support compliance with regulatory frameworks?
XDR supports compliance by continuously collecting telemetry, retaining evidence automatically, and recording standardized remediation steps. Those features simplify audits—SOC 2, HIPAA, ISO 27001, and others—by producing searchable logs and documented incident timelines auditors can review, reducing the manual burden of compliance management.
What are the cost implications of implementing XDR?
While implementing XDR involves upfront investment, it typically reduces long-term costs by consolidating tools, lowering licensing and integration expenses, and reducing the staffing needed for routine triage. Automation and managed SOC options further cut TCO while enabling security teams to focus on higher-value work.
Conclusion
Adopting XDR strengthens your security posture by delivering unified visibility, automated threat detection, and faster incident response. That integrated approach reduces operational complexity and supports compliance with key frameworks—helping your organization stay secure and audit-ready. By combining AI-driven automation with managed SOC services, you can optimize security operations and control costs. Learn how ShieldWatch XDR can help you implement a practical, measurable XDR strategy today.




Fast indexing of website pages and backlinks on Google https://is.gd/r7kPlC
Drive sales and watch your affiliate earnings soar!
Join our affiliate program and start earning commissions today—sign up now!
Drive sales, earn commissions—apply now!